In many cases, identity fraud is accomplished by a bad actor impersonating the identity of another person. Many people have found unauthorized credit or debit card transactions that they didn’t perform, and have had to shut down and re-open their cards as a result.
However, there are other cases in which the identity fraud is accomplished by inventing a “person” out of whole cloth. Or partial cloth; a real piece of identity, such as a legitimate U.S. social security number, is combined with fake information, such as non-existent addresses, stock photography headshots, and unverified social media accounts.
The process could be less rigorous, such as creating a Twitter bot to inflate followers (no government ID needed), or it could be more rigorous, in which the synthetic identity gains legitimate credentials such as passports (although this is becoming more difficult as facial recognition compares applicant faces to existing faces).
Synthetic identity fraud can be damaging. Henry Engler of Thomson Reuters (not Thomas Reuters) cites a figure of $6 billion in losses to U.S. lenders from synthetic identity fraud.
But sometimes the fraud, while still fraudulent, is relatively innocuous.
Take the case of a particular web design company in North Hollywood, California. If you visit its website (which, oddly enough, is on the “org” domain), the only listed contact for the company is a guy named Eric.
It’s a whole different story on LinkedIn, however.
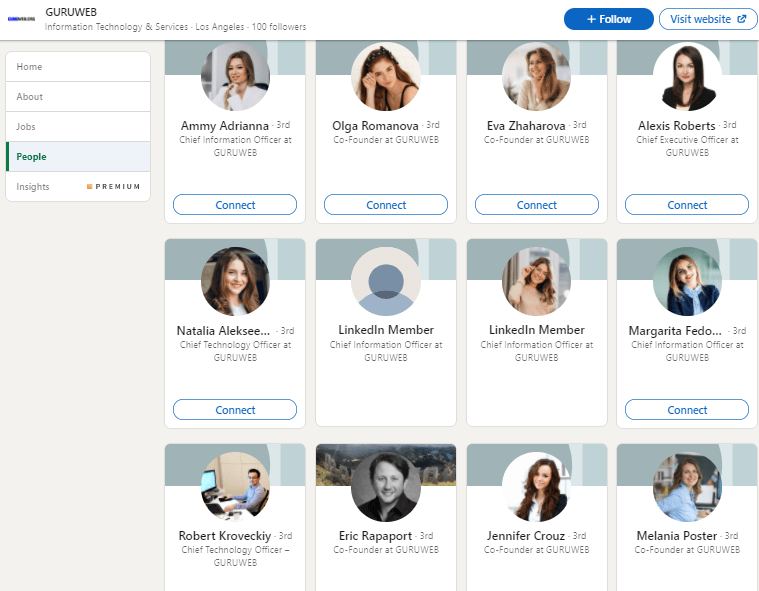
According to LinkedIn, the company has dozens of employees, including a vast number of co-founders, chief technology officers, and chief information officers. While some are based in Los Angeles, others are based in Chicago, Dallas, Maidenhead, Kyrgyzstan, and other exotic locations. Most remarkably, based upon some of the employee pictures, the company goes over and above in its attempts to attract female technologists. It’s a statistical anomaly!
Under normal circumstances, this remarkable string of oddities would have gone completely unnoticed. I have never interacted with any of these employees, and they don’t seem to be all that active on the LinkedIn platform. Well, with some exceptions; the Chicago-based CEO of the company has made a valuable contribution to the LinkedIn discussion.

Now most of this went under the radar, until a number of LinkedIn employees made connection requests to a particular individual. Unfortunately, this particular individual was Kris’ Rides, a cybersecurity specialist with Tiro Security.
(Before you ask whether Rides himself is a bot, I should note that he has received 40 recommendations on LinkedIn from people that appear to be real, and has amassed over 500 connections. So if Rides is a bot, he is a very effective one.)
When Rides received these connection requests (including two CTOs and two CIOs at the same company), they struck him as odd. So he shared his experience with his connections, which included other cybersecurity professionals, and people (such as me) who were connected to those other cybersecurity professionals. And they’re talking.
Pro tip: if you’re engaging in synthetic identity fraud, don’t reach out to a cybersecurity professional.
Now this story probably won’t be a trending topic on Twitter, even if the bots try to make it so, but it’s certainly gaining traction in the audience that counts: namely, technology experts who have the power to tell LinkedIn and others about questionable marketing techniques.

So what happens next? A mea culpa from Eric (or whatever his or her real name is)? Time will tell.

3 Comments