Two weeks ago, I thought it was a mistake to prioritize daily fires over long-term strategic planning. But blog posts are ephemeral (like AI agents) and a conversation with Google Gemini made me realize I had it backward.
Before, sprinkler systems outranked firefighting
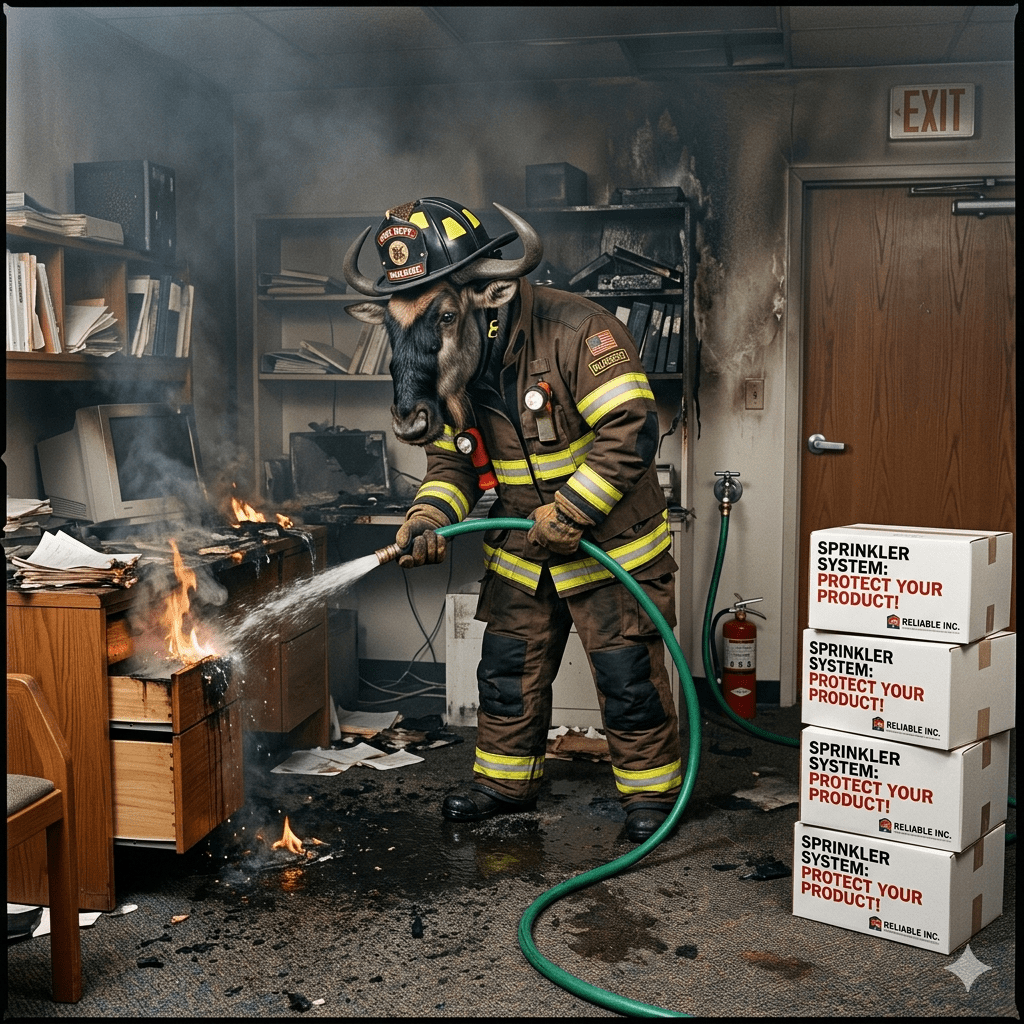
On May 12 I wrote a post entitled “Is Your Identity/Biometric Firm Too Busy Putting Out Fires to Install a Sprinkler System?” Its thesis:
“Your identity/biometric firm needs experienced product marketing contract help because you are drowning in work. But because you’re drowning in work you can’t take the time to set up that contract.”
I won’t get into the resolution of the post, but note the inherent value judgment contained within the content.
