Tag Archives: identity
Contact My Friend
An odd email arrives with the subject line “Contact My Friend.” And so the scam begins…unless you know your business.
Spotting GoFundMe “Helper” Scammers
When someone approaches you to “help” with your fundraiser, look for these 3 scammer signs:
- The contact says no specifics about the fundraiser.
- The contact is NOT the helper.
- You MUST go to a different platform.
Know your business!
Also see my previous posts on GoFundMe “helper” scams:
Bredemarket helps anti-fraud firms market their products. https://bredemarket.com/mark/
My Latest Honeypot
I’ve created honeypots before, but this one was designed to lure people who scam GoFundMe fundraisers.
And it worked.

Bredemarket helps anti-fraud firms market their products. https://bredemarket.com/mark/
GoFundMe? No, GoFund ME! Fraud Scams Targeting Fundraisers
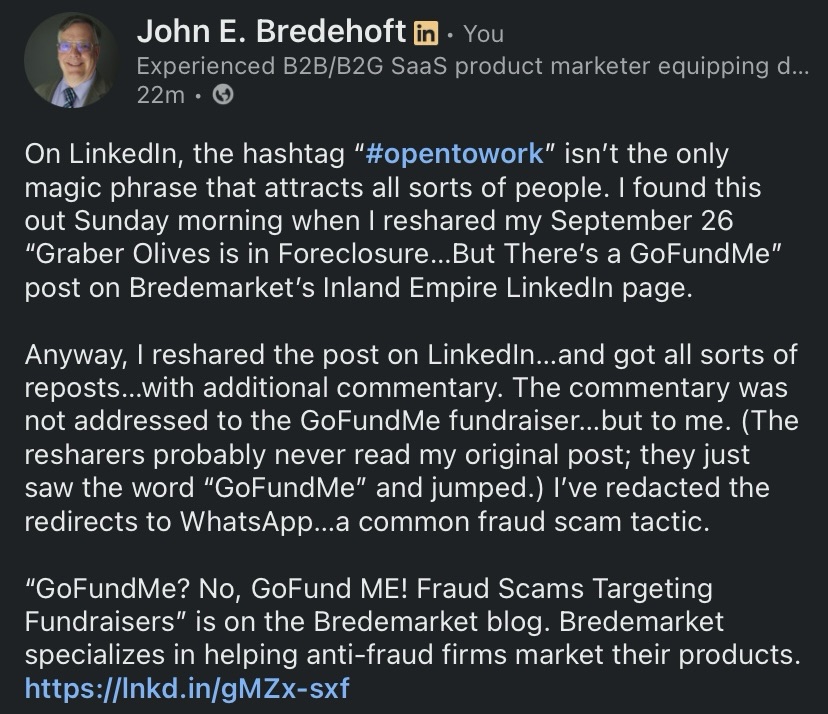
On LinkedIn, the hashtag “#opentowork” isn’t the only magic phrase that attracts all sorts of people. I found this out Sunday morning when I reshared my September 26 “Graber Olives is in Foreclosure…But There’s a GoFundMe” post on Bredemarket’s Inland Empire LinkedIn page.
You will recall that the post detailed Kelsey Graber’s fundraising efforts to keep the Graber Olive House from foreclosure. As of October 19 the GoFundMe fundraiser is still active at the https://www.gofundme.com/f/dont-let-ontario-lose-its-oldest-landmark URL.

