Inland Empire firms: does anyone know who you are?
Who can help your firm create content?
- Blog posts?
- Case studies?
- White papers?
- Social media?
- Market and competitive analyses?
Contact Bredemarket: https://bredemarket.com/contact/
Identity/biometrics/technology marketing and writing services

Inland Empire firms: does anyone know who you are?
Who can help your firm create content?
Contact Bredemarket: https://bredemarket.com/contact/
(Part of the biometric product marketing expert series)
Is your firm asking the following questions?
Bredemarket can help you answer these questions.
For those who don’t know, or who missed my previous discussion on the topic, Bredemarket performs analyses that contain one or more of the following:
Bredemarket analyses only use publicly available data.
These analyses can range in size from very small to very large. On the very small side, I briefly analyzed the markets of three prospect firms in advance of calls with them. On the large side, I’ve performed analyses that take between one and six weeks to complete.
Obviously I can’t provide specifics upon the analyses I’ve already performed since those are confidential to my customers, but I always discuss the customers’ needs before launching the analysis to ensure that the final product is what you want. I also provide drafts along the way in case we need to perform a course correction.
Do you need a market, competitor, or self analysis? Contact me. Or book a meeting with me at calendly.com/bredemarket to talk about your needs (and check the “Market/competitor analysis” check box).

Identity/biometric firms: does anyone know who you are?
Who can help your firm create content?
Who knows identity/biometrics:
Who can provide content:
I know who can help.
Contact Bredemarket: https://bredemarket.com/contact/

Identity professionals, what’s in a name?
You cannot uniquely identity someone by name alone.
A unique identification relies on multiple factors.
If your firm desires to tell a story about how your identity solution surpasses name-based solutions, Bredemarket can help.

Technology marketers, do you need written content?
If you don’t use written content to communicate with your prospects and clients, save yourself some time and stop reading this.
But if you realize that written content is essential for prospect awareness, consideration, and especially conversion…
And if you need someone adept at creating a variety of written content, from blog posts and articles to case studies and white papers to smartphone application content and scientific book chapters…
Bredemarket can help.
I have created all of these types of content, plus internal content such as market/competitor analyses and proposal templates. And I can create this content for your company.
To address your content gaps today, talk to Bredemarket via my contact page, or book a meeting.

By the way, if you’d like nore information on the 22 types of content, read “The 22 (or more) Types of Content That Product Marketers Create.”
Bredemarket offers marketing and writing services to firms who need help, or who don’t have the time to craft their own content.
Talk to Bredemarket…today! Visit https://bredemarket.com/contact/ or https://calendly.com/bredemarket.

Here is one way to test the marketing of your AI product.
If your product marketing fails the “Pentium” test, Bredemarket can help.
Contact Bredemarket.

(Delivery van image by Unisouth at English Wikipedia, CC BY-SA 3.0, https://commons.wikimedia.org/w/index.php?curid=3897499)
All of my Bredemarket work involves providing deliverables to clients in some way:

For all but one Bredemarket client, I provide my deliverables via email. The deliverables usually consist of items such as Microsoft Word documents, Microsoft Excel workbooks, and Portable Document Files.
Easy to email.
Except in one case.
As I mentioned above, Bredemarket often performs market/competitive analyses. In fact, one of my clients likes my analyses so much that they keep on coming back for more analyses to cover different markets.
For the last three analyses for this particular client, my deliverables have consisted of the following:

In my analyses I referred to the companies’ publicly available websites to gather information on the competitor products, as well as the markets they address. (Using a made-up example, if my client provided its products to convenience stores, and a particular competitor ALSO targeted convenience stores, my client would obviously want to know this.)
But for this third analysis I didn’t just look at the websites. I also looked at the product brochures that I could download from these websites.

This gave me an idea.
Since I was downloading all the publicly available brochures from the various competitors, why not provide all of these brochures to my client?
It seemed like a great idea. Since I had gone through all the work to collect the brochures, might as well let my client make future use of them.
So as I wrapped up the project and prepared the deliverables for my client, I discovered that I had amassed over 100 megabytes of brochures. (That’s what happens when you analyze over 100 competitor products.)

