Are you a technology marketing leader who lies awake at night worrying about the following?
“Keeping up with the speed and complexity of the digital landscape.”
Well, maybe not that exact phrase. That sounds like something generative AI would write.
And in fact, my buddy Bredebot wrote it when answering a question about Chief Marketing Officer pain points relative to content.

But I’m not going to let Bredebot write an entire post about it, because I’m going to write it myself.
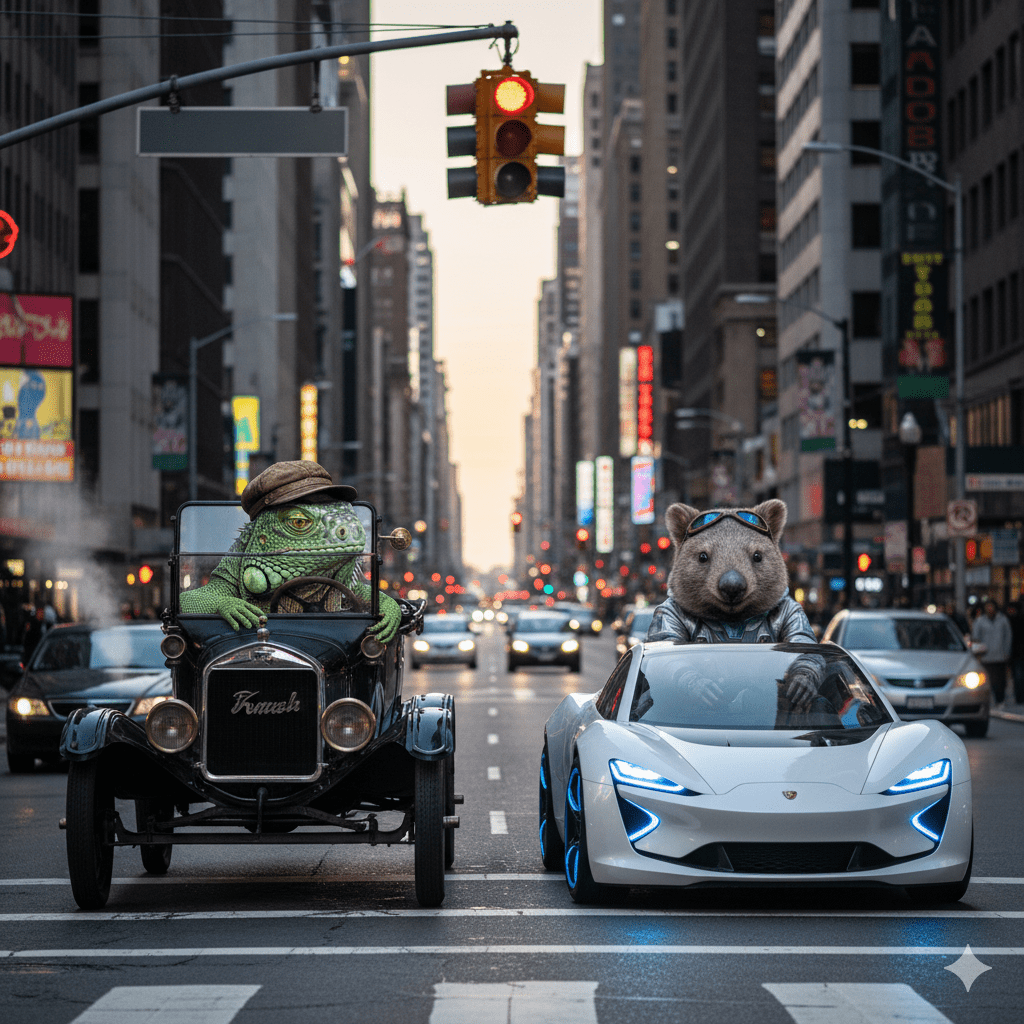
The human way to reflect the sentiment above is to ask whether your content is up-to-date, or is as dated as a Pentium.