I should note this is Kelsey Graber’s GoFundMe. This is not my GoFundMe.
Anyway, I reshared the post on LinkedIn…and got all sorts of reposts…with additional commentary. The commentary was not addressed to the GoFundMe fundraiser…but to me. (The resharers probably never read my original post; they just saw the word “GoFundMe” and jumped.) I’ve redacted the redirects to WhatsApp…a common fraud scam tactic.
The scammers’ what
Foone Berkeley:
“Hi, I came across your campaign, really impressive work. It reminded me of an independent group I’ve seen quietly helping project owners connect with private contributors who genuinely want to make a difference.
I’m not part of their team, but I’ve seen them support a few people in my circle. If you’re open to exploring new sources of backing, you can reach them directly here:
📞 WhatsApp: [REDACTED]
They usually prefer to speak one-on-one with campaign owners to understand their goals and see if there’s a good fit.
Wishing you continued success, your work truly deserves attention.”
Alex Mary:
“Hello 🌸 I just read your campaign, and it truly touched me. I know how tough fundraising can be, but there are genuine people out there who want to help. A trusted charity once helped me raise over $38,000 after I’d almost given up. If you’d like, you can message them on WhatsApp 👉 [REDACTED] they might be able to guide you too. 💙”
Olivia Williams:
“If you’re looking to grow your campaign donations fast, I truly recommend reaching out to Crowd. She’s an expert in GoFundMe promotions and helped me raise over $180,000 a few months ago! he knows exactly how to attract real donors and get results. You can contact her directly here [REDACTED]”
The scammers’ how
Let’s look at the red flags common to all three:
- The person is touched by the fundraising effort, but doesn’t say anything specific about them. (And doesn’t acknowledge that this is someone else’s fundraiser, not mine.)
- The person resharing is not the person who can provide help. It’s always someone else: an independent group, a trusted charity, or a woman (or man?) named Crowd.
- The person wants to get you off LinkedIn as soon as possible. Private email, SMS, or an encrypted service like WhatsApp or Telegram.
The scammers’ goals
So why are these people so willing to recommend helpers who can assist desperate GoFundMe fundraisers? GoFundMe itself has addressed this:
“If someone you don’t know is reaching out to offer something that sounds too good to be true, we always recommend validating the individual before sharing any personal information. Donors and donor networks shouldn’t expect anything from you in return for their generosity.”
Two common tactics include:
- Guarantee reaching your fundraising goal in exchange for a service fee or percentage of funds raised
- Make a donation if you provide personal information such as email address, phone number, or banking information
There are other tactics, but the goal is the same. Instead of helping you raise money, the “helper” wants to get money from you.
Now there are legitimate companies that assist charities in their fundraising efforts…but they can be contacted via methods other than WhatsApp.
Today’s honeypot
And now that I’ve written this warning, I’m going to conduct a little experiment.
I’m going to reshare THIS post on LinkedIn.
With quotes from the first and fourth paragraphs that include several mentions of the word “GoFundMe”…plus the additional honeypot word #opentowork. (I haven’t planted an opentowork honeypot in a while. Oh, and not that they’ll notice, but the words “fraud” and “scam” also appear.
Let’s see what moths are attracted to the new flame.
And consider what YOU are doing to fight fraud.
Bredemarket specializes in helping anti-fraud firms market their products.
(Image sources: Gemini (still), GoFundMe, Grok (video). Only the GoFundMe is real.)
Reducing Biometric Marketing Internal Bias By Using Bredemarket
Identity/biometric marketing leaders continuously talk about how their companies have reduced bias in their products. But have they reduced bias in their own marketing to ensure it resonates with prospects?
I recently talked about the problem of internal bias:
“Marketers are driven to accentuate the positive about their companies. Perhaps the company has a charismatic founder who repeatedly emphasizes how ‘insanely great’ his company is and who talked about ‘bozos.’ (Yeah, there was a guy who did both of those.)
“And since marketers are often mandated to create both external and internal sales enablement content, their view of their own company and their own product is colored.”
Let’s look at two examples of biometric marketing internal bias…and how to overcome it.

