Perhaps it’s different in Louisiana where the mDL is long established and supported, but in California the only place where I’ve used my mDL is at a TSA checkpoint. And last Friday I couldn’t even do that because the reader was down.
But at least mDLs are available to a large number of people. deepidv provides this good news…and the bad news.
“As of mid-January 2026, the American Association of Motor Vehicle Administrators tracks 21 US states plus Puerto Rico issuing ISO/IEC 18013-5 compliant mobile driver’s licenses. That includes California, New York, Virginia, Arizona, and most of the largest population states. Industry analysis puts the figure at roughly 41 percent of Americans now living in a state with an active mDL program, and 76 percent in a state where the program is live or in development.”
So at least many of us can get mDLs. But as I noted, it’s a challenge to use them in-person, despite a standard outlining how it can be used.
“ISO/IEC 18013-5 covers proximity presentation. The mDL holder shows the credential to a verifier device that is physically nearby, typically over Bluetooth Low Energy or NFC. That works for airport security, in-person retail age checks, and traffic stops.”

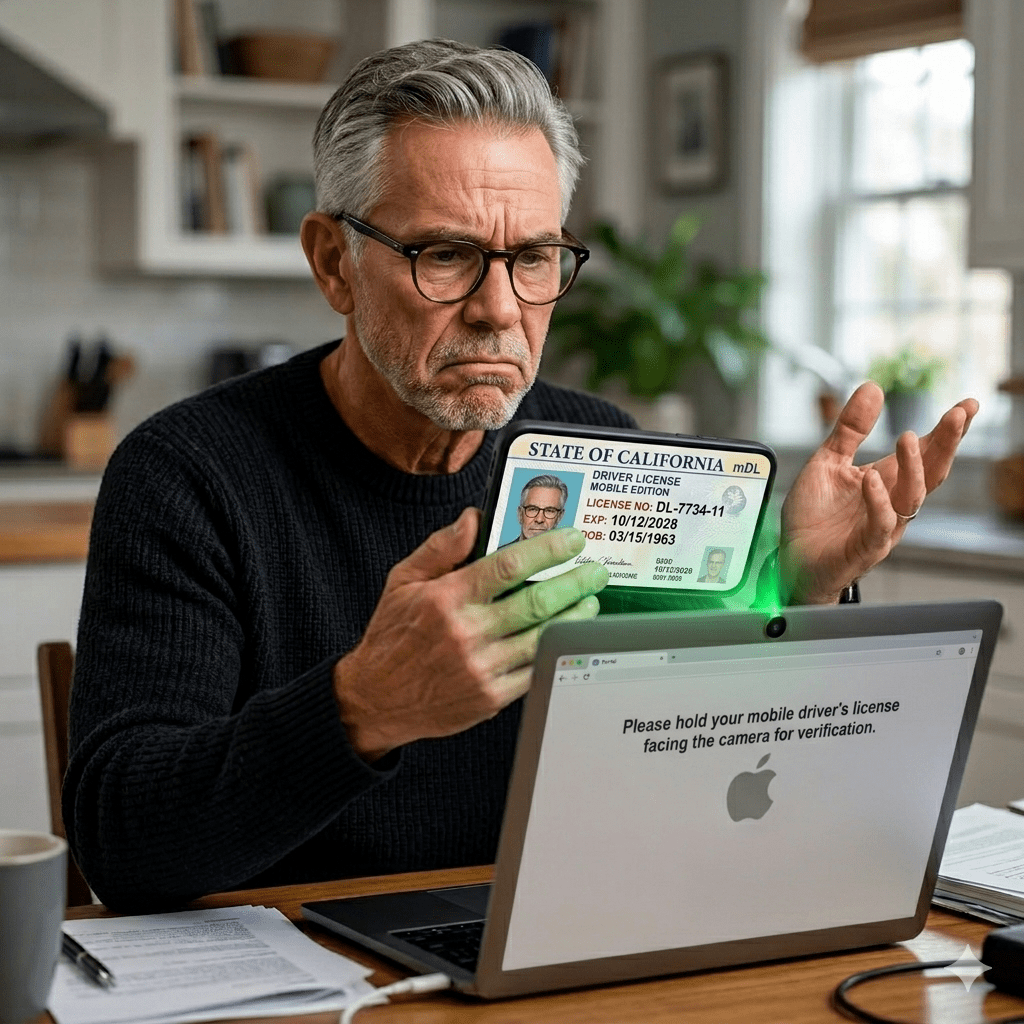
But it’s a greater challenge to use mDLs online.
“It does not work for online onboarding because there is no proximity. For online flows, the standard is ISO/IEC TS 18013-7, published in 2025, which defines remote and online presentation. Adoption of Part 7 is, in the words of the people building these systems, “limited and inconsistent.””
This is where the benefit of decentralized identity falls apart. In a decentralized identity system, the user controls where the identity is stored. (I have two California mDLs on my phone, because decentralized is very decentralized.)
deepidv has concerns with this:
“Device-side verification means the cryptographic check that establishes whether the credential is authentic happens in an environment the relying party does not control. A rooted phone, a compromised app, a tampered SDK, a man-in-the-middle on the verification flow, all of these break the trust model. The relying party is being asked to trust a yes-no answer it cannot independently verify.”
deepidv describes server-side verification, as well as other issues with mDL adoption, in its LinkedIn article.
Though not referenced by name, deepidv cites Regula’s support of server-side processing:
“Malware, rooted phones, tampered apps: User devices such as smartphones can pose risks to identity verification, as these environments are difficult to control against fraud.
“Regula says it has a solution. The identity verification firm has introduced server-side reprocessing of mobile driver’s license (mDL) data in its document reader software, Regula Document Reader SDK. The capability means that mDL data is processed on the backend in a controlled, trusted environment rather than relying solely on user devices, which also helps preserve the integrity of the identity signal across the verification flow. Data captured on the user’s device is revalidated through a PKI check and signature verification on the server.”
But will the decentralized identity people insist that server-side verification is evil? And how will the decentralized proponents convince others that a decentralized identity is really really secure?
If your company has a decentralized or centralized solution and you need to communicate its benefits to prospects, Bredemarket can work with you.