Bredemarket spends a lot of its time on competitive analysis, either as part of client projects, or for my own personal edification. For example, right now I’m working on a client project and analyzing 20 of the client’s competitors in over 20 markets serving hundreds of customers.
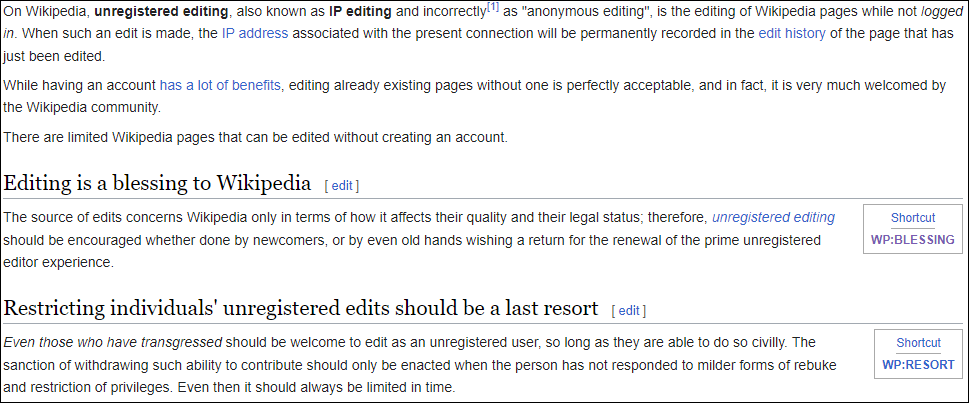
But when I perform competitive analysis, I use entirely ethical and legal methods to obtain my competitive information. Nothing clandestine that will get me in trouble.

But sometimes the well of competitive information goes dry. Companies go silent and then come back, with no explanation of why its former communications were…um…incomplete.
Of course, I don’t know why a particular company suddenly decides that prospect/customer communication isn’t critically important.
But this got me thinking. How often DO companies go silent?
And I had an excellent way to conduct a mini-survey and find out.
Are the 40+ blogging identity firms still blogging?
Back in September, I identified over 40 identity firms that were blogging, some more frequently than others. Blogging provides quantifiable benefits, and these companies were obviously taking advantage of those benefits.

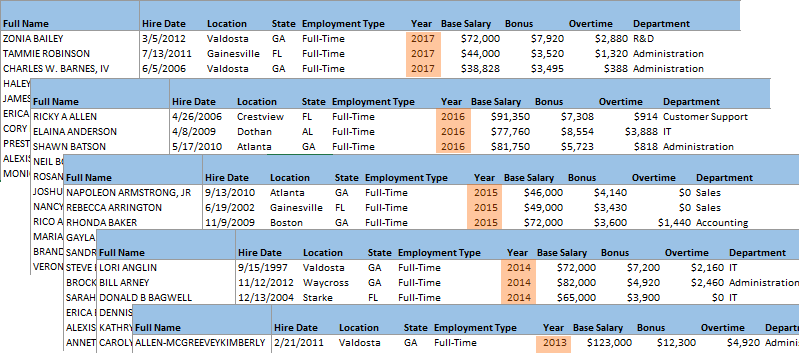
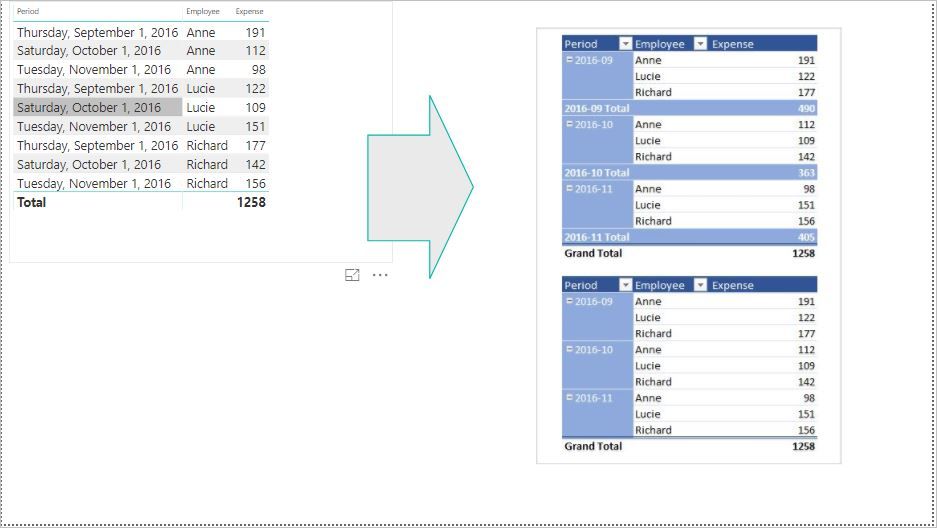
But that was back in September. How many of those companies were still actively blogging in mid-December? I wanted to find out, so I conducted a mini-survey of those identity blogs. Of the 40+ companies whose blogs and articles had identifiable posting dates:
- 21 had blogged at least once this month (December).
- 11 had last blogged in November.
- 3 had last blogged in October.
- 7 hadn’t blogged since the 3rd calendar quarter of 2023 (July – September).
- 4 hadn’t blogged since the 2nd calendar quarter (April – June).
- 1 hadn’t blogged since the 1st calendar quarter (January – March).
- 1 hadn’t blogged at all in 2023. Perhaps it forgot it had a blog, or a former employee never surrendered the password.

My mini-survey shows that of the 40+ identity firms with blogs, about one-third of them HAVEN’T SAID A SINGLE THING to their prospects and customers in the last two months.
Is your firm failing to engage in identity blog post writing, even though you have a blog?
But what about other communications?
To be fair, this is not a complete measure of corporate content marketing. While some of these companies hadn’t blogged on their own websites, they HAD communicated on Instagram (Mark Zuckerberg’s website), LinkedIn (Satya Nadella’s website), X (Elon Musk’s website), YouTube (Sundar Pichai’s website), and other websites controlled by other people. Great traffic for Zuck et al…not so great traffic for the companies.
More importantly, some of these companies communicate via email, which is a great way to find out what the company is doing…if the company has your email address.
If the company doesn’t have your email address, and if it isn’t blogging, then it’s going to be hard for prospects to find company information.
So why is your identity firm ignoring your customers?
Some identity companies with blogs and similar mechanisms are consciously making the choice to NOT communicate with their prospects and customers.
Why not?
There are many reasons. Here are five reasons that Full Funnel identified.
- A couple of them have already been addressed by Bredemarket, such as “we don’t have the time.” (Bredemarket has the time.)
- But I would like to dive into Full Funnel’s fourth reason: “we don’t have anything to say.” I encourage you to read Full Funnel’s response to that objection, because I agree with it. Your firm MUST have something to say if it wants to differentiate itself and remain viable. If you don’t have anything to say, prospects will go to your more talkative competitors.
When is your identity company going to start communicating with your prospects and customers?
If your identity company has fallen down on the blogging front, it’s best to restart the process as soon as possible. As I’ve said before, content marketing doesn’t yield immediate results. A particular piece of content may not result in a sale until six or twelve months later, or longer. Delaying the implementation simply delays the benefits I mentioned above.
So if your identity company is failing to reach your prospects and customers with content, why don’t you talk with Bredemarket now and develop a plan to reach them?
Yes, I know we’re right in the middle of the holidays, and some of you will put this off until next week, or probably the week after next.
For me, that’s just as well. That gives me more time to talk to your competitors and get their content process moving.
If you DON’T want your competitors to get in line ahead of you, click the image below and schedule a meeting. I’m available this week and most of next week.