If you’re not familiar with the complete history of the Eagles, you may not know that they began as practitioners of country rock. Their early songs were therefore softer than the ones from the Joe Walsh years.
One of those songs (actually later, but earlier in feel) was “Lyin’ Eyes.”
And it contains a lyrical oddity.
Glenn Frey and Don Henley could tell stories with the best country songwriters. And this was no exception, with a tale of a woman seeking solace outside of her marriage. Her life gets more scattered, until the singer turns judge and announces, “My, oh my, you sure know how to arrange things.”
But before that, when the singer is merely telling the story, the woman needs to seek solace.
So the singer says what the woman is doing:
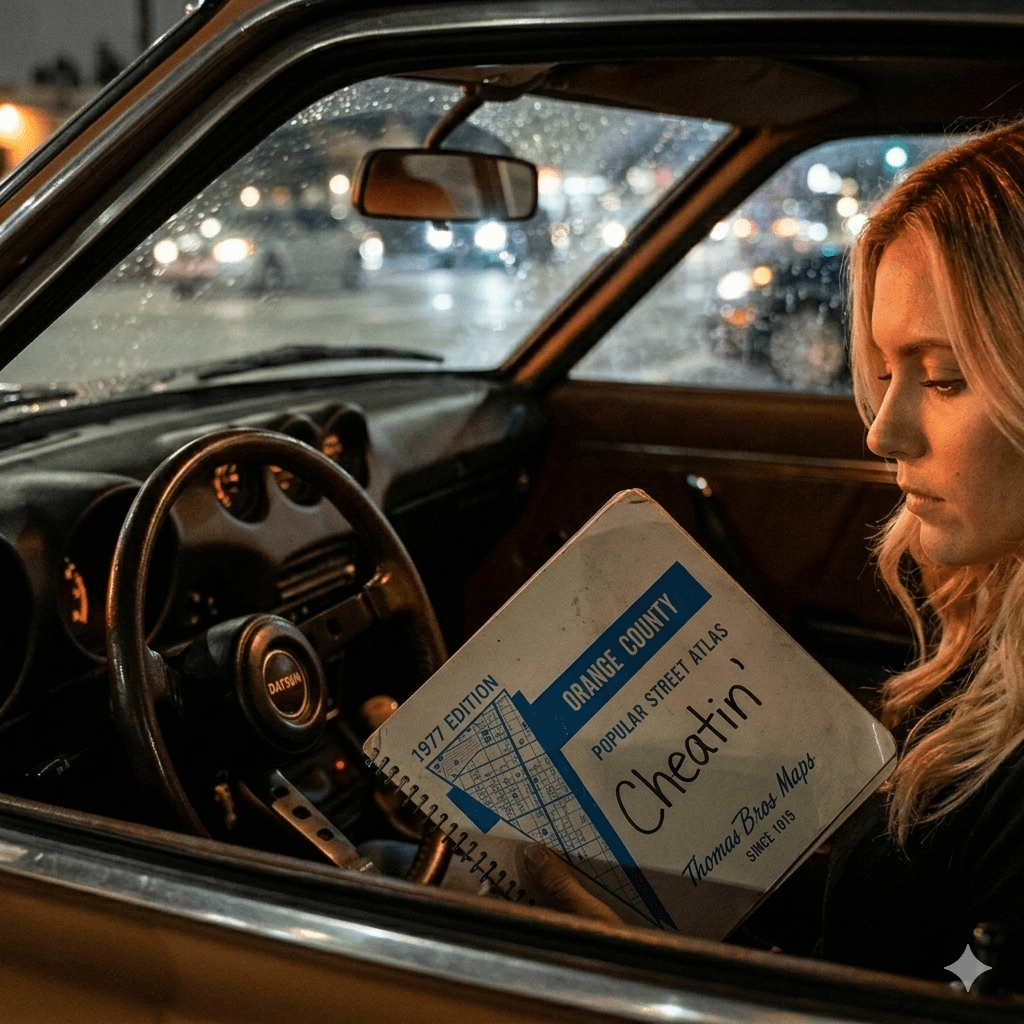
“She is headed toward the cheatin’ side of town”
Now this is a lyrical fiction.
