My belief that everything on the Internet is true has been irrevocably shattered, all because of what an entertainment executive ordered in his spare time. But the Casey Bloys / “Kelly Shepherd” story is just a tiny bit of what is going on with synthetic identities. And X isn’t the only platform plagued by them, as my LinkedIn experience attests.
By the way, this blog post contains pictures of a lot of people. Casey Bloys is real. Some of the others, not so much.
Blame COVID
Casey Bloys is the Chairman and CEO of HBO and Max Content. Bloys had to start a recent 2024 schedule presentation with an apology, according to Variety. After explaining how passionate he is about his programming, he went back in time a couple of years to a period that we all remember.
So when you think of that mindset, and then think of 2020 and 2021, I’m home, working from home and spending an unhealthy amount of scrolling through Twitter. And I come up with a very, very dumb idea to vent my frustration.
From Variety.
Casey Bloys’ very, very dumb idea
So why did Bloys have to apologize on Thursday? Because of an article that Rolling Stone published on Wednesday. The article led off with this juicy showbiz tidbit about Bloys’ idea for responding to a critic.
“Maybe a Twitter user should tweet that that’s a pretty blithe response to what soldiers legitimately go through on [the] battlefield,” he texted. “Do you have a secret handle? Couldn’t we say especially given that it’s D-Day to dismiss a soldier’s experience like that seems pretty disrespectful … this must be answered!”
From Rolling Stone.
(A note to my younger readers: Twitter used to be a popular social media service that no longer exists. It was replaced by X.)
Eventually Bloys found someone to create the “secret handle.” Sully Temori is now alleging wrongful termination by HBO (which is why we’re learning about these juicy tidbits, via court filings). But in 2021 he was an executive assistant who wanted to get ahead by pleasing his bosses.
This is where Kelly Shepherd enters the story.
Kelly Shepherd, fake vegan mom
Ms. Shepherd seems like a nice woman. A mom, a Texan, a herbalist and aromatherapist, and a vegan. (The cows love that last part.)
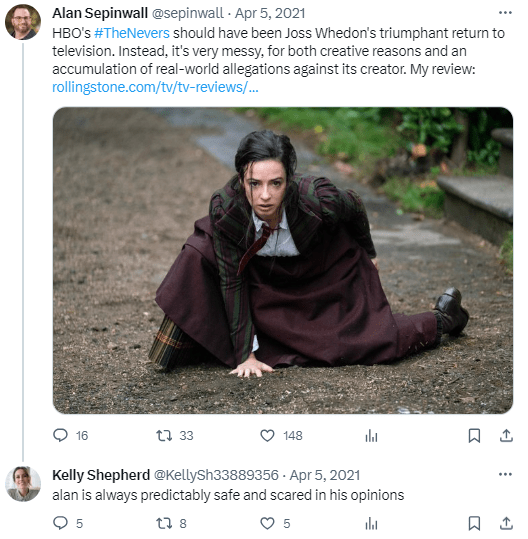
Most critically, Shepherd is a normal person, not one of those Hollywood showbiz folks. Although Shepherd, who never posted anything on her own, seems to have a distinct motivation to respond to critics of HBO shows. Take her first reply to a critic from (checks notes) Rolling Stone. (Two years later, Rolling Stone would gleefully report on this story. Watch out who you anger.)
alan is always predictably safe and scared in his opinions
From https://twitter.com/KellySh33889356/status/1379101699969720323
Kelly’s other three replies were along the same lines.
- All were short one-sentence blurbs.
- Most were completely in lower case, because that’s how regular non-Hollywood folk tweet.
- All were critical of those who were critical of HBO, accusing them of “shitting on a show about women,” getting their “panties in a bunch,” and being “busy virtue signaling.”
Hey, if I couldn’t eat hamburgers and my home was filled with weird herbs and aromas, I’d be a little mad too.
And then, a little over a week later, it was over, and Kelly Shepherd never tweeted again. Although Temori apparently performed other activities against HBO critics via other methods. Well, until he was terminated.
Did Kelly Shepherd open a LinkedIn account?
But as part of the plan to satisfy Casey Bloys’ angry whims, Kelly Shepherd acquired a social media account, which she could use as a possible proof of identity.
Even though we now know she doesn’t exist.
But X isn’t the only platform plagued with synthetic identities, and some synthetic identities can do much more than anger an entertainment reviewer.
Many of us on LinkedIn are regularly receiving InMails and connection requests (in my case, from profiles with pictures of beautiful women) who say that we are constantly recommended by LinkedIn, who tell us how impressive our profiles are, and who want to contact us outside of the LinkedIn platform via text message or WhatsApp.
Now perhaps some of these messages are from real people, but I seriously doubt that so many of the employees at John Q Wine & Liquor Winery in New York happen to have the last name “Walter.” And the exact same job title.
Let’s take a close look at what Karina has been doing for the last 4+ years. Other than posing in front of her car, of course.
Ms. Walter is a pretty busy freelance general manager / director / content partnerships manager.
As for her colleague Ms. Alice Walter, she has more experience (having started in 2018) but also has an extensive biography that begins:
The United States is a country with innovative challenges, and there is more room for development in the wine industry at John Q Wine & Liquor Winery. I am motivated and love to learn, and like to be exposed to more different cultures, and hope to develop more careers in my future life.
From https://www.linkedin.com/in/alice-walter-b97bb2113/
Sound familiar?
And you can check out Maria Walter’s profile if you’re so inclined. Or at least check out “her” picture.
Now none of the Walters women tried to contact me, but another “employee” (or maybe it was a “freelancer,” I forget) of this company tried to do so, which led my curious nature to discover yet another hive of fake LinkedIn profiles.
Sadly, one person from this company is a second-degree connection, which means that one of my connections accepted “her” connection request.
Synthetic identities are harmless…right?
Who knows what Karina, Alice, and Maria will do with their LinkedIn profiles?
- Will they connect with other professionals?
- Will they ask said professionals to move the conversation to SMS or WhatsApp, for whatever reason?
- Will they apply for new jobs, using their impressive work history? A 98.8% customer satisfaction rate while managing 1,800 sub-partnerships is remarkable.
- Will they apply for bank accounts…or loans?
The fraud possibilities from fake LinkedIn accounts are endless, and could be very costly for any company who falls for a fake synthetic identity. In fact, FiVerity reports that “in 2020, an estimated $20 billion was lost to SIF” (synthetic identity fraud). Which means that LinkedIn account holders and Partnerships Managers Karina, Alice, and Maria Walter could make a LOT of money.
Now banks and other financial institutions have safeguards to verify financial identities of people who open accounts and apply for loans, because fraud reduction is critically important to financial institutions.
Social media companies? Identity is only “important” to them.
They don’t even care about uniqueness (as Worldcoin does), evidenced by the fact that I have more than two X accounts (but none in which I portray a female Texas mom and vegan).
So if someone comes up to you on X or LinkedIn, remember that all may not be as it seems.