Sometimes our mental horizons are limited, and we fail to notice things just outside of our sphere of vision. And when we ignore these things, we may receive nasty surprises.
The first step in competitive analysis is to identify your competitors. Some companies utterly fail at this by declaring, “We have no competitors.” (Voiceover: “You do.”) But even those companies that successfully identify their competitors do not always identify ALL of them.

For example, if you owned a taxicab company circa 2008, you might count other taxicab companies and buses as competitors, but you might not include the possibility of a competitor raising over $25 billion to create an infrastructure that allowed people to use their own cars to pick up people who needed rides. Of course, Uber and other companies did just that, while at the same time dodging taxicab industry regulations that mandated purchase of medallions. The rideshare companies weren’t always successful at dodging these regulations, but sometimes they were. As a result, by 2015 the taxicab industry was dying.
This is just one of many examples of competitors that seemingly arise out of nowhere and decimate existing businesses.
One biometric modality for authentication
When considering authentication of individuals, we sometimes fail to, um, identify ALL the ways in which individuals can be identified.
When I entered the biometric industry in the mid-1990s, people were individually identified by something they had (such as a credit card), something they knew (such as a personal identification number or PIN associated with the credit card), and with a rudimentary form of something they were (a signature that matched the signature on the back of the credit card).
My employer and two other companies thought that we had a better solution than the rudimentary signature verification check—fingerprints. All three companies proposed solutions in which welfare benefit recipients would use fingerprints to authenticate themselves as the persons entitled to the welfare benefits. (Another ramification: the fingerprints could also be used to confirm that people weren’t receiving benefits under multiple names.) But in those pre-iPhone days signatures were associated with law enforcement, and benefit recipients feared that the benefit agencies would forward their fingerprints to the cops, and the use of fingerprints by welfare benefits agencies decreased.
But many people still felt that fingerprints could be used to identify individuals, and therefore people began to look at the fingerprint industry and identify competitors in that industry. Around 2000, those competitors included Cogent, Morpho, NEC, Printrak, livescan companies such as Digital Biometrics and Identix, and a few others.
But fingerprints aren’t the only biometric modality, and there were other competitors outside of the fingerprint companies.
Multiple biometric modalities for authentication
By the early 2000s, other biometric modalities matured enough to be used for authentication purposes. Faces were tested for identification of people at Super Bowl XXXV. Irises began to be used for authentication at airports in Amsterdam (and elsewhere) in 2001, although they were cumbersome to capture. Individuals could eventually be identified via their voices.
All of these different biometric modalities got people excited. Some people, um, “advanced” the notion that biometrics (something you are) was THE way to identify people, and that passwords were of necessity going to die. Bill Gates predicted the death of the password in 2004, but he wasn’t (and isn’t) the only one to assert this view. Some assert that biometrics are clearly better than passwords. Opponents, however, objected to a reliance on only biometrics because of the ability to spoof biometrics, and because of perceived and actual racial disparities. (See my comments on faulty conclusions, and on the racist methods that people use when they DON’T use computerized facial recognition.)
Multiple factors of authentication
The solution, as many people recognized, was to use multiple factors of authentication, not just “something you are” (biometrics).
Why multiple factors? Because if you use multiple methods to identify an individual, the ability to fraudulently impersonate an individual decreases rapidly.
Even if someone spoofed your fingerprint or face, it would be much harder for them to spoof your fingerprint/face and your driver’s license, or your fingerprint/face and your driver’s license and your password.
The National Institute of Standards and Technology (NIST) has helpfully defined the term multi-factor authentication, or MFA, for standardized U.S. government use.
Authentication using two or more factors to achieve authentication. Factors include: (i) something you know (e.g. password/personal identification number (PIN)); (ii) something you have (e.g., cryptographic identification device, token); or (iii) something you are (e.g., biometric). See authenticator.
From https://csrc.nist.gov/glossary/term/Multi_Factor_Authentication
Source(s):
CNSSI 4009-2015 under multifactor authentication from NIST SP 800-53 Rev. 4
But are three factors of authentication enough?
Sometimes the government moves more slowly than the industry. This is one of those times.
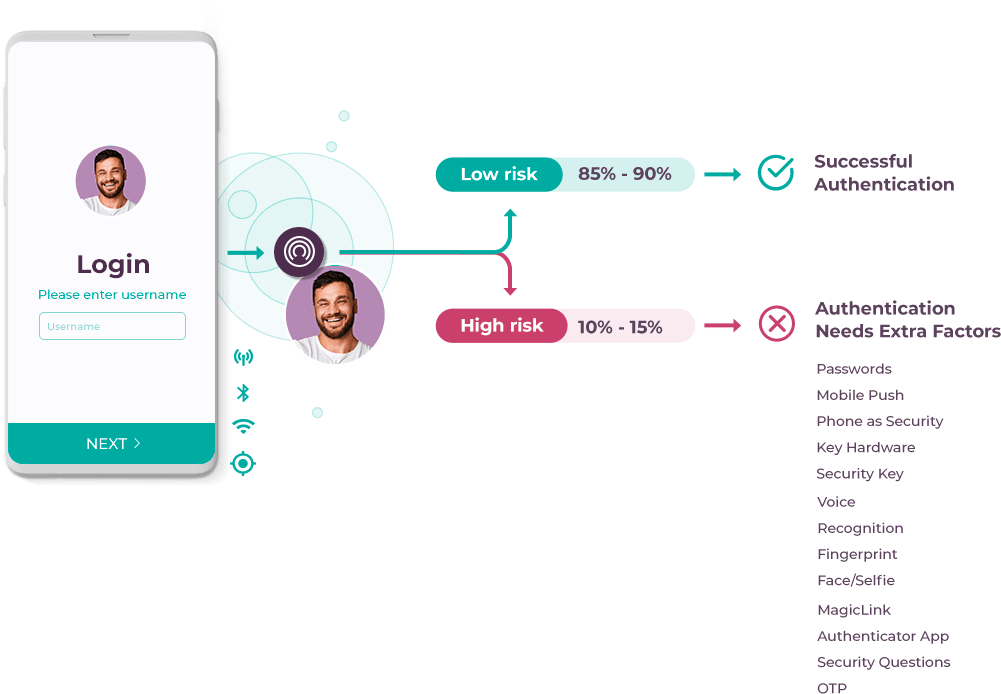
While NIST only discusses the three factors of something you know, have, and are as factors of authentication, other sources identify two additional factors. I personally use a model which includes five authentication factors, in which the other two factors are “something you do” and “somewhere you are.”
Let me illustrate how the fifth authentication factor could have helped me out several years ago.
In mid-2009, roughly fifteen years after joining the biometric industry, I had just become an employee of the new company MorphoTrak, but had not yet shifted from product management to proposals. MorphoTrak still operated as two separate divisions, and an opportunity arose for me to demonstrate a product from the Printrak division to customers of the Morpho division.