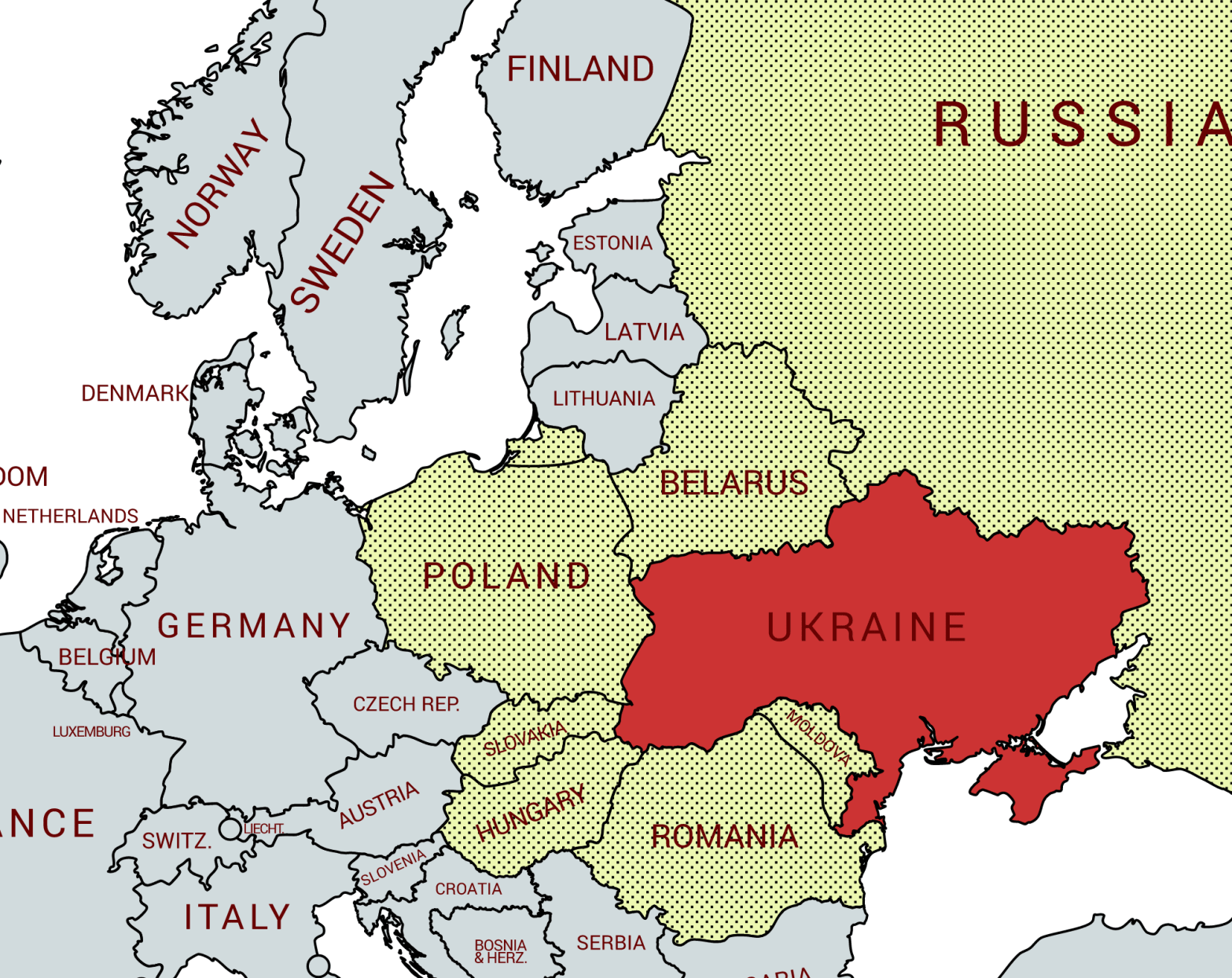
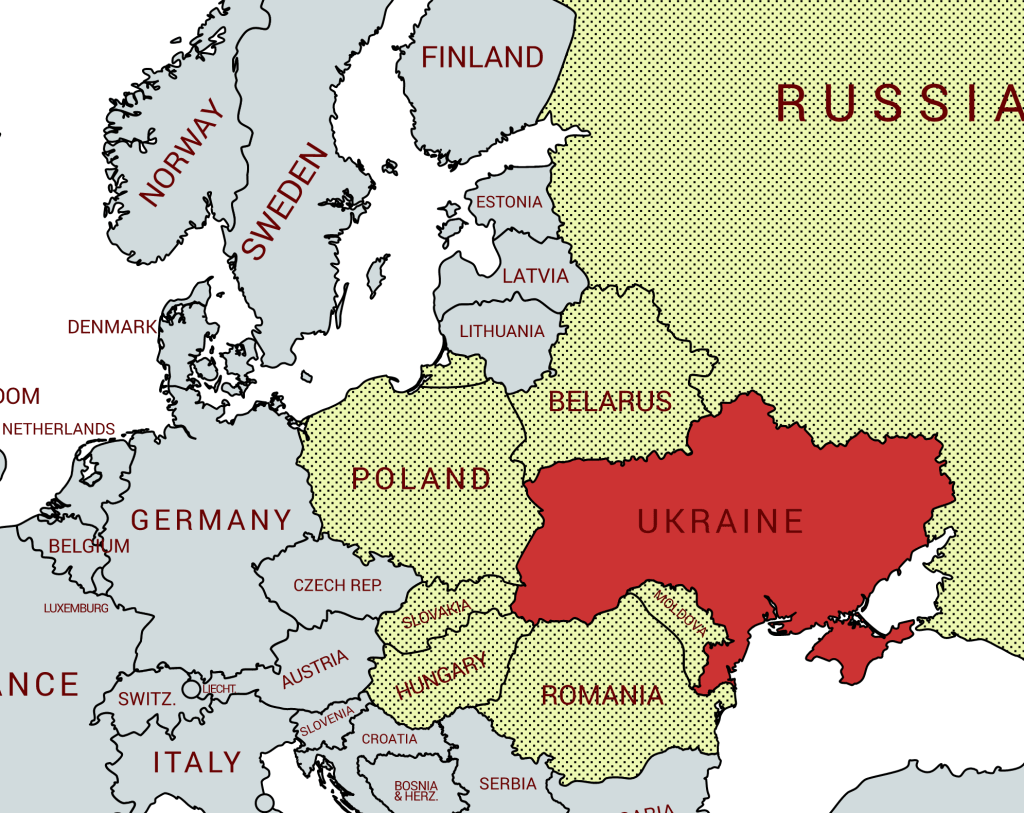
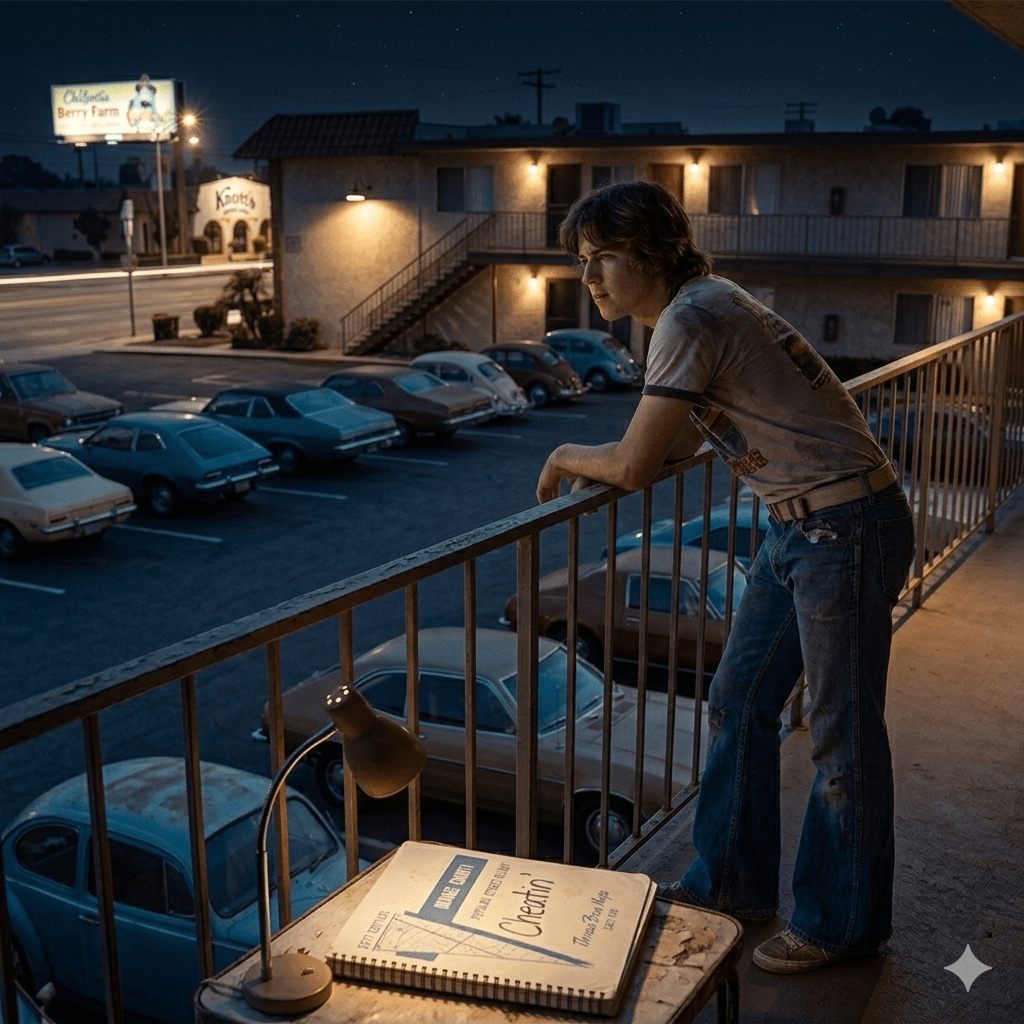
To my knowledge, no town in California or anywhere else enforces residential zoning regulations that segregate cheaters from non-cheaters. When “the boy” in the song rented his apartment (in Buena Park?), he didn’t need to indicate his receptiveness to desperate housewives. (Different decade, I know.)
