I intentionally chose an obscure title for this post.
I could have entitled the post “Ricardo Montalban.” Just because.
In a more relevant way, I could have entitled the post “Former IDEMIA employee weighs in on Advent’s possible sale of the company.” That would have got some clicks, to be sure.
But it would have misled the reader, because the reader would have gotten the idea that I have some expertise in corporate acquisitions, and an abillity to predict them.
And as past history has shown, I do not have any such expertise.
- In 2000, I was completely and totally surprised when I learned that Printrak wanted to sell itself to Motorola. I didn’t have a clue that any such thing was going to happen.
- In 2008, I was reading online late one evening and was completely and totally surprised when I learned that Motorola wanted to sell off half of Printrak to the French company Safran, the Sagem Morpho folks. Yes, Motorola was in trouble, but I didn’t have any idea that we would be sold off.
- Years later, I was kinda sorta surprised when Safran decided that it wanted to get rid of its entire identity and security business, and was completely and totally surprised when the buyer was an American investment firm that owned Oberthur Technologies.
So my record on really understanding these acquisitions is pretty low.
With that caveat, I’ll go ahead and use a really eye-catching SUBtitle. Better late than never.
Impressive, isn’t it?
But before proceeding, I should let you know about THAT Reuters article that I referenced in the real post title.
On Friday, Reuters published an exclusive article entitled “Advent gears up for $4.6 bln sale of French biometrics firm IDEMIA – sources.”
So who is Advent?
Advent (actually, Advent International) is the American investment firm that I mentioned earlier. As an investment firm, its purpose in life is to buy businesses, improve them, and sell them for a profit.
Back in 2011, Advent bought Oberthur Technologies with this intent. To that end, Advent announced in 2015 that Oberthur Technologies planned an Initial Public Offering. Within a month, those plans were shelved. Advent determined that an Oberthur IPO wouldn’t do so well.
So Advent began thinking about ways to make Oberthur more attractive.
At the same time, Safran was trying to decide what to do with its identity and security business. The purchase of Printrak was just a blip in Safran’s plans, as it acquired L-1 Identity Solutions (renamed MorphoTrust) and other businesses. But Safran is not an identity and security company. It’s a “de plane” company.
And Safran is also a defense company to protect France and other countries from evil forces.
The identity part of the business was clearly the odd one out. Heck, rich Corinthian leather would have fit better into the Safran product line.
OK, I’ll stop now.
Anyway, in the end Advent announced in 2016 that it had entered into an agreement to negotiate the purchase of Safran’s identity and security business. The purchase was completed on May 31, 2017, and Advent combined Oberthur (OT) and the portion of Safran (Morpho) into OT-Morpho, which was quickly renamed IDEMIA.
I was an employee of IDEMIA at the time, and I don’t think I’m spilling any company secrets if I reveal that Advent wanted IDEMIA to do really really well, so that it could make a profit on the two acquisitions. I wasn’t at the highest executive level that was setting the high-level strategy, but I was often working on initiatives to help realize Advent’s profitability goal.
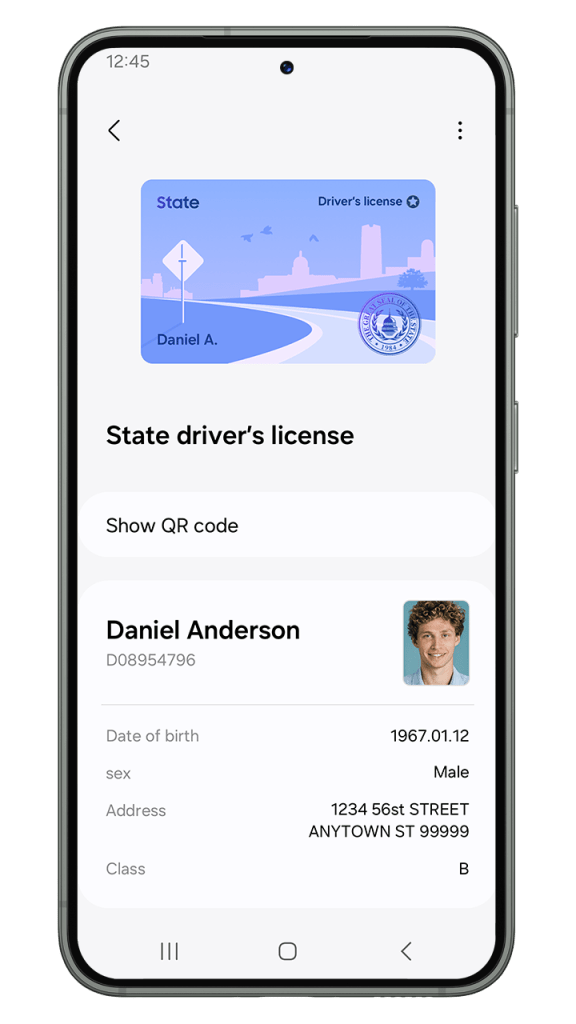
The possibility of an IDEMIA IPO or sale receded somewhat in early 2020. Among other things, COVID adversely affected two of IDEMIA’s core businesses in the United States, TSA PreCheck (nobody was flying) and driver’s licenses (the DMV offices were all closed).
Back to THAT Reuters article
Fast forward to 2022 and Reuters’ exclusive revelations.
Advent International is looking to sell its French biometrics and fingerprint identification firm IDEMIA in a deal worth up to $4.6 billion as it seeks to capitalise on growing demand for cybersecurity assets in Europe, two sources told Reuters.
The U.S. buyout fund is reviewing a series of options to sell IDEMIA, including a possible break-up of the company which was formed in 2016 by combining Safran’s identity and security business with Oberthur Technologies, the sources said.
