This has been a long-standing favorite of mine, from the old days before everyone used artificial intelligence to create their own robots. (Or lovers.)
But rather than sharing the original video, I’m sharing the “live” television performance.
Identity/biometrics/technology marketing and writing services

This has been a long-standing favorite of mine, from the old days before everyone used artificial intelligence to create their own robots. (Or lovers.)
But rather than sharing the original video, I’m sharing the “live” television performance.
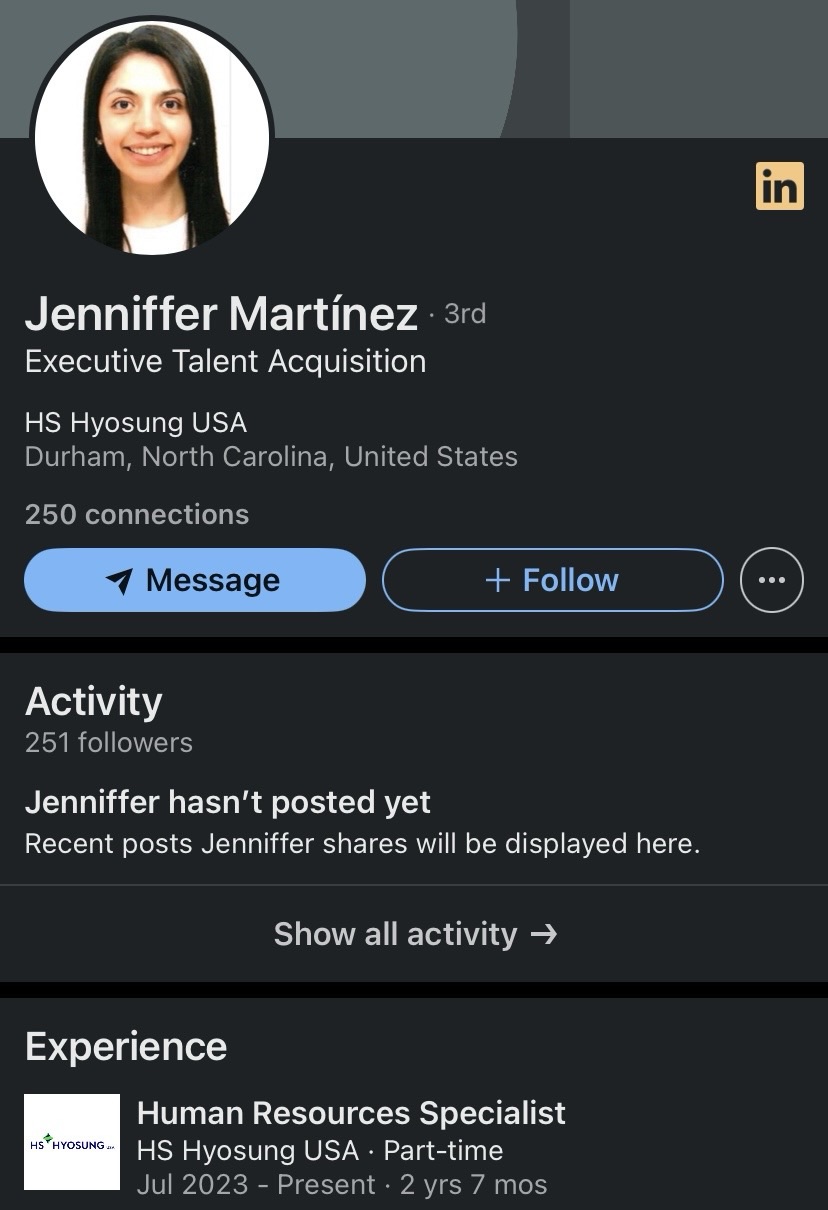
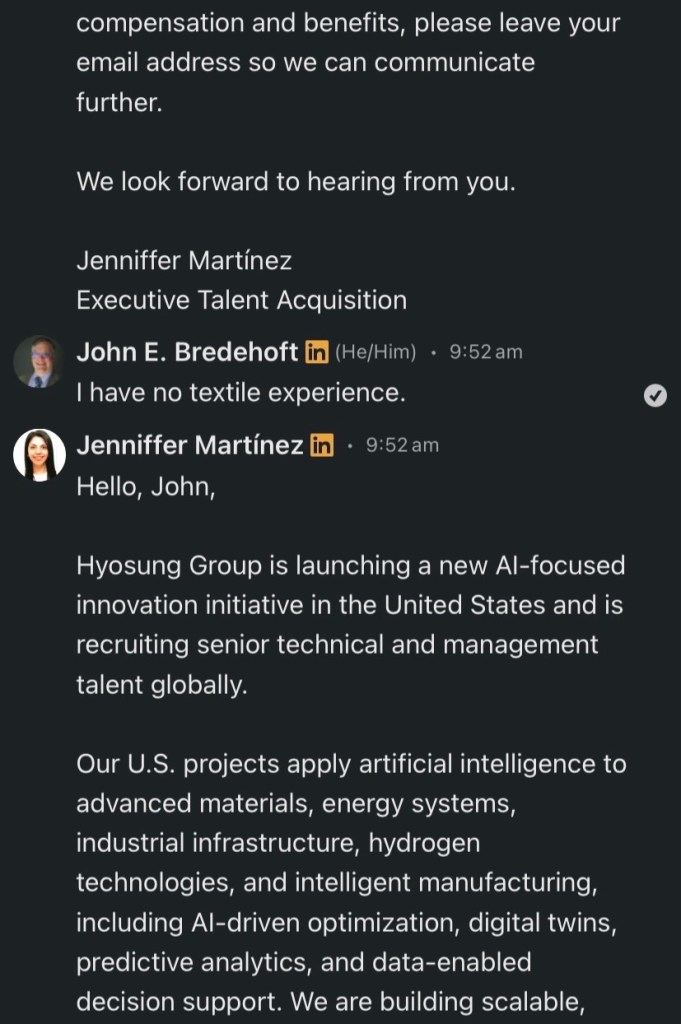
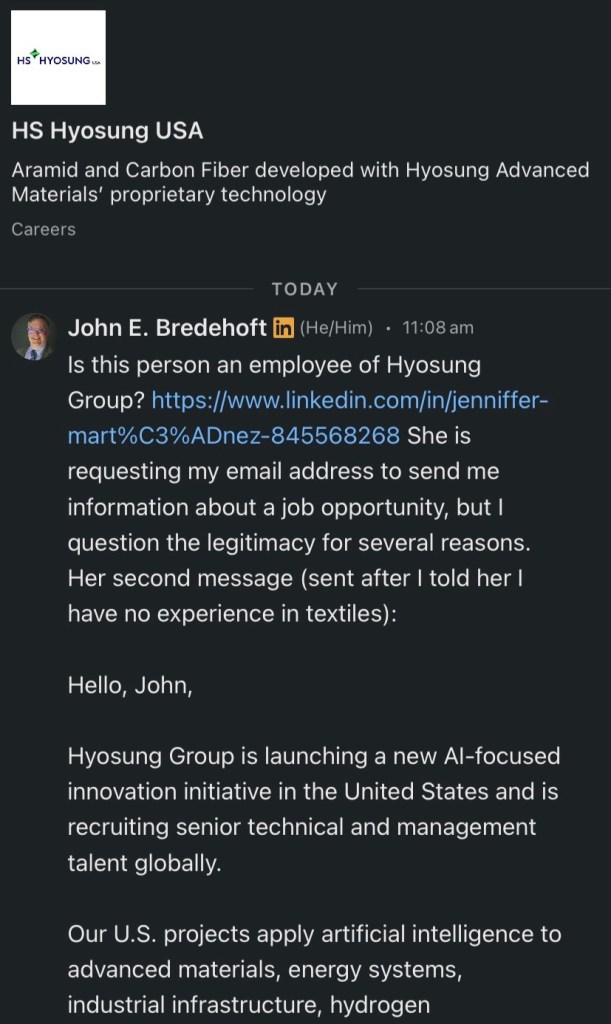
I was messaged on LinkedIn by Jenniffer Martinez, purportedly from HS Hyosung USA. She wanted my email address to send information about a job opportunity.
Why?
“After reviewing your resume and relevant experience, we believe your management experience, professional background, and career stability are a strong match for Yaskawa Group’s current talent needs.”
(Only now did I notice the reference to Yaskawa Group, whatever it is.)
Eventually I told “Jenniffer” that I had contacted her employer directly.
By 11:30 she had deleted her entire conversation, which is why I took screen shots immediately.
And I never even got around to asking her for HER corporate email address.
No word from HS Hyosung USA, but it knows all about Jenniffer now (see final screen shot).
Know Your Employer.



