When Bredemarket begins an engagement with a client, I usually have no idea what processes, templates, or practices the client already has. So I have to handle whatever is or is not there and either understand what is there, adapt it, or create what is needed.
Understand
In some cases clients already have a process.
For example, as I delved into the Sharepoint library for one of Bredemarket’s clients, I found a complete set of branding guidelines that covered logos, colors, and many other aspects of the company’s branding.
In that case, my job is to simply make sure that I align with the client’s branding, and that my content, proposals, and analysis work for the client aligns with the branding guidelines…or with whatever other process the client has.
Adapt
Sometimes the client has a process, but it needs to be adapted in some way.
Here’s an example I can publicly share: not from a Bredemarket client, but from my former employer Motorola (back when Motorola was one company). I was a product manager at the time, and products were developed via a “stage gate” process. At Motorola, of course, it was called M-Gates.
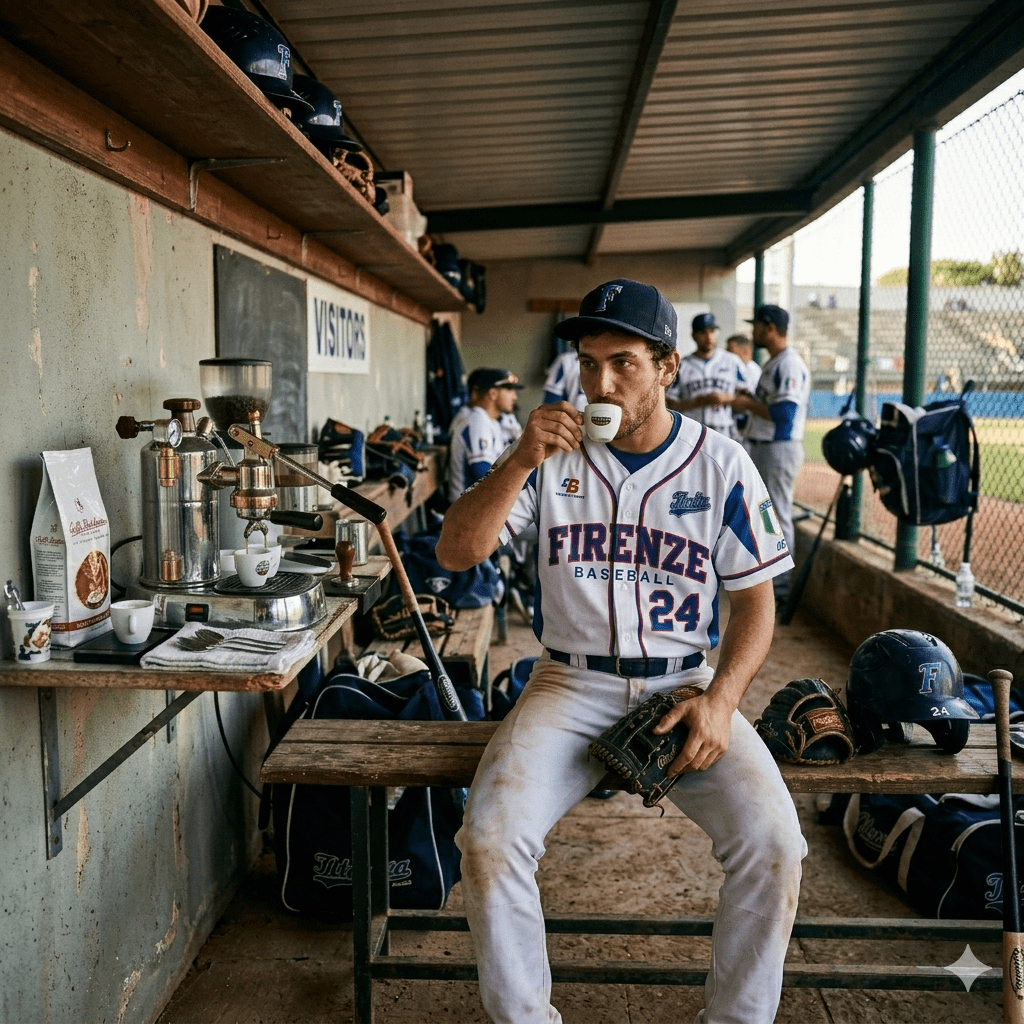
Our “Printrak” group (automated fingerprint identification systems, computer aided dispatch systems, and the like) was the odd group out in our part of Motorola (the part that would later become Motorola Solutions). Most of the people in that part of Motorola sold police radios that were manufactured in bulk. Therefore the stage gate process included a step for a limited production run of police radios before moving to full production.
