Whether a student is attending a preschool, a graduate school, or something in between, the educational institution needs to know who is accessing their services. This post discusses the types of identity verification and authentication that educational institutions may employ.
Why do educational institutions need to verify and authenticate identities?
Whether little Johnny is taking his blanket to preschool, or Johnny’s mother is taking her research notes to the local university, educational institutions such as schools, colleges, and universities need to know who the attendees are. It doesn’t matter whether the institution has a physical campus, like Chaffey High School’s campus in the video above, or if the institution has a virtual campus in which people attend via their computers, tablets, or phones.
Access boils down to two questions:
- Who is allowed within the educational institution?
- Who is blocked from the educational institution?
Who is allowed within the educational institution?
Regardless of the type of institution, there are certain people who are allowed within the physical and/or virtual campus.
- Students.
- Instructors, including teachers, teaching assistants/aides, and professors.
- Administrators.
- Staff.
- Parents of minor students (but see below).
- Others.
All of these people are entitled to access to at least portions of the campus, with different people having access to different portions of the campus. (Students usually can’t enter the teacher’s lounge, and hardly anybody has full access to the computer system where grades are kept.)
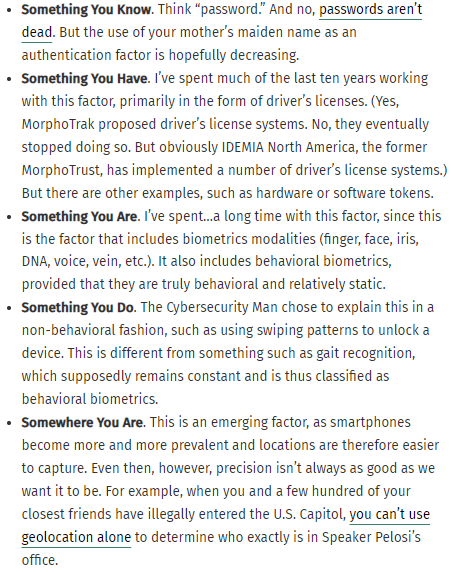
Before anyone is granted campus privileges, they have to complete identity verification. This may be really rigorous, but in some cases it can’t be THAT rigorous (how many preschoolers have a government ID?). Often, it’s not rigorous at all (“Can you show me a water bill? Is this your kid? OK then.”).
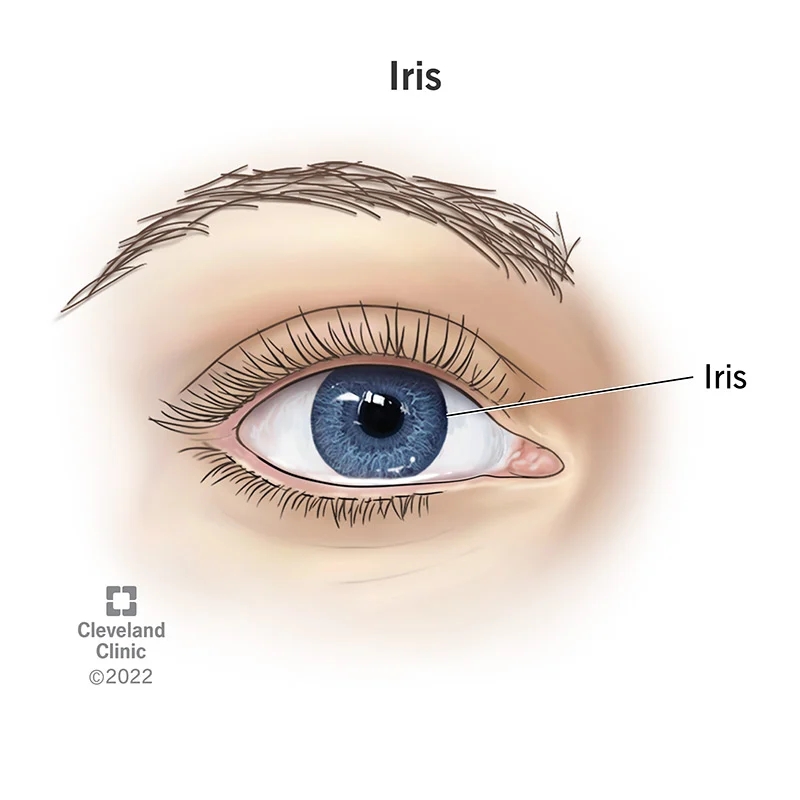
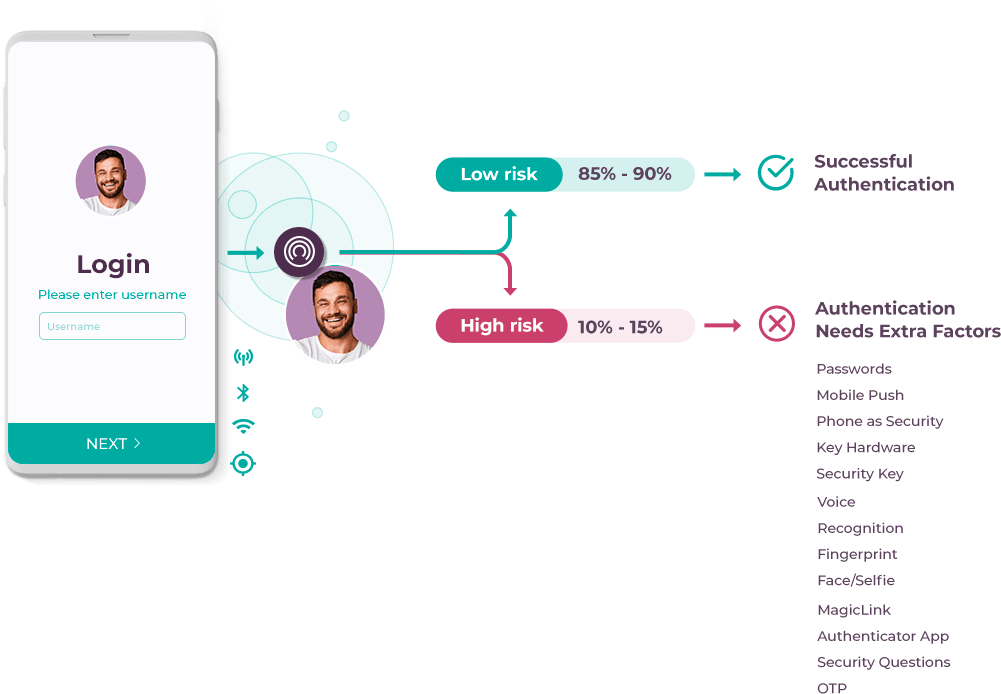
Once an authorized individual’s identity is verified, they need to be authenticated when they try to enter the campus. This is a relatively new phenomenon, in response to security threats at schools. Again, this could be really rigorous. For example, when students at a University of Rhode Island dining hall want to purchase food from the cafeteria, many of then consent to have their fingerprints scanned.