So my idea of zipping all the brochures into a single file wouldn’t work. Even the zip file exceeded the attachment sending limits of Bredemarket’s email service provider, Google. (And probably exceeded the attachment receiving limits of my client’s email service provider.)
And if you’ve already figured out the obvious solution to my problem, bear with me. It took me several days to realize the obvious solution myself.
Anyway, I hit upon a great solution to my problem…or so I thought.
But that wasn’t a problem for me. Along with my email account, Google also provides Bredemarket with Google Drive. While the contents of my Google Drive are private to the employees of Bredemarket (all 1 of us), I can designate individual files and folders for access by selected people.
So I set up a designated folder for my client’s access only, uploaded all the deliverables including the 100+ MB zip file to the designated folder, and provided my client’s contact with access.
I then told my client that all the deliverables were in the Google Drive folder and asked the client to let me know when they were downloaded.
Which is when I encountered my second problem.
For security reasons, the client’s IT department forbids employees from accessing unauthorized Google Drives.
So I jumped back to Plan A and emailed all the files to my client except for the one 100+ MB zip file.
Now I just had to get that zip file to the client.
That’s when I recalled the Dropbox account I set up for Bredemarket some time ago.
It was a quick process to upload the single 100+ MB zip file to a designated folder in Dropbox and give my client access.
But the client isn’t allowed to access Dropbox from work either.
By the time that my client was contacting his IT department for a possible fix, I realized the solution that you the reader probably realized several paragraphs ago.

Instead of emailing one zip file, why not email multiple zip files in multiple emails, with each zip file under Google’s 25 MB limit?
So I sent six emails to my client.
This FINALLY worked.
I should have divided and conquered in the first place.
Do you want Bredemarket to send you 100 megabytes of brochures, now that I know how to do it?
More importantly, do you want Bredemarket to send you a market/competitor analysis to your specifications?
Talk to Bredemarket and discuss your needs. Book a meeting with me at calendly.com/bredemarket. Be sure to fill out the information form so I can best help you.

On June 1, I shared a little piece on Bredemarket’s social media channels, including a post on the Bredemarket Technology Firm Services page on LinkedIn.
It was an announcement from Knell Computer.
Knell Computer announced Friday that it is eliminating wi-fi capabilities from its business computer product lines.
“At Knell Computer, we strongly believe that the best work occurs in a traditional office environment,” according to Gabriel Knell, CEO. “Since modern offices are fully equipped with Ethernet cabling, wi-fi is an unnecessary expense. Removal of wi-fi allows us to sell Knell Computers at a lower price point than our competitors, providing cost savings to our customers.”
Knell will promote this innovation with an ad campaign in major city downtown business districts, where it will attract the attention of real workers.
Gabriel Knell: “If you’re an amateur who performs so-called ‘work’ at home in your shorts, rather than from a true cubicle office environment, feel free to buy wi-fi computers from our competitors. We are embarrassed to see the Knell logo in a coffee shop—or in a converted bedroom.”
In a related announcement, Knell will incorporate technology that “red flags” the use of any Knell computer in a residential zone.

For those of you who don’t know much about Knell Computer, LinkedIn’s helpful AI feature provided contextual detail, including answers to critical questions:
All of these answers, sourced from information found in LinkedIn and on the Internet, were undoubtedly helpful.
But LinkedIn AI appears to have missed one teeny tiny thing.

Since I’m not engaged in full-time product marketing (although I perform some product marketing activities for my Bredemarket clients), I sometimes spend my time writing other things.
Like fake press releases for fake products from fake companies.
But I think that most of you figured out that Knell Computer and its head Gabriel Knell are based upon Dell Computer and its head Michael Dell.
(Note the “angelic” naming here. And no, I’m not naming anything after Lucifer.)
And most of you know why Dell Computer was suddenly in the news in May, and actually a little before that, as this Forbes article indicates.

