As many of my readers know, there are a variety of ways for people to individually identify themselves.
The National Institute of Standards and Technology recognizes three of these authentication factors:
- The most commonly known authentication factor is “something you know.” This includes such items as passwords, personal identification numbers (PINs), and the name of your childhood pet. This authentication factor is very common and very controversial, to the point where some want to eliminate it altogether. (I don’t.)
- Another authentication factor that I know very well is “something you are.” Biometrics such as fingerprint identification and facial recognition falls into this category, as well as gait recognition, “behavioral biometrics,” and other biometric identifiers.
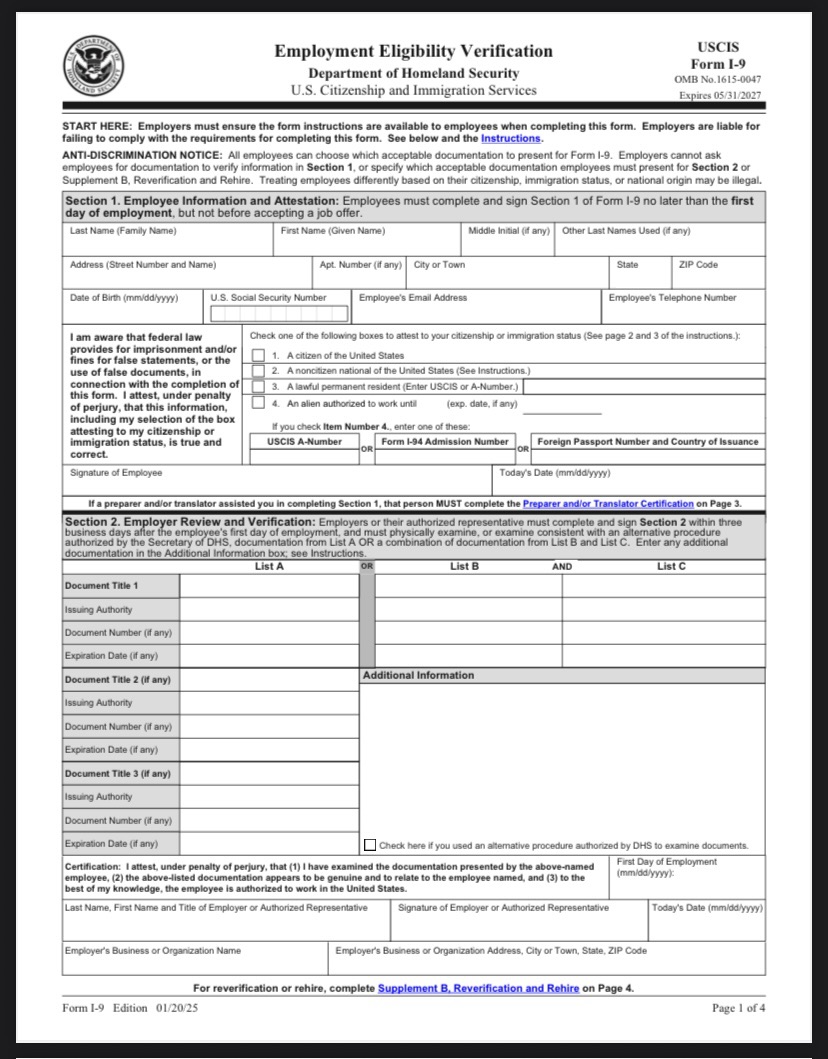
- The third authentication factor that NIST recognizes is “something you have.” This could be a driver’s license, a passport, a key fob, a smartphone, or perhaps a digital identity application.
But those aren’t the only authentication factors. Two others have been identified, as I have previously noted.
- “Something you do” differs from both gait recognition and behavioral biometrics, because this is not an inherent property of your being, but is a deliberate set of actions on your part. For example, you could gain access to a nuclear facility by putting your left foot in, putting your left foot out, putting your left foot, in and shaking it all about. Note, however, that this particular “something you do” is as common as the password “12345” and should be avoided.
- And the fifth factor is “somewhere you are.” For example, if I am buying something at a a store in Virginia, but I am physically in California, something appears to be wrong.
OK, that’s it. End of post. Those are the five authentication factors. There aren’t any more, and there never will be any more. Oh sure, you could come up with a sixth authentication factor, but chances are that it would map into one of the five existing authentication factors.
Or maybe not.
Why?
I’d like to propose a sixth authentication factor.
What about the authentication factor “why”?
This proposed factor, separate from the other factors, applies a test of intent or reasonableness to any identification request.
Let me give you an example. Assume for the moment that I am at a McDonald’s in Atlantic City and want to use my brand new credit card to buy some healthy Irish cuisine.
You could, of course, apply the existing authentication factors to this transaction:
- I physically have the credit card.
- I know the PIN that is associated with the credit card.
- My face matches the face of the person who owns the credit card.
- I am physically at the McDonald’s where the food is for sale, and I physically have a hotel key associated with a nearby hotel, and I physically have a badge associated with a trade show in the city. (The latter two facts are actually a combination of “something you have” and “somewhere you are,” but I threw them here for the fun of it.)