Internal bias at Company A
- Company A does not participate in the U.S. National Institute of Standards and Technology (NIST) Face Recognition Technology Evaluation (FRTE) for technical reasons.
- As a result, the company’s marketing machine constantly discredits NIST FRTE, and the company culture is permeated with a “NIST is stupid” mentality.
- All well and good…until it runs into that one prospect who asks, “Why are you scared to measure yourself against the competition? Does your algorithm suck that bad?”
Internal bias at Company B
- Company B, on the other hand, participates in FRTE, FATE, FRIF (previously FpVTE), and every other NIST test imaginable.
- This company’s marketing machine declares its superiority as a top tier biometric vendor, supported by outside independent evidence.
- All well and good…until it runs into that one prospect who declares, “That’s just federal government test data. How will you perform in our benchmark using our real data and real computers?”
Internal bias at Bredemarket
Well, I have my admittedly biased solution to prevent companies from tumbling into groupthink, drinking of Kool-Aid, and market irrelevance.
Contract with an outside biometric product marketing expert. (I just happen to know one…me.)

I haven’t spent 30 years immersed in your insular culture. I’ve heard all the marketing-speak from different companies, and I’ve written the marketing-speak for nearly two dozen of them. I can ensure that your content resonates with your external customers and prospects, not only with your employees.
All well and good…until…
Reducing internal bias at Bredemarket
“But John, what about your own biases? IDEMIA, Motorola, Incode, and other employers paid you for 25 years! You probably have an established process that you use to prepare andouillette at home, based upon a recipe from 2019!”

I don’t…but point taken. So how do I minimize my own biases?
My breadth of experience lessens the biases from my past. Look at my market-speak from 1994 to 2023, in order:
- We are Printrak, a nimble private company that will dominate AFIS with our client-server solution.
- We are Printrak (stock symbol AFIS) a well-funded public company that will dominate AFIS, mugshot, computer aided dispatch, and microfiche.
- We are Motorolans, and our multi-tier Digital Justice Solution has a superior architecture to that of Sagem Morpho and others.
- We are MorphoTrak, bringing together the best technologies from MetaMorpho and Printrak BIS, plus superior French technology for secure credentials and road safety…unencumbered by the baggage that weighs down MorphoTrust.
- We are IDEMIA North America, bringing together the best technologies from MorphoTrust and MorphoTrak for ABIS, driver’s licenses, and enrollment, coupled with the resources from the rest of IDEMIA, a combined unbreakable force.
- We are Incode, not weighed down with the baggage of the old dinosaurs, and certainly not a participant in the surveillance market.
Add all the different messaging of Bredemarket’s clients, plus my continuous improvement (hello MOTO) of my capabilities, and I will ensure that my content, proposals, and analysis does not trap you in a dead end.
Reducing internal bias at your company
Are you ready to elevate your company with the outside perspective of a biometric product marketing expert?
Let’s talk (a free meeting). You explain, I ask questions, we agree on a plan, and then I act.
Schedule a meeting at https://bredemarket.com/mark/
Identity and Expression
(Part of the biometric product marketing expert series)
Whether you are a human or a non-person entity (NPE) with facial recognition capability, you rely on visual cues to positively identify or authenticate a person. Let’s face it; many people resemble each other, but specific facial expressions or emotions are not always shared by people who otherwise look alike.

But in one of those oddities that fill the biometric world, you can have TOO MUCH expression. Part 3 of International Civil Aviation Organization (ICAO) Document 9303, which governs machine readable travel documents, mandates that faces on travel documents must maintain a neutral expression without smiling. At the time (2003) it was believed that the facial recognition algorithms would work best if the subject were expressionless. I don’t know if that holds true today.

But once the smile is erased, any other removal of expression or emotion degrades identification capability significantly. For example, closing the eyes not only degrades facial recognition, but is obviously fatal to iris recognition.

And if you remove the landmarks upon which facial recognition depends, identification is impossible.

While expression or lack thereof does not invalidate the assumption of permanence of the biometric authentication factor, it does govern the ability of people and machines to perform identification or authentication.
Communicate with the Words of Authority
Biometric marketing leaders, do your firm’s product marketing publications require the words of authority?