From https://www.reuters.com/business/exclusive-advent-gears-up-46-bln-sale-french-biometrics-firm-idemia-sources-2022-02-04/
As you, the wise reader, know, Reuters goofed here.
IDEMIA was NOT formed in 2016. The formation of IDEMIA was ANNOUNCED in 2016, but the deal wasn’t actually COMPLETED until 2017. Hey, at least Biometric Update got it right.
Anyway, if you read either Reuters or Biometric Update, you’ll learn that nothing is going to happen immediately (France is holding an election in April, and the composition of the new government could impact any sale), and that the possible split-up may separate the part of the business that sells to governments from the part that sells to commercial firms.
Of course, the big question about any sale of IDEMIA would be the identity of the buyer. Would Advent try (again) to issue an IPO, or would Advent look for one or more existing companies to purchase IDEMIA?
Both Reuters and Biometric Updare speculate that Thales could be a potential buyer. While Safran was slimming down to concentrate on its aircraft business, Thales has been beefing to to diversify its business, most notably in its purchase of Gemalto. (As people in my industry know, that purchase provided Thales with the technology of the old Cogent Systems.)
However, there are two possible issues with a Thales purchase of all or part of IDEMIA.
- Antitrust issues. Automated fingerprint identification systems isn’t the only product that Thales and IDEMIA have in common. For example, both companies provide driver’s licenses in the United States. As any Thales purchase of IDEMIA is considered by the United States, France, and dozens of other countries, the deal could be opposed on antitrust grounds. This can be mitigated by limiting what Thales can buy, but it could complicate matters.
- Thales is French. Some of the driver’s license and biometric technology that IDEMIA sells was developed in the United States, and is used by many government agencies, including the Federal Bureau of Investigation and the Department of Homeland Security. At present, while IDEMIA is headquartered in France, it is primarily owned by Americans, so there’s a teeny bit of comfort in that. But what if a French firm were to own IDEMIA? The horror! (Many years ago, when Cogent Systems first sold itself, it intentionally chose a U.S. buyer, 3M, for this very reason.) Never mind that the U.S. government has been using French (and Japanese) technology for years, and that some very specific arrangements have been set up to mitigate the risks of foreign ownership. Some Senator or another is guaranteed to raise a big stink if U.S. government institutions are dependent upon a French company.
So perhaps Thales could buy all or part of IDEMIA, or perhaps it may pass. But if Thales passes, are there any U.S.-owned companies that may have an interest in IDEMIA’s technology?
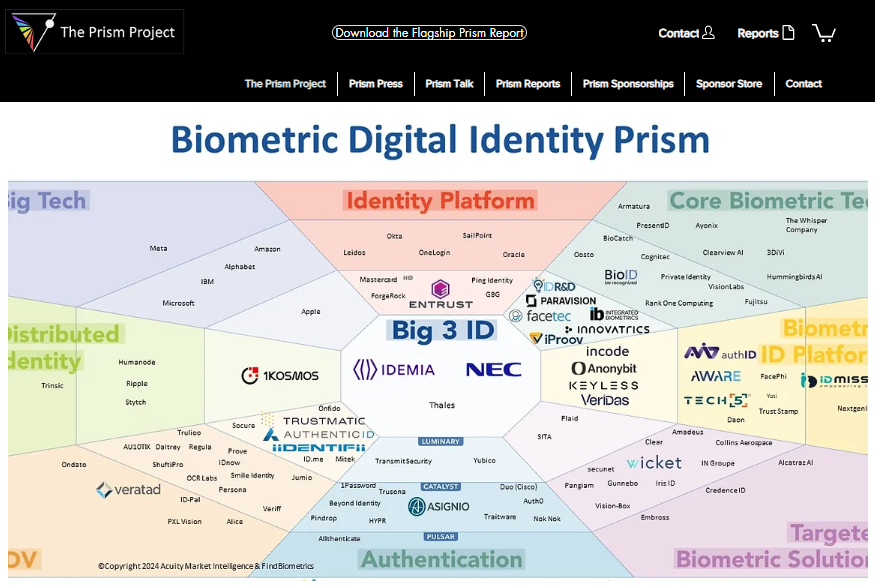
Because of my biometric bias, the first thing that I would consider would be American companies that are active in the biometric market. However, many of the U.S. companies are small, and don’t have a few billion dollars lying around to buy IDEMIA. So don’t look for Aware, Clearview AI, Paravision, Rank One Computing, or the like to be a buyer.
There are of course much bigger U.S. firms in high tech that have dipped their fingers into the biometrics market. Amazon, Apple, Facebook, Google, and Microsoft all come to mind. However, those same customers that are of prime concern to U.S. Senators are also or prime concern to the employees of some of those firms, who don’t want their employers to do business with the “evil” Department of Homeland Security or even the “evil” local police departments that should all be defunded. (Amazon quit selling Rekognition to police agencies, for example.) Even Apple, which is developing its own digital driver’s license technology, is probably reluctant to own IDEMIA.
But there’s one tech company that intrigues me as possibly having an interest in IDEMIA.
Oracle.
It’s big enough to make the purchase, certainly likes to make acquisitions, and has no hesitation about working with government agencies.
ANY government agency.
After all, the name “Oracle” came from a database project that Ellison worked on before founding the company with the same name.
His client was the Central Intelligence Agency.
If you’ve paid attention to this article, then you already know that since I have speculated that Oracle could purchase IDEMIA, that puts the chances of Oracle actually purchasing IDEMIA at zero.
And for all we know, Reuters’ two sources might be unreliable, or something else might happen (another COVID variant?) that could cause Advent to hold on to IDEMIA for a few more years.
So we’ll have to see what happens.