In the ideal world, when a writer such as me begins to work with your firm, the firm hands me a brand book that explains exactly how I am supposed to communicate when writing for your firm.
In the real world, this rarely happens, if ever.
But I’m smart enough to know that you don’t want me to write in the same style that I use in the Bredemarket blog.
So I ask questions, addressed both to you and to your existing content.
While I don’t officially create a real “brand book” out of thin air, the answers to these questions guide me as I create your content. I may include your founding story (someone broke into my house when I wasn’t home), your love of sports (football, or perhaps football), or your prospects’ most pressing needs.
My goal is to be you…whoever you are.
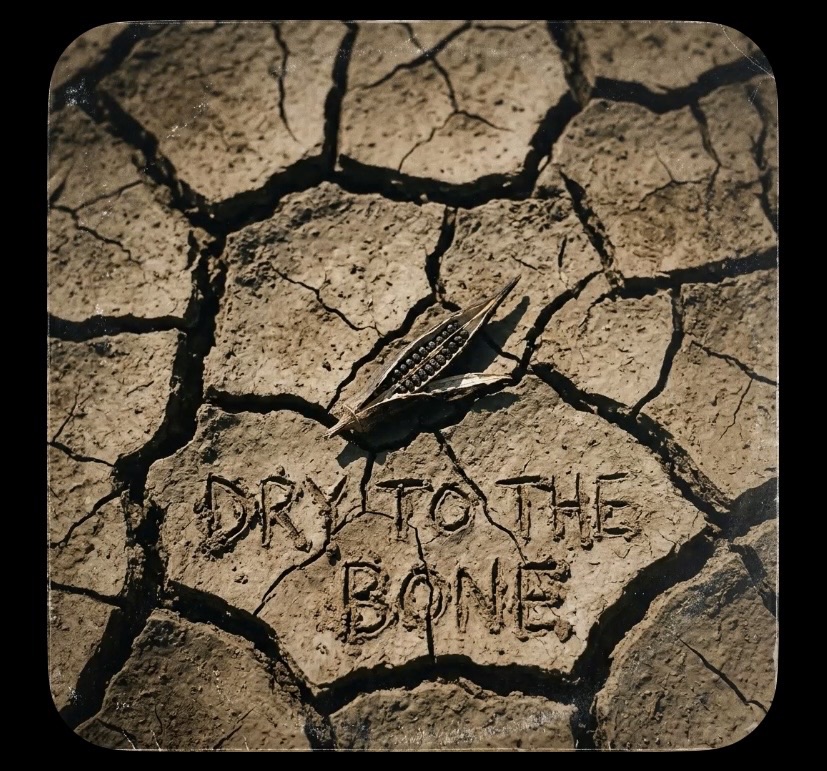
P.S. Speaking of books, might as well flog mine.