Can John E. Bredehoft of Bredemarket—the biometric product marketing expert—contribute words of authority to your content, proposal, and analysis materials?
I offer:
- 30 years of biometric experience, 10 years of product marketing expertise, and complementary proposal and product management talents.
- Success with numerous biometric firms, including Incode, IDEMIA, MorphoTrak, Motorola, Printrak, and over a dozen biometric consulting clients.
- Mastery of multiple biometric modalities: friction ridge (fingerprint, palm print), face, iris, voice, DNA.
- Compelling CONTENT creation: blog posts, case studies and testimonials, LinkedIn articles and posts, white papers.
- Winning PROPOSAL development: managing, writing, editing for millions of dollars of business for my firms.
- Actionable ANALYSIS: strategic, market, product, competitive.
To embed Bredemarket’s biometric product marketing expertise within your firm, schedule a free meeting with me.
Today’s Acronyms are CMMI, ISACA, and NSS
I’m going to discuss the acronyms CMMI and NSS, which I’ve kinda sorta discussed before but never in combination. (And as an added bonus I’ll discuss one more acronym.)
Capability Maturity Model Integrated (CMMI)
Back in February and in April I made passing references to CMMI, which stands for the Capability Maturity Model Integration. But I only mentioned it in passing because my experience is with the older Capability Maturity Model (CMM).

Who manages the CMMI?
Information Systems Audit and Control Association (ISACA)
Back in March and in April I either explicitly referenced or implicitly quoted from ISACA, which is the Information Systems Audit and Control Association.
Back in 2016 ISACA acquired the CMMI Institute, which managed CMMI. But the process suites originated earlier.
“CMMI was originally developed at the Software Engineering Institute, a federally funded research and development center within Carnegie Mellon University.”

Thus ISACA governs all CMMI-related activity, including assessments and certifications.
Which brings us to…
National Security Systems (NSS) and National Security Solutions (NSS)
‘Cause you know sometimes acronyms have two meanings.

Although in this case the two are related.
When a foreign-owned company wants to do business with the sensitive parts of the U.S. federal government, they have to set up a set up an entity that is free from foreign ownership, control, or influence. This is FOCI, a bonus acronym for you today.

In the biometric world, there are two notable FOCI-mitigated subsidiaries of foreign companies:
- NEC National Security Systems (NSS), a subsidiary of the Japanese-owned NEC.
- IDEMIA National Security Solutions (NSS), a subsidiary of the primarily U.S.-owned IDEMIA. Primarily, but not exclusively, because a small sliver of IDEMIA is French-owned.
Bringing all the acronyms together
Focusing on IDEMIA National Security Solutions, the company recently made a CMMI-related announcement:
“IDEMIA National Security Solutions (NSS), a subsidiary of IDEMIA, the leading provider of secure and trusted biometric-based solutions, is proud to announce that it has successfully earned re-certification at level 3 of ISACA’s Capability Maturity Model Integration (CMMI®).”

You’ll recall that the CMMI levels go up to Level 5. So IDEMIA NSS is not at the maximum CMMI level, but Level 3 is impressive enough to issue a press release.
IDEMIA NSS’ extensive federal government work dictates that it maintain a number of certifications and conformances. CMMI gives the government agencies assurance that IDEMIA NSS provides its products according to specific quality and process improvement standards.
Why Do We Trust SMS?
I hate to use the overused t word (trust), but in this case it’s justified.
“Scammers are aware that people are more likely to open and read a text message rather than an email The open rates for text messages are more than 90% while the open rates for emails is less than 30%. In addition, many email providers have filters that are able to identify and filter out phishing emails while the filtering capabilities on text messages is much less. Additionally, people tend to trust text messages more than emails. Text message also may prompt a quick response before the targeted victim can critically consider the legitimacy of the text message.”
From Scamicide, https://scamicide.com/2025/09/18/scam-of-the-day-september-19-2025-treasury-refund-text-smishing-scam/
What I can’t figure out is WHY text messages have such a high level of t[REDACTED]. Does SMS feel more personal?