- If my credit card company has implemented it, I can perform the super secret finger pattern (or hokey pokey dance) associated with this account.
But even if all of these factors are authenticated, or even if some of them are not, does it make sense that I would be purchasing a meal at a McDonald’s in Atlantic City?
- Did I recently book a flight and fly from my California home to Atlantic City? This could explain “why” I was there.
- Is it lunchtime? This could explain “why” I was making this transaction.
- Is my stomach growling? This could indicate that I am hungry, and could explain “why” I was at such a fine food establishment.
Admittedly, employing data warehousing and artificial intelligence to use the “why” factor to authenticate a small fast food purchase is overkill, just like it’s overkill to require three biometric identifiers and a passport to open a physical mailbox.
But perhaps use of such an authentication factor would be appropriate at a critical infrastructure facility such as a nuclear power plant.
Assume for the moment that I am a double agent, employed the the U.S. Department of Energy but secretly a spy for an enemy country. All of the five authentication factors check out, and I am the person who is authorized to visit a particular nuclear power plant.
But why am I there?
Am I there for some regular U.S. Department of Energy business that is totally above board?
Or am I there for some other unknown reason, such as theft of secrets or even sabotage?
How to implement the “why?” authentication factor
I believe that a “why?” authentication factor could be very powerful, but it would take some effort to implement it.
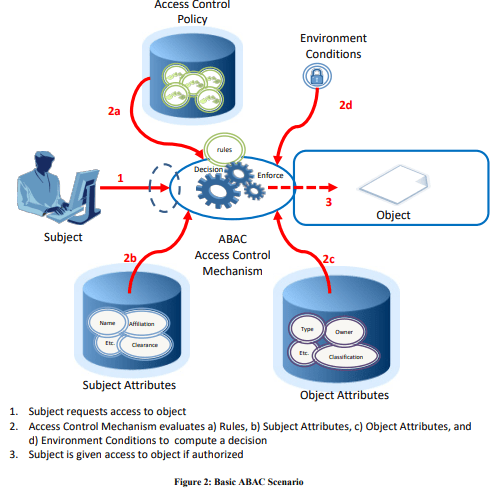
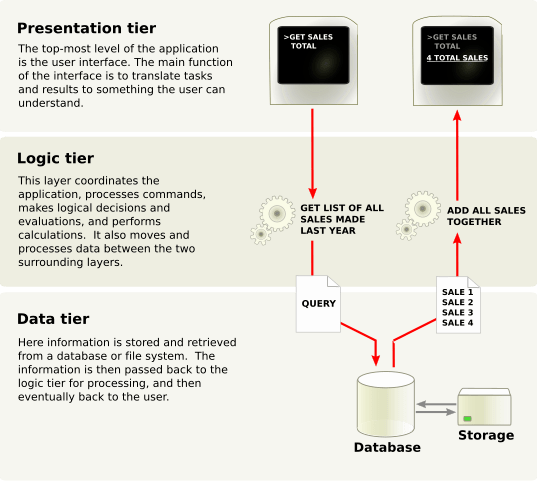
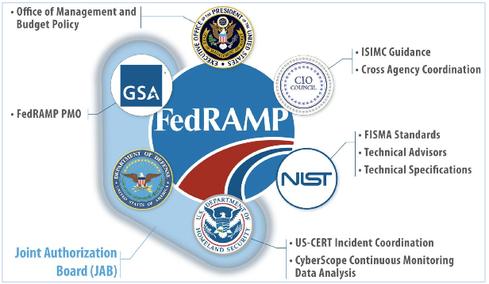
First, the authentication system would have to access all the relevant data. In the McDonald’s example above, that includes (a) my flight data, (b) the time of day, and (c) my health data (“biometrics” in the broader sense). In the nuclear power plant example, the authentication system would have to know things such as nuclear power plant inspection schedules, trip authorizations from my supervisor, and other data that would indicate a reason for me to be at the plant. That’s a lot of data.
Second, the authentication system would have to process all the relevant data to glean knowledge from it. By itself, the data points “United Flight 123 from Ontario to Atlantic City yesterday,” “1:30 pm,” and “haven’t eaten in six hours” do not allow the system to make an authentication decision.
Third, the authentication system would have to collect and protect that mass of data in a way that protects my privacy and the privacy of others. In the United States at present, this is where the whole system would probably fall apart. While a whole bunch of data is collected about us and placed in silos (the TSA-airline silo, for example), putting it all together could be pretty scary to some. Although certain lawyers in Illinois would love the moneymaking opportunities that such a system could provide via Illinois Biometric Information Privacy Act lawsuits.
So a complete implementation of the “why” authentication factor is probably impossible for now, due to both technical and societal constraints.
But is it possible to implement a subset of the “why” authentication factor? For example, since a company presumably has access to employee corporate travel schedules, could the company use the knowledge of an employee’s flight from Chicago to Los Angeles on Sunday to provide the employee with physical access to the firm’s Southern California office on Monday?
Something to think about.
Maybe I should speak to a patent attorney.