Dell’s new remote-work policy will categorize its workers into two main groups: remote and hybrid.
Hybrid workers must agree to come into an “approved” office at least 39 days each quarter. This is roughly the equivalent of three days per week. Remote workers do not have to come into an approved office at all. However, remote workers aren’t eligible for promotion or to change jobs within the company.
According to the Register, Dell confirmed the 39 days/quarter requirement, and explained why it believed it was important.
In a statement, a Dell spokesperson told The Register, “We shared with team members our updated hybrid work policy. Team members in hybrid roles will be onsite at a Dell Technologies office at least 39 days per quarter (on average three days a week). In today’s global technology revolution, we believe in-person connections paired with a flexible approach are critical to drive innovation and value differentiation.”
But the Dell statement didn’t say HOW Dell would know who was in the office. The Register supplied that additional detail; Dell was reported to use tracking and color coding.
Starting next Monday, May 13, the enterprise hardware slinger plans to make weekly site visit data from its badge tracking available to employees through the corporation’s human capital management software…
Let me just pause right there. Any time that you read something about “human capital management,” your antennae should go up.
But let’s get back to how Dell is managing its carbon-based capital.
…and to give them color-coded ratings that summarize their status. Those ratings are:
Blue flag indicates “consistent onsite presence”
Green flag indicates “regular onsite presence”
Yellow flag indicates “some onsite presence”
Red flag indicates “limited onsite presence”