Bredemarket works with a number of technologies, but it’s no secret that my primary focus is biometrics. After all, I call myself the “biometric product marketing expert,” having worked with friction ridge (fingerprint, palm print), face, iris, voice, and rapid DNA.
If I can help your biometric firm with your content, proposal, or analysis needs, schedule a free meeting with me to discuss how I can help.

Yes it’s political, but I couldn’t resist.

You would think that bars would hate Dry January.
Ontario, California’s Strum Brewing Company embraces it.
In a Facebook post it welcomes Dry Januarians with its non-alcoholic offerings.
• **Alcohol-free Slushies** (yes, still fun 👀)
• **Sodas** & NA beers**
• **Flavored Waters & Hop Water**
• **Scrumptious Cookies, Beef Jerky, Pretzels, Pork Rinds , Garlic Peanuts, and soon Hummus & Toum**
• Cozy vibes & good company all month long 🎶🐾
Strum Brewing is on Euclid Avenue in downtown Ontario.

Unchecked disinformation runs wild in this Slashdot story, contributed anonymously.
“Only the government could spend 20 years creating a national ID that no one wanted and that apparently doesn’t even work as a national ID. But that’s what the federal government has accomplished with the REAL ID, which the Department of Homeland Security (DHS) now considers unreliable, even though getting one requires providing proof of citizenship or lawful status in the country.”
The anonymous Slashdot contributor is either a liar or a fool. As I noted back in May after Leonardo Garcia Venegas’ first detainment (I didn’t know he was detained a second time), a REAL ID was NEVER intended to prove citizenship.
Here are California’s non-citizen REAL ID requirements, which are federally acceptable:
“This includes all U.S. citizens, permanent residents who are not U.S. citizens (Green Card holders), and those with temporary legal status, such as recipients of Deferred Action for Childhood Arrivals (DACA) or Temporary Protected Status (TPS) and holders of a valid student or employment visa.”
But since the REAL ID expiration date matches the date at which temporary legal status expires, it DOES prove legal presence.
Slashdot, get your facts straight.
Postscript: Slashdot lifted its claims from Reason.


If our AI twins are allowed to violate space and time, then mine will parachute into Times Square.
The real me, safely on the ground, wishes Bredemarket prospects, clients, and supporters a Happy New Year.

The end of the old year means the beginning of a new one.
Start the year off right by acting to fill your content gaps. Click below and schedule a free meeting with Bredemarket to address your content needs, and how Bredemarket can help ensure your visibility.

2025 has been a year of declutterring and focusing.
The declutterring is the hardest. I may still love that long sleeve shirt with holes in the right elbow. (Why always the right elbow? I’m left handed.) But it’s no longer good for me, and I should have gotten rid of it years ago.
Whether it’s a former friend—a great person who went silent and indifferent—or a newsletter from a company that rejected my 2023 job application and only contacted me afterwards because GDPR required it—the time has come to simplify and focus.
Now just a few hundred LinkedIn newsletters and email subscriptions to go.
And to see where I can focus now.