I’ll confess: there is a cybersecurity threat so…um…threatening that I didn’t even want to think about it.
You know the drill. The bad people use technology to come up with some security threat, and then the good people use technology to thwart it.
That’s what happens with antivirus. That’s what happens with deepfakes.
But I kept on hearing rumblings about a threat that would make all this obsolete.
The quantum threat and the possible 2029 “Q Day”
Today’s Q word is “quantum.”
But with great power comes great irresponsibility. Gartner said it:
“By 2029, ‘advances in quantum computing will make conventional asymmetric cryptography unsafe to use,’ Gartner said in a study.”
Frankly, this frightened me. Think of the possibilities that come from calculation superpowers. Brute force generation of passcodes, passwords, fingerprints, faces, ID cards, or whatever is necessary to hack into a security system. A billion different combinations? No problem.
So much for your unbreakable security system.
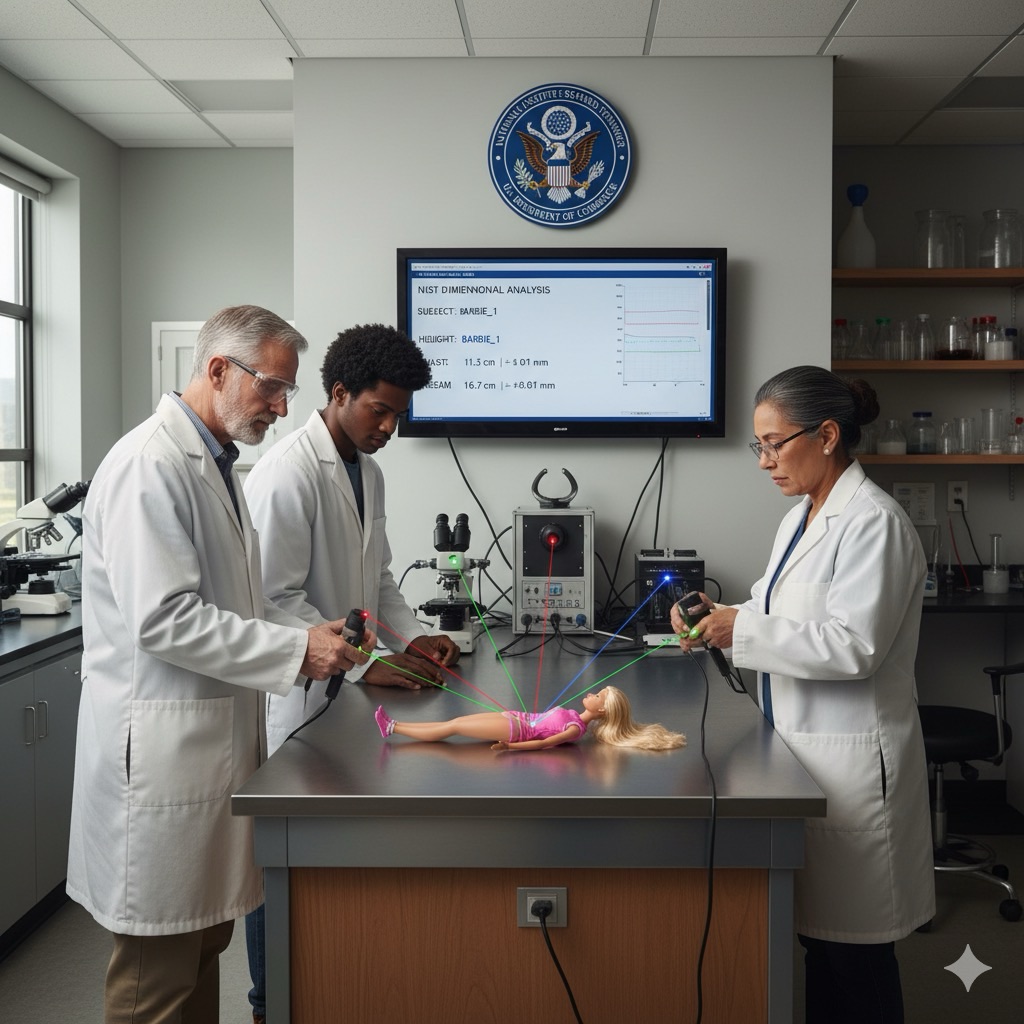
Thales implementation of NIST FIPS 204
Unless Thales has started to solve the problem. This is what Thales said:
“The good news is that technology companies, governments and standards agencies are well aware of the deadline. They are working on defensive strategies to meet the challenge — inventing cryptographic algorithms that run not just on quantum computers but on today’s conventional components.
“This technology has a name: post-quantum cryptography.
“There have already been notable breakthroughs. In the last few days, Thales launched a quantum-resistant smartcard: MultiApp 5.2 Premium PQC. It is the first smartcard to be certified by ANSSI, France’s national cybersecurity agency.
“The product uses new generation cryptographic signatures to protect electronic ID cards, health cards, driving licences and more from attacks by quantum computers.”
So what’s so special about the technology in the MultiApp 5.2 Premium PQC?
Thales used the NIST “FIPS 204 standard to define a digital signature algorithm for a new quantum-resistant smartcard: MultiApp 5.2 Premium PQC.”

The NIST FIPS 204 standard, “Module-Lattice-Based Digital Signature Standard,” can be found here. This is the abstract:
“Digital signatures are used to detect unauthorized modifications to data and to authenticate the identity of the signatory. In addition, the recipient of signed data can use a digital signature as evidence in demonstrating to a third party that the signature was, in fact, generated by the claimed signatory. This is known as non-repudiation since the signatory cannot easily repudiate the signature at a later time. This standard specifies ML-DSA, a set of algorithms that can be used to generate and verify digital signatures. ML-DSA is believed to be secure, even against adversaries in possession of a large-scale quantum computer.”
ML-DSA stands for “Module-Lattice-Based Digital Signature Algorithm.”

Now I’ll admit I don’t know a lattice from a vertical fence post, especially when it comes to quantum computing, so I’ll have to take NIST’s word for it that modules and lattice are super-good security.
Certification, schmertification
The Thales technology was then tested by researchers to determine its Evaluation Assurance Level (EAL). The result? “Thales’ product won EAL6+ certification (the highest is EAL7).” (TechTarget explains the 7 evaluation assurance levels here.)
France’s national cybersecurity agency (ANSSI) then certified it.
However…
…remember that certifications mean squat.
For all we know, the fraudsters have already broken the protections in the FIPS 204 standard.

And the merry-go-round between fraudsters and fraud fighters continues.
If you need help spreading the word about YOUR anti-fraud solution, quantum or otherwise, schedule a free meeting with Bredemarket.