So if the cheatin’ side of town is not a geolocation, is it perhaps tied to another factor of authentication?
Such as the sixth factor—somewhat you why?
After all, you could use non-identity biometrics such as respiration to discover the intent of a woman, whether she is driving
- to comfort an old friend who’s feeling down, or
- to rush into a man’s arms as they fall together.
Cheaterland is a state of mind. My, oh my.
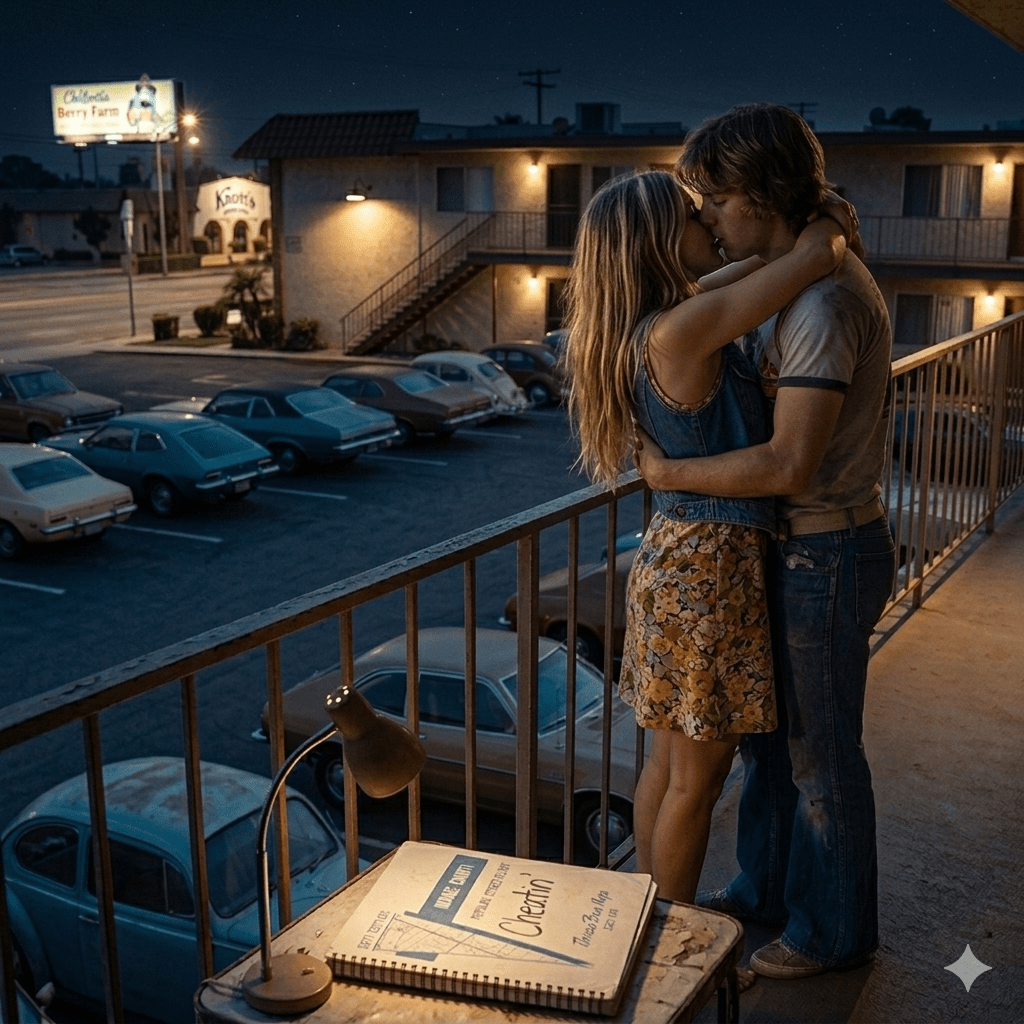
And if I may interject an author’s note, I am VERY impressed with Google Gemini (Nano Banana 2) for knowing what a “Thomas Brothers Map” is. Except that I had to change my story setting from North Hollywood to Buena Park to match the images.
“Life in the Fast Lane,” of course, would need a Los Angeles County map.