Initialism
I have been amused by press releases for many years.
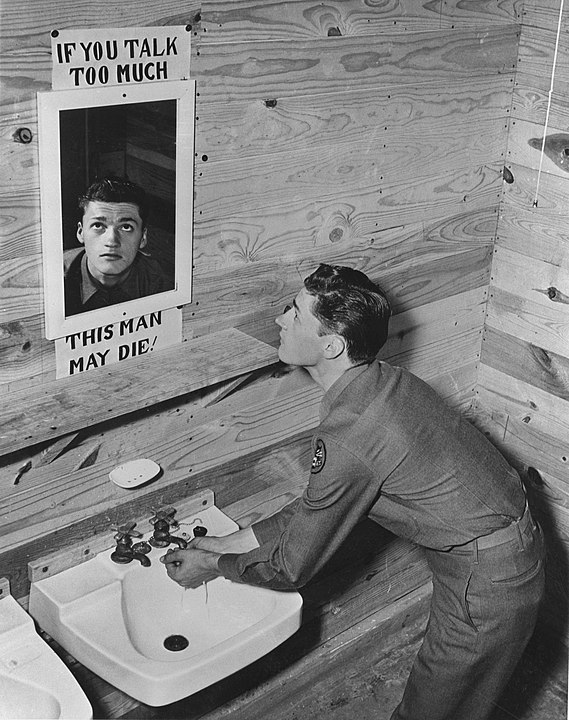
You’re reading along in the press release and then you get to a quote from an executive with the company issuing the press release.
“MegaCorp’s new best-of-breed revolutionary platform will increase artificial intelligence synergies and optimize blockchain outcomes,” said Silas Phelps, Chief Executive Officer and Strategist at MegaCorp. “Did I mention pickleball?” he added.
Sometimes the executive has even read the quote before publication. Or maybe not. Because in most cases the quote was written by someone else.
Inner Stall

I was amused by this practice so much that when I wrote a press release for a side project of mine in 2017, I called out the practice.
The marketing flack who is pretending to speak for Ontario Emperor put some new words in his mouth for this release. “Yes, I am self-proclaiming this to be the greatest electronic album ever,” stated Ontario. “And in all honesty, the songs are more developed than the ones on my previous releases. Each of the twelve songs evokes a particular mood, although I will leave it to the listener to determine what these moods may be.”
Empoprises’ John E. Bredehoft also had some words put into his mouth. “Our experience with Bandcamp has been very fruitful,” Bredehoft supposedly said. “We look forward to expanding our relationship with Bandcamp in the future.”
As an aside, the Ontario Emperor electronic album “Drains to Ocean” is still available for purchase ($8 “or more”) at https://ontarioemperor.bandcamp.com/album/drains-to-ocean. Or you can save yourself some money and listen to one of the songs, “For a Meaningful Apocryphal Animation,” for FREE by scrolling to the bottom of Bredemarket’s “Information” page. (And to the bottom of this post.)
One more aside that may be of interest to a few of you: the drain pictured above is a few buildings west of IDEMIA’s LaPalma office in Anaheim Hills.
But years later, the whole thing became less of a joke.
Climbing
Why?
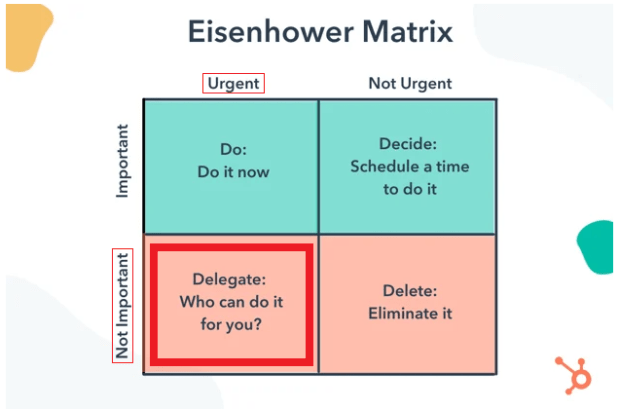
Because one of Bredemarket’s clients required a draft press release, and I wrote the first draft, including quotes from “Executive X.”
Now I didn’t make these quotes up out of whole cloth, taking them from an internal client document.
But Executive X thought they were a little off, so the executive, myself, and a third person got together to hammer out a new quote that was more in line with something Executive X would say.
And I’m glad we did. Even though the vast majority of people who read the press release never knew Executive X, those who did know the executive would be pleased with the quote. Hopefully it sounded somewhat more authentic than the usual run-of-the-mill quotes found in press releases.
I stubbornly think that readers will reward authenticity someday. At least the good readers will.
But I failed in one respect. I didn’t create an apocryphal animation to go with the quote. But that’s a topic for another time.