So I, along with a Metro ID demonstration system, flew to Atlantic City, New Jersey to attend a trade show which would have many attendees from New Jersey, a Morpho customer. Theoretically, local New Jersey agencies could buy Metro ID and submit results from that system to the New Jersey MetaMorpho system.

I had just acquired a new credit card for business purposes, which I would use for the first time at the trade show.
When I first tried to use the card, it was declined.
Look at it from the credit card issuer’s perspective:
- Someone had just received a credit card, which had never been used.
- The first time that someone tried to use the credit card, it was used thousands of miles from the California location where the customer lived and worked.
- Sure the transaction was for a low dollar amount (I think I was at a McDonald’s), but there’s always the danger that if that transaction were approved, the user would next walk a few blocks to a casino and withdraw thousands of dollars.
- Because this seems suspicious, we’d better check it out before approving any transactions. Maybe the card was stolen.
So the credit card company had to verify that the use in Atlantic City was legitimate. To do so, they called my house in California.
Which ordinarily would be fine, but I was not at my house in California. I was in Atlantic City.
Eventually, everything worked out, but wouldn’t it be nice if the credit card company realized that not only did
- the person using John Bredehoft’s credit card actually have possession of the card, and that
- the person using John Bredehoft’s credit card knew the PIN associated with the card, but also that
- John Bredehoft was physically in Atlantic City, New Jersey, where the card was being used?
Now you can see how “somewhere you are,” or geolocation, could be used as an identifier. Of course this would be very hard to authenticate in 1994, and wasn’t even a common authenticator in 2009, but clearly in 2022 everyone can figure out where you are.
Incognia and (not) zero factor authentication
Enter Incognia, a company that states that is offers an identification solution that uses what they call “zero factor authentication.” Tyler Choi of Biometric Update explains why Incognia’s solution is important:
Incognia points to an increase in revenue and activity across apps in financial services, crypto, social networks, and online gaming, which accentuates the need for fraud prevention.
From https://www.biometricupdate.com/202203/incognia-adds-location-fraud-detection-to-mobile-onboarding-and-authentication
While I have a problem with the “zero authentication factor” / “0FA” semantics Incognia uses (location IS an authentication factor, at least in my model), I can appreciate what the company does.
Incognia’s award-winning location identity technology is highly resistant to location spoofing and offers superior location precision for accurate fraud detection on mobile with very low false-positive rates. Incognia uses network, location, and device intelligence data to silently recognize trusted users based on their unique behavior patterns….
Incognia’s location technology uses data from not only GPS, but also WiFi, cellular and Bluetooth sensors, which makes it highly effective at detecting location spoofing, unlike fraud detection based on IP and GPS alone.
From https://www.incognia.com/location-behavioral-analytics?hsLang=en
Incognia asserts that the vast majority of transactions can be authenticated based on location alone. For example, if I perform a transaction when at my house, the chance is high that I am truly the person performing the transaction.
But what if I perform a transaction on the other side of the country, in a location that I have never visited before? Then Incognia uses additional factors of authentication to verify my identity.
For example, I could provide the password or a biometric identifier. The very fact that I possess a phone that was previously associated with me is another indicator that I may be who I say I am.
But we’re not really using geolocation yet
However, geolocation is not commonly used as an authentication factor, something that I subsequently discovered several years after my trip to Atlantic City.
By this time I had acquired another credit card for business purposes, and my credit card provider noticed some strange behavior. Not a single attempt to purchase food across the country at a restaurant in New Jersey, but multiple repeated purchases across the country at a store in Virginia.
The credit card provider got suspicious when the person made repeated small balance purchases at the same store, and froze the account until it could check with me to see if those purchases were legitimate. This time I was home in California and was able to confirm that the purchases were fraudulent.
Of course, the credit card provider could have detected this much more quickly if it knew that I was not in Virginia, but California.
So when you perform competitive analysis on authentication companies, don’t forget about competitors that use geolocation.




2 Comments