I recently discussed some proposed changes to the way in which beneficial ownership information (BOI) is collected. However, even after the changes are made, FinCEN will still collect BOI for foreign firms.
Hungary, facial recognition, and geolocation
Biometric Update recently published a story about facial recognition in Hungary, and its use to identify people who display rainbows and dress in ways “that diverge from the gender they were assigned at birth.” I’m going to zero in on one portion of the story: the facial recognition provider involved.
The company FaceKom has been around under different names since 2010 but has seen significant growth during the past few years thanks to investments from the Central European Opportunity Private Equity Fund (CEOM). The fund has no direct links with [Prime Minister Orbán’s son-in-law, István] Tiborcz. However, it is registered on the same address in Budapest where several companies owned by Orbán ‘s son-in-law operate.
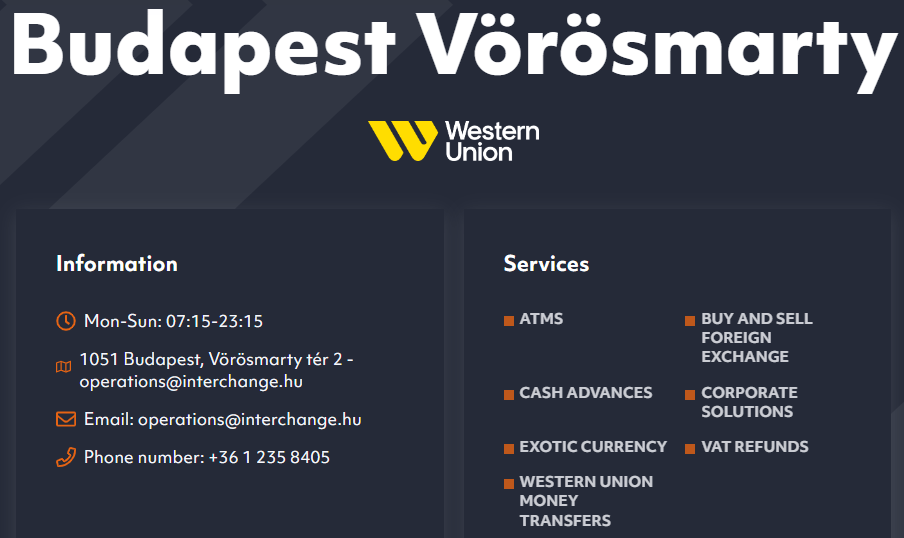
Ah, geolocation! The Chi Fu Investment Fund Management Zrt.’s address of record is 1051 Budapest, Vörösmarty tér 2.
And do you know what else is at that address?
A Western Union Currency Exchange.
Well, that’s enough to drive some conspiracy theorists crazy.
Beneficial ownership and legal ownership
So I didn’t find the smoking gun, but I do want to take this opportunity to point out what BENEFICIAL ownership is. Investopedia:
A beneficial owner is a person who enjoys the benefits of ownership even though the title to some form of property is in another name.
Using the Hungarian example (without the Western Union part), it’s not enough to say that CEOM and/or Chi Fu Investment Fund Management Zrt. (I don’t know enough Hungarian to confirm they are one and the same) does not list István Tiborcz (or Victor Orbán) as an official owner or co-owner.
As Unit21 points out, you don’t have to literally own (either on your own or through a trust) 25% of an entity to be a beneficial owner. Here’s another criterion of a beneficial owner:
Any individual that holds a significant ability to control, manage, or direct the legal entity
De facto control without de jure control could very well be wielded by a powerful politician, or his son-in-law.
(Imagen 3)