(Part of the biometric product marketing expert series)

We’ll get to Bob a little later. But let me start off by telling you something.
AAABWTCI.
That stands for “acronyms are a bad way to convey information.”
But you didn’t know that.
Many of us like to use acronyms to quickly convey information, but we need to remember that different people use acronyms in different ways.
For example, in my circles, people generally understand “FBI” to refer to the United States Federal Bureau of Investigation.

But try telling that to the Faith Bible Institute, or to an employee of Frontier Booking International. (I’ll admit that the founder of the latter company, Ian Copeland, chose the company name deliberately. After all, his brother Miles founded I.R.S. Records, and their father worked for the Central Intelligence Agency.)
It’s best not to use acronyms at all and instead use full words. Because if you use full words, then (as Ed McMahon would say) you will ensure that EVERYONE knows exactly what you mean.

Allow me to play the Johnny Carson role and say that Ed was WRONG.

After all, the great English philosopher Robert Plant (I told you we’d get to Bob eventually) noted,
“You know sometimes words have two meanings.”
“Stairway to Heaven.” https://genius.com/Led-zeppelin-stairway-to-heaven-lyrics
Take the word “biometrics.” In my circles, people generally understand “biometrics” to refer to one of several ways to identify an individual.

But for the folks at Merriam-Webster, this is only a secondary definition of the word “biometrics.” From their perspective, biometrics is primarily biometry, which can refer to “the statistical analysis of biological observations and phenomena” or to “measurement (as by ultrasound or MRI) of living tissue or bodily structures.” In other words, someone’s health, not someone’s identity.
Fun fact: if you go to the International Biometric Society and ask it for its opinion on the most recent FRVT 1:N tests, it won’t have an answer for you.
The terms “Biometrics” and “Biometry” have been used since early in the 20th century to refer to the field of development of statistical and mathematical methods applicable to data analysis problems in the biological sciences.
Recently, the term “Biometrics” has also been used to refer to the emerging field of technology devoted to the identification of individuals using biological traits, such as those based on retinal or iris scanning, fingerprints, or face recognition. Neither the journal “Biometrics” nor the International Biometric Society is engaged in research, marketing, or reporting related to this technology. Likewise, the editors and staff of the journal are not knowledgeable in this area.
From https://www.biometricsociety.org/about/what-is-biometry
This can confuse people when I refer to myself as a biometric proposal writing expert or a biometric content marketing expert. I’ve been approached by people who wanted my expertise, but who walked away disappointed that I had never written about a clinical trial.
Despite this, there are some parallels between biometrics and biometrics. After all, both biometrics and biometrics take body measurements (albeit for different reasons), and therefore some devices that can be used for biometry can sometimes also be used for identification, and vice versa.
But only sometimes. Your run-of-the-mill optical fingerprint reader won’t contribute to any medical diagnosis, and I’m still on the fence regarding whether brain waves can be used to identify individuals. I need a sample size larger than 50 people before I’ll claim brain waves as a reliable biometric.
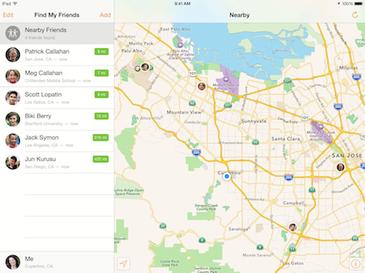
Of course, a biometric device such as an Apple Watch can not only measure your biometrics, but also your geolocation, which is another authentication factor.