So that was the situation as of June 1 when Knell Computer issued its press release, complete with “red flag” capability.
I’m forced to confess that Knell Computer’s product marketing efforts didn’t really make an impact. (I KNEW I should have included the press release in the Bredemarket blog. Better late than never.)
But Dell Computer’s efforts truly impacted its employees…but not in the way that Dell Computer wanted.
No, not the Steve Taylor song.
The Dell human capital management method that ranked hybrid employees based upon their willingness to work in the office.
A few weeks after Knell Computer’s product marketing effort, stories began to emerge about what was happening at the real Dell. Here’s part of what Ars Technica said on June 20:
Dell announced a new return-to-office initiative earlier this year. In the new plan, workers had to classify themselves as remote or hybrid.
Those who classified themselves as hybrid are subject to a tracking system….
Alternatively, by classifying themselves as remote, workers agree they can no longer be promoted or hired into new roles within the company.
Business Insider claims it has seen internal Dell tracking data that reveals nearly 50 percent of the workforce opted to accept the consequences of staying remote, undermining Dell’s plan to restore its in-office culture.
“But wait!” you’re saying. “So many people are willing to forgo promotion at Dell, or even to apply to new positions at Dell?”
Yes. Because here’s a dirty little secret:
Dell employees can leave Dell and work for other companies.
Granted many other companies aren’t remote-friendly either (believe me, I know), but those that are have an opportunity to scoop up Dell’s best and brightest.
And as the Dell workers leave, this provides an opportunity for yours truly. After all, I’d be happy to report to Dell’s office in Ontario, California. So I went to see what opportunities I’d have.
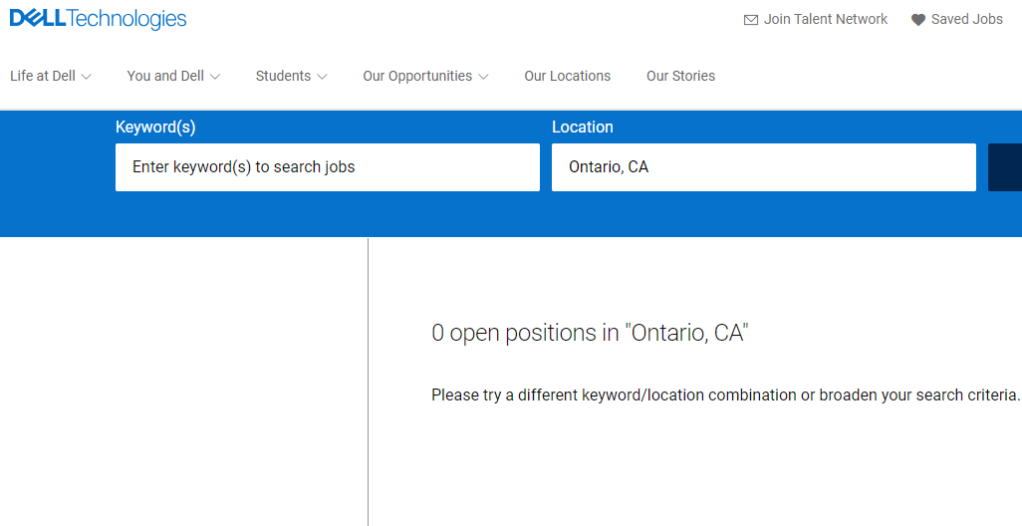
It turns out that Ontario, California is not one of Dell’s officially approved hybrid work locations. I’d have to drive to Utah, Texas, or Oklahoma three days a week.
But hey, I’m not the only marketer affected by Dell’s work policies. Silicon Valley marketers can’t work hybrid at Dell either.
I’ll continue to monitor how this plays out. Perhaps Knell Computer may issue a second press release.
Which LinkedIn AI will take as the truth.
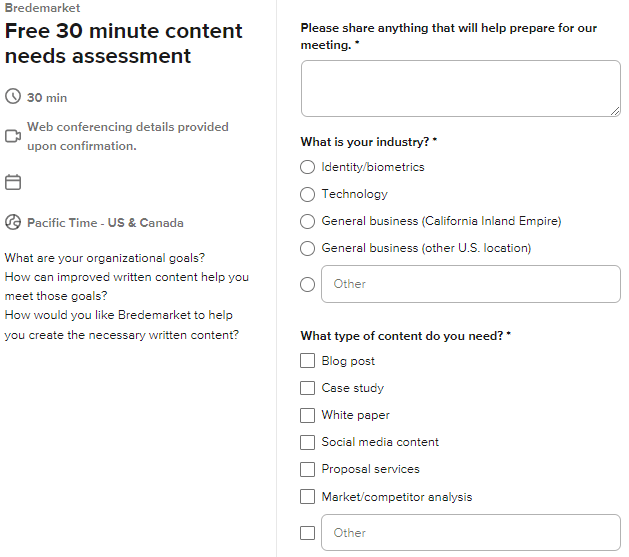
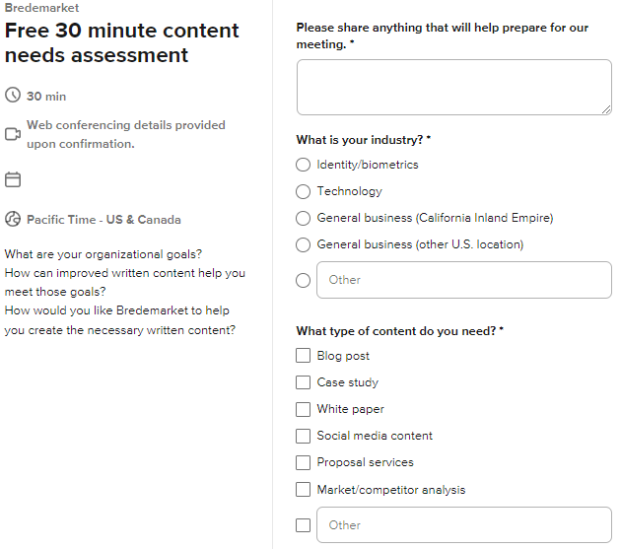
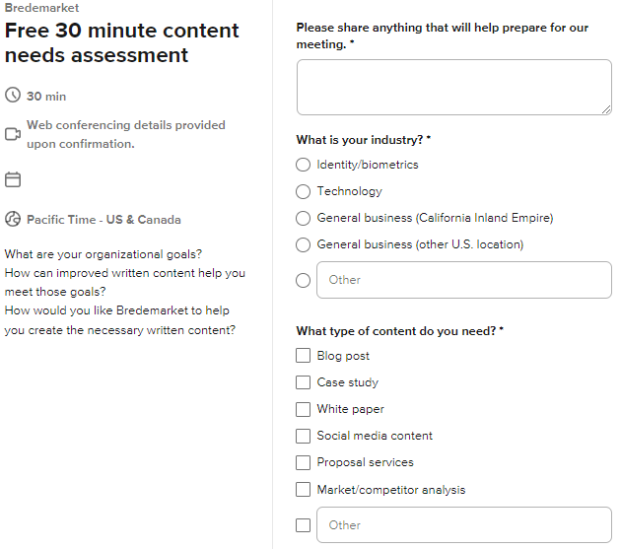
If you book a free 30 minute meeting with Bredemarket, you’ll now find an additional option in the “What Type of Content Do You Need?” section: Market/competitor analysis. I’ve done these for years, but never added the option to the form.
My analyses ONLY use publicly available information that is NOT subject to NDA. So you won’t get access to the analyses I’ve performed for other clients, and they won’t get access to the analysis I prepare for you.
While I primarily provide these analyses in the identity/biometrics industry, I’m open to discussing analysis needs in other industries.
Book a meeting to discuss your content needs.