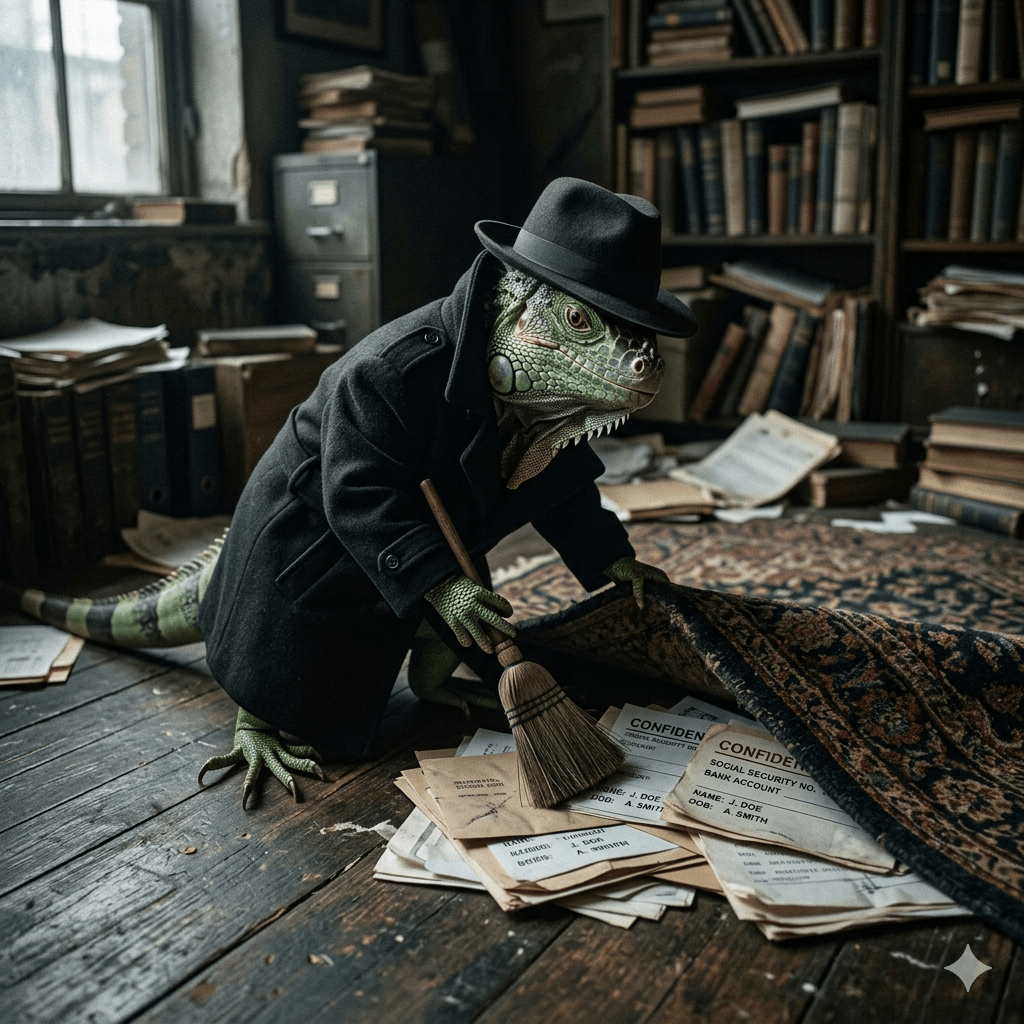
- Manually putting out fires (NEVER with gasoline) is reactive, displays a lack of planning, and is therefore denigrated.
- Installing a sprinkler system is proactive, displays a bias toward strategic long-term planning, and is therefore elevated.
So if the prospect takes the time to sign that contract with Bredemarket, I will ensure that the process is as frictionless as possible. I already know the identity/biometric terminology, and Bredemarket’s “seven questions” process removes the need for you to develop a briefing book for me.
Nice and stable, like installing a sprinkler system.
Something that a sage would write.
Let’s look at it again
But then I began asking questions—in this case, with Google Gemini. Not with the distinctive Bredebot persona, but with Gemini’s natural voice. And as I engaged in a messaging and positioning dialogue, Gemini hit me between the eyes with this observation.
“[Bredehoft] notes that many biometric firms are “too busy putting out fires to install a sprinkler system.”
“The “Fire” is an immediate, looming RFP deadline….A consultant like Bredehoft is brought in as an emergency firefighter to secure that short-term win.
“The “Sprinkler System” is long-term product marketing (building consistent messaging, positioning products, and writing educational white papers)….
“[C]onsulting clients are notoriously reactive. They are far more likely to open their wallets for immediate help with an active proposal than for long-term strategic brand-building.”
