Warning: this post discusses sexual assault and child abuse.

The Hippocratic Oath imposes duties on medical professionals, including this one:
I will follow that system of regimen which, according to my ability and judgment, I consider for the benefit of my patients, and abstain from whatever is deleterious and mischievous.
From https://www.health.harvard.edu/blog/first-do-no-harm-201510138421.
For people like me who do not use the word “deleterious” on a daily basis, it means “harmful often in a subtle or unexpected way.”
The dictates of the Hippocratic Oath lead us to forensic nursing (as defined by 1NURSE.COM), the invasive nature of some forensic techniques, and what companies such as Foster+Freeman are doing to minimize invasive evidence capture.
What is forensic nursing?

As 1NURSE.COM notes, forensic nursing is multidisciplinary, operating “at the critical juncture of medical science and the legal system.”
Forensic nursing is a specialized branch that integrates medical expertise with forensic science to provide comprehensive care for individuals impacted by violence, abuse, or criminal activities. These professionals serve as a crucial link between the realms of healthcare and the legal system, collaborating with law enforcement, attorneys, and other professionals to gather evidence, provide expert testimony, and ensure justice for victims.
From https://www.linkedin.com/pulse/forensic-nursing-exploration-intricate-profession-1nurse-com-iedyc/.
When I started my forensic career 29 years ago, I was solely involved in the capture and processing of fingerprints from criminals. If I may be honest, the well-being of the individual who provided the forensic evidence was NOT an overriding concern.
But within a year or two I started to get involved in the capture and processing of fingerprints from NON-criminals who were applying for and receiving government benefits.
- For that market we HAD to concern ourselves with the well-being of our clients, to make fingerprint capture as easy as possible, and to treat our clients with the utmost respect.
- In the end it didn’t matter, because in the popular mind fingerprinting was associated with criminals, and benefits recipients didn’t want to be treated like criminals no matter how nice we were. To my knowledge, all of the benefits recipient fingerprint programs in the United States have all ceased.
Forensic nursing needs to gather the necessary forensic evidence while preserving the compassionate care that nurses are required to provide.
Invasive forensic techniques
So if we have to take care when gathering information from benefits recipients, imagine the level of care we need to take when gathering information from crime victims. Returning to 1NURSE.COM’s article, here are two of the tasks that forensic nurses must perform:
Sexual Assault Forensics: Specializing in sexual assault examination, forensic nurses provide not only compassionate care but also play a pivotal role in collecting evidence essential for legal proceedings. Their expertise ensures a sensitive approach while preserving the integrity of forensic evidence. Example: A forensic nurse conducting a sexual assault examination may collect biological samples and document injuries to aid in prosecuting the assailant.
Child Abuse Investigation: Forensic nurses are instrumental in assessing and documenting cases of child abuse. They collaborate with child protective services and law enforcement to ensure the safety and well-being of the child. Example: A forensic nurse working on a child abuse case may conduct a thorough examination to document injuries and provide expert testimony in court.
From https://www.linkedin.com/pulse/forensic-nursing-exploration-intricate-profession-1nurse-com-iedyc/.
The “compassionate care” part is important, as Foster+Freeman notes in a separate article:
We have focussed a lot on how the investigation works when looking for crimes of a distressing nature but not actually how this investigation process can affect the victim of these crimes and put the victim first. This period can be incredibly distressing for the victim, and the investigation can make this worse as it is making the victim re-live this experience.
https://www.linkedin.com/pulse/victim-first-forensics-focusing-victims-crime-foster-freeman-gnw6e/
As part of their duties, the forensic nurse has to capture evidence from the very parts of the body that were assaulted during the abuse crime itself. No one wants to go through that again. How can evidence capture be less invasive?
Three ways to minimize invasive evidence capture
While it’s not possible to completely erase the pain that crime victims suffer during a forensic investigation, there are ways to minimize it. The Foster+Freeman article highlights three ways to do this:
- Capture evidence via non-invasive techniques. As a supplier of alternate light source (ALS) technology, Foster+Freeman notes that its products can discover evidence, even at the subdermal layers, without touching the victim. “Using an ALS is a non-invasive and non-destructive way to examine potential evidence on the skin. This is especially important when dealing with fragile or sensitive skin, as it minimizes the risk of causing further harm during the examination process.”
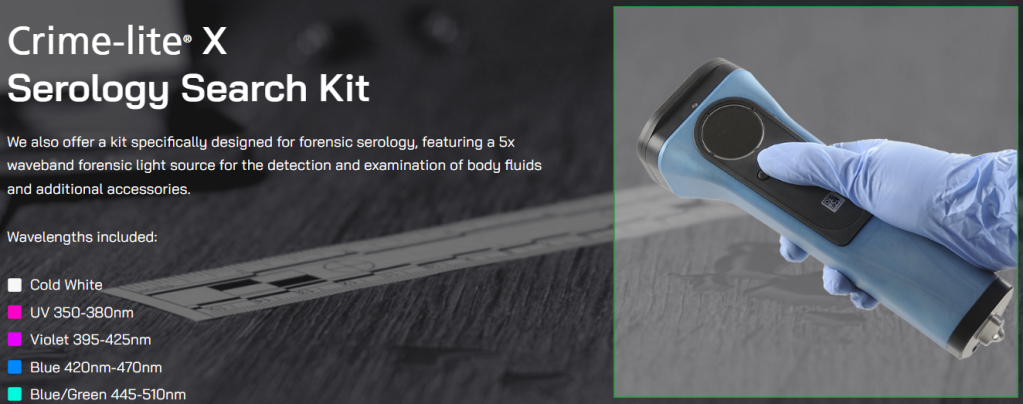
- Capture evidence quickly. Forensic nurses do not want to prolong an examination. There are ways to gather evidence as quickly as possible. For example, rather than using multiple ALS devices, you can use a single one; Foster+Freeman’s Crime-lite® X Serology Search Kit is “a multispectral light source that has been made with five wavelengths of light integrated into one unit.”
- Capture evidence thoroughly. What’s the point of putting a victim through the trauma of evidence capture if it doesn’t result in a conviction? Because of this, it’s important to capture as much evidence as possible. A variety of alternate light sources accomplishes this.
Foster+Freeman is just one of a multifarious array of companies that supply evidence collection solutions to forensic nurses and other forensic professionals.
And no, Foster+Freeman didn’t sponsor this post, although Bredemarket is available to provide writing services to Foster+Freeman or to other companies who need to drive content results.
And now that I’ve successfully used “multifarious,” I need to find a way to use “deleterious.” Keep your eyes open.