And that’s something that a marketing leader DOES worry about, because they (usually) want their firms to be perceived as innovative, not old fashioned.
Let me give you an example of outdated content that persists today.
SEO, AEO, GEO…I believe they’re different
For years we have been discussing search engine optimization, or SEO. The whole point of SEO is to ensure that your content appears at the top of results when you use Google or Bing or another search engine to launch a search. (Ignore “sponsored content” for a minute here.)
In case you haven’t noticed, fewer and fewer people are using search engines. Instead, they are searching for answers from their favorite generative AI tool, and now the new term the kids are using is answer engine optimization, or AEO. Or perhaps you can follow the lead of Go Fish and refer to generative engine optimization, or GEO.
Now some people are continuing to use SEO when they mean AEO and GEO, under the theory that it’s all just optimization, and it’s all just searching but just with a different tool. Personally, I believe that continuing to refer to SEO is confusing because the term has always been associated with search engines.
Plus, the concept of keywords is fading away, as Lisa Garrud noted in May.
“Unlike traditional SEO, which focuses on ranking for keywords, AEO concentrates on providing comprehensive, authoritative answers that AI systems can easily process and deliver to users….
“Think about how you use AI tools today. You don’t ask for ‘electrician Auckland residential services’, you ask, ‘What’s causing the flickering in my kitchen lights?’ or ‘How much should it cost to rewire a 1970s house?’ You want answers, not search results.”
But forget about XEO and let’s return to the content YOU create.
How do you keep YOUR content up-to-date?
Let’s say that you’ve reached the point in your content calendar where you have to write a blog post about pop music.
And let’s also say that you’re old enough to remember the 20th century.
You may have a problem.
For example, when you see the words “pop music,” you may immediately spell the second word with a “z” and a “k” when you TALK ABOUT.
Or if someone mentions INTERPOL, you immediately respond with Deutsche Bank, FBI, and (und?) Scotland Yard.
And now that I’ve lost half my reading audience, you can see my point. While personas are approximations, you need to refer to them when crafting your content. If your hungry people (target audience) tend to be in their 20s and 30s, they’re probably not going to understand or respond to songs from M (Robin Scott) or Kraftwerk.
There are other things you can write that are obviously old, such as “fingerprint identification decisions are infallible.” That statement was questioned back in 2003…BEFORE the whole Brandon Mayfield thingie.
So how does a marketer ensure that their content is not dated? By remembering to ask, then act. Question your assumptions, do your research, write your content, then check your content.
Question your assumptions
Before you write your content, ensure your premise is correct. For example, I didn’t assume without questioning that “keeping up with the speed and complexity of the digital landscape” was a pressing issue. I KNEW that it was a pressing issue, because I encounter it daily.
Do your research
Next, take a moment and check what you are about to say. Was your assumption about fingerprint examiner infallibility affected by the NAS report? Was your assumption affected by activities that occurred after the NAS report?
Write your content
At some point you have to stop asking and start acting, writing your content. Write your draft 0.5 to get your thoughts down, then write your draft 1.0. And keep your personas in mind while you do it.
Check your content
Once it’s drafted, check it again. Have your dated assumptions crept into your writing? Did you use the term “SEO” out of habit, by mistake? Fix it.
The results of up-to-date content
If you do all these things, you’ll ensure that your competitors don’t laugh at your content and tell you how out of touch you are.
Ideally, you want your competitors to show how out of date they are.
“Look at WidgetCorp, who doesn’t even know how to spell! Their writer’s left finger slipped while typing, and they typed the so-called word ‘AEO’ rather than ‘SEO’! Everybody know the term is SEO!”
Which gives you the opportunity to write a succinct reply to your bozo competitor.
I’ll give you the joy of writing it yourself.
Unless you want Bredemarket to write it, or other content. Book a free meeting to discuss your needs. https://bredemarket.com/mark/