Another rigorous example: people whose biometrics are captured when taking exams, to deter cheating.
But some authentiation is much less rigorous. In these cases, people merely show an ID (hopefully not a fake ID) to authenticate themselves, or a security guard says “I know Johnny.”
(Again, all this is new. Many years ago, I accompanied a former college classmate to a class at his new college, the College of Marin. If I had kept my mouth shut, the professor wouldn’t have known that an unauthenticated student was in his class.)
Who is blocked from the educational institution?
At the same time, there are people who are clearly NOT allowed within the physical and/or virtual campus. Some of these people can enter campus with special permission, while some are completely blocked.
- Former students. Once a student graduates, their privileges are usually revoked, and they need special permission if they want to re-enter campus to visit teachers or friends. (Admittedly this isn’t rigorously enforced.)
- Expelled students. Well, some former students have a harder time returning to campus. If you brought a gun on campus, it’s going to be much harder for you to re-enter.
- Former instructors, administrators, and staff. Again, people who leave the employ of the institution may not be allowed back, and certain ones definitely won’t be allowed back.
- Non-custodial parents of minor students. In some cases, a court order prohibits a natural parent from contact with their child. So the educational institutions are responsible for enforcing this court order and ensuring that the minor student leaves campus only with someone who is authorized to take the child.
- Others.
So how do you keep these people off campus? There are two ways.
- If they’re not on the allowlist, they can’t enter campus anyway. As part of the identity verification process for authorized individuals, there is a list of people who can enter the campus. By definition, the 8 billion-plus people who are not on that “allowlist” can’t get on campus without special permission.
- Sometimes they can be put on a blocklist. Or maybe you want to KNOW that certain people can’t enter campus. The inverse of an allowlist, people who are granted access, is a blocklist, people who are prevented from getting access. (You may know “blocklist” by the older term “blacklist,” and “allowlist” by the older term “whitelist.” The Security Industry Association and the National Institute of Standards and Technology recommend updated terminology.)
There’s just one teeny tiny problem with blocklists. Sometimes they’re prohibited by law.
In some cases (but not in others), a person is required to give consent before they are enrolled in a biometric system. If you’re the ex-student who was expelled for brining a gun on campus, how motivated will you be to allow that educational institution to capture your biometrics to keep you off campus?
And yes, I realize that the expelled student’s biometrics were captured while they were a student, but once they were no longer a student, the institution would have on need to retain those biometrics. Unless they felt like it.
This situation becomes especially sticky for campuses that use video surveillance systems. Like Chaffey High School.

Now the mere installation of a video surveillance system does not (usually) result in legally prohibited behavior. It just depends upon what is done with the video.
- If the video is not integrated with a biometric facial recognition system, there may not be an issue.
- If Chaffey High School has its own biometric facial recognition system, then a whole host of legal factors may come into play.
- If Chaffey High School does not have a biometric facial recognition system, but it gives the video to a police agency or private entity that does have a biometric facial recognition system, then some legal factors may emerge.
Or may not. Some facial recognition bans allow police use, and if this is true then Chaffey can give the footage to the police to use for authorized purposes. But if the jurisdiction bans police use of facial recognition, then people on the video can only be recognized manually. And you know how I feel about that.
Writing About Educational Identity
As you can see, educational identity is not as clear-cut as financial identity, both because financial institutions are more highly regulated and because blocklists are more controversial in educational identity. Vladimir Putin may not be able to open a financial account at a U.S. bank, but I bet he’d be allowed to enroll in an online course at a U.S. community college.
So if you are an educational institution or an identity firm who serves educational institutions, people who write for you need to know all of these nuances.
You need to provide the right information to your customers, and write it in a way that will motivate your customers to take the action you want them to take.
Speaking of motivating customers, are you with an identity firm or educational institution and need someone to write your marketing text?
- Someone with 29 years of identity/biometric marketing experience?
- Someone who understands that technological, organizational, and legal issues surrounding the use of identity solutions?
- Someone who will explain why your customers should care about these issues, and the benefits a compliant solution provides to them?
If I can help you create your educational identity content, we need to talk.
- Email me at john.bredehoft@bredemarket.com.
- Book a meeting with me at calendly.com/bredemarket.
- Contact me at bredemarket.com/contact/.
- Subscribe to my mailing list at http://eepurl.com/hdHIaT.