Then it hit me.
The firefighter is the GOOD guy.

After, firefighting outranks sprinkler systems
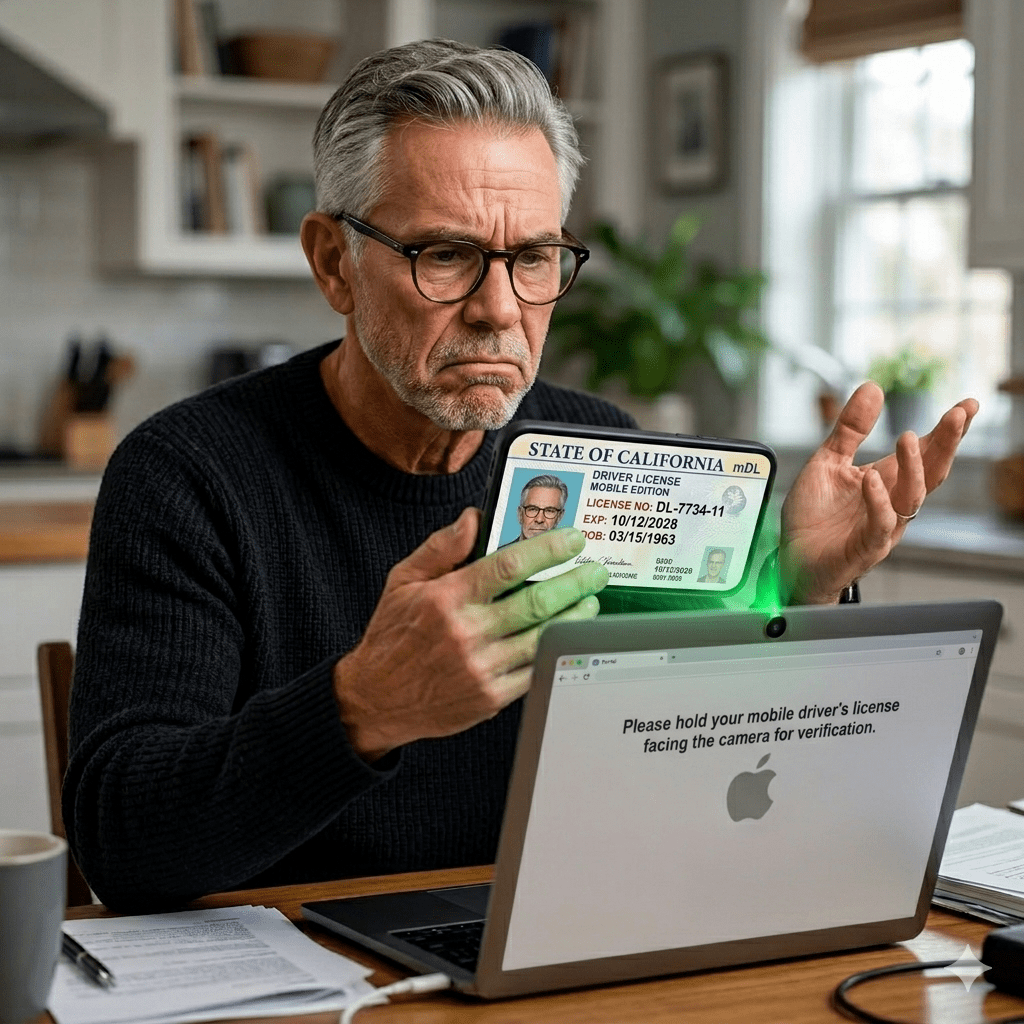
Prospects call in a consultant because they want something yesterday and, as my home page phrases it, “don’t have the time to craft their own content.”
And not just proposal content with money on the line as Gemini explained. Maybe the prospects need a blog post right now; no immediate contract, but invaluable positioning. Or maybe they even need an emergency analysis. (Hey, it could happen.)
When you’re in the middle of a fire, you don’t have time to train a rookie. I already know the identity world, so we can get straight to bailing out your firm.
I will fight your fire, and then maybe later on we can discuss more strategic topics.
But first we need that pesky contract, or the equivalent. (“John, we’ll pay you $500 net 15 for that blog post.”)
But first let’s put out the fire. Contact Bredemarket today to get it done.
And here is a postscript for the kids who don’t know why I was talking about gasoline earlier.
Or why right now.