That didn’t apply for the software we sold to government systems. For example, the entire production run for the Omnitrak 8.1 release was no more than a half dozen systems for customers in Switzerland, Oklahoma, and other places. A limited production run wouldn’t make sense.
So OUR stage gate process eliminated that step and went straight to full production.
Create
And then there are the clients who don’t have anything. In these cases, my invention hat goes on.
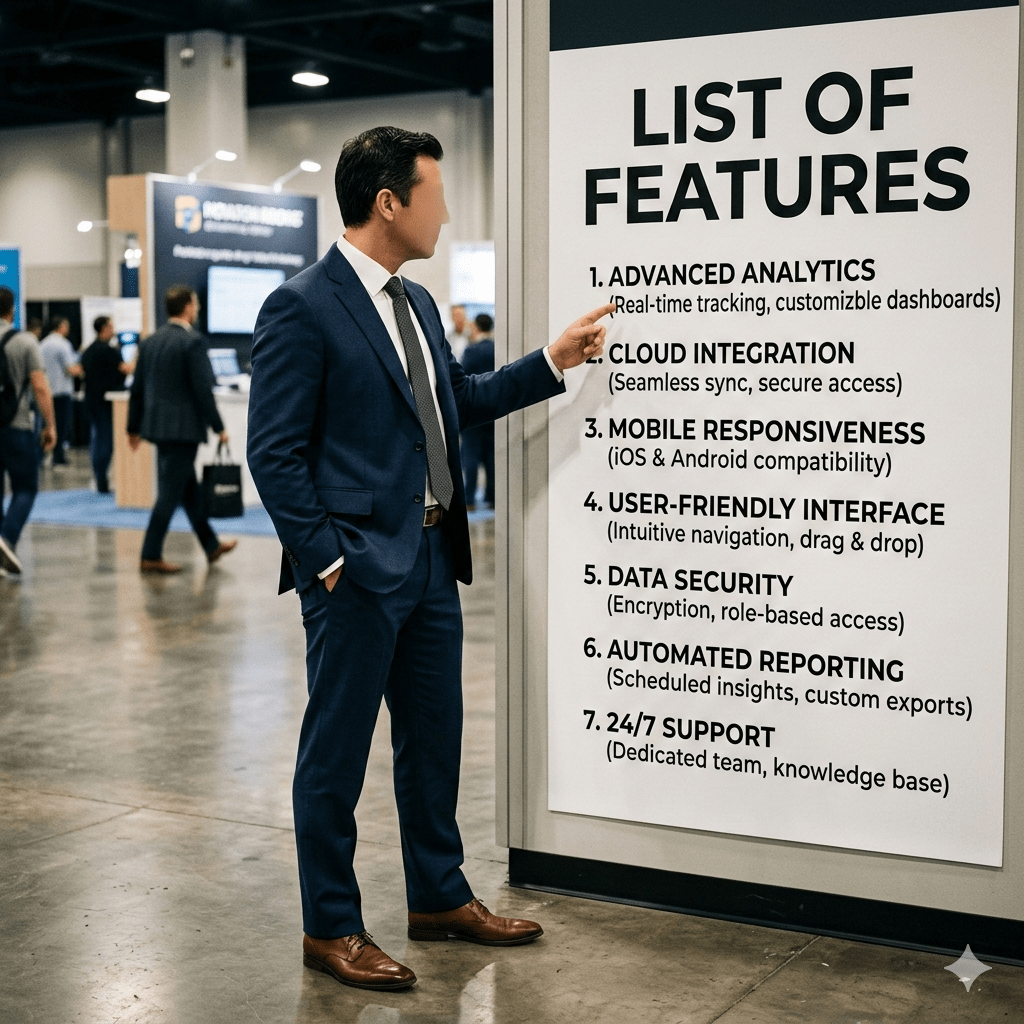
For one Bredemarket client, I was asked to develop several pieces of collateral, such as (ironically) one on process maturity, and several random pieces of content tied to a product release.
I decided to approach it more systematically by introducing a simple go-to-market process that defined the external and internal collateral required for a “high” tier product release and a “low” tier product release. Resisting my urge to define something thorough, I simplified the GTM process as much as possible, while still providing guidance on what a product release should contain.
The client rejected the idea: “we don’t need no steenking process.”
Not surprisingly, the process maturity content was never released either.
I’ve had better luck with other Bredemarket clients, defining go-to-market, proposal, and other processes for them as needed.
Be Prepared
Providing product marketing expertise is much more than writing about a product.
Before I write a word of text, I ensure that the content aligns with the client’s strategies…or my own strategies if the client doesn’t have any.
And of course I ask questions.