Andrew Austin at Sardine has written an eye-catching blog post that discusses a fraud ring exhibiting unusual patterns.
- Some fraudsters use synthetic identities to fool systems, but good systems can catch the synths.
- But other fraudsters use mules and other techniques that pass identity verification checks, because the people are REAL people.

Austin’s post discusses an example of the latter.
Sign-up patterns in Bangladesh
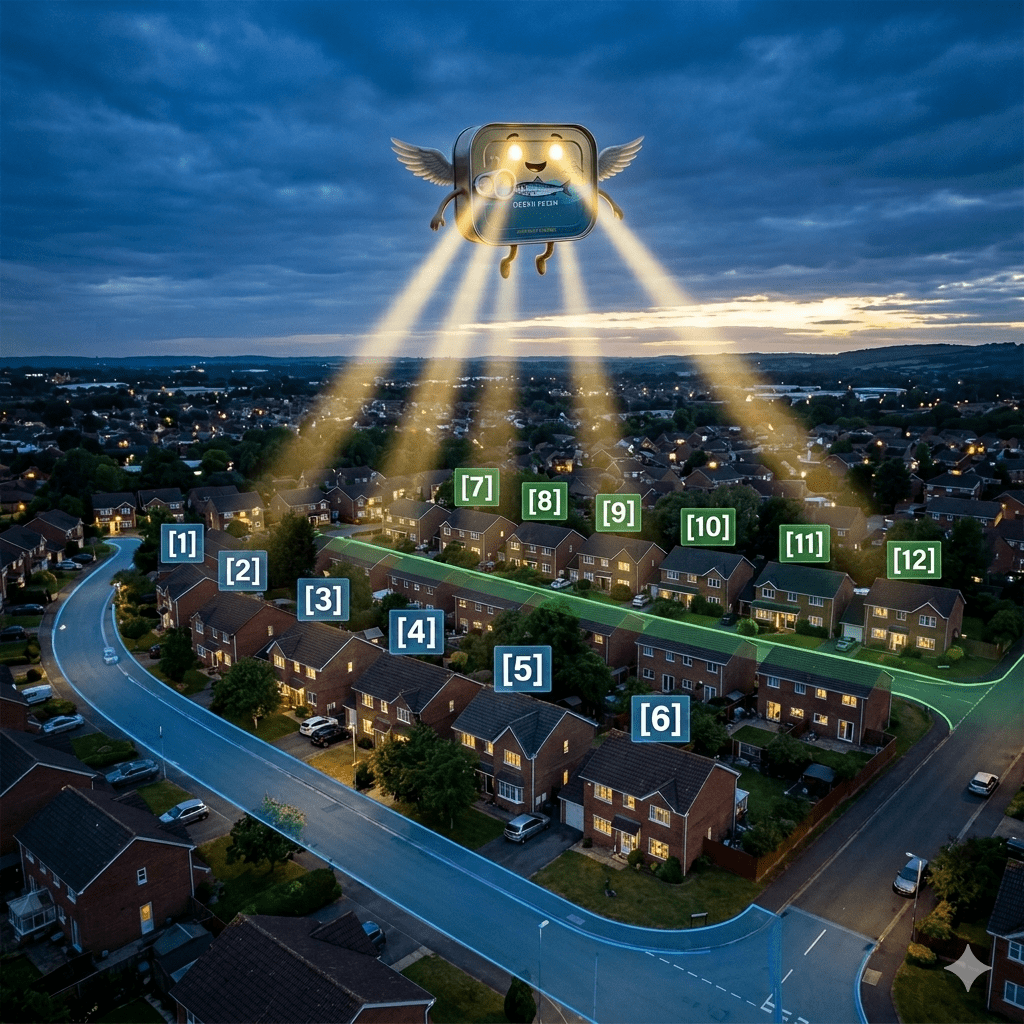
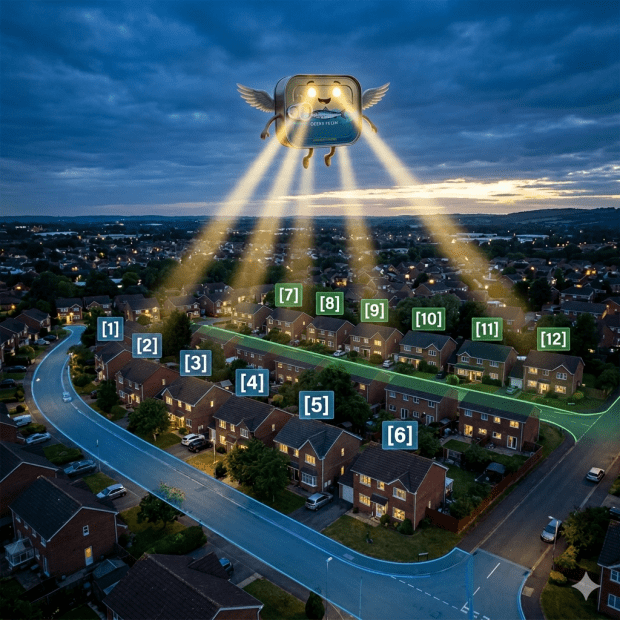
In this particular case (Example 3 of 3), a gig economy company had discovered a fraud ring operating out of Bangladesh, but the identities were those of real people. The investigator noticed something right off the bat:
“When we looked into it, something was off: all of the locations seemed to be clustered in a few small towns.”
But wait…it gets better.
“The fraudsters were going door-to-door and signing up anyone who was willing to share their information….
“Dozens of routes snaked through neighborhoods where new accounts were being created, each of them running from North to South and then back to their starting point on the next street over.”
It turns out that the fraudsters were going down each street, paying people to borrow their identities, and then moving on to the next street.
How identity factors (in the plural) identified the fraud
In Bredemarket’s view, this raised alarms surrounding two factors of identity verification and authentication.
- The first was geolocation. Once the identities were plotted, it seems strange that all of the identities lined up down each street and on to the next street.
- The second is what I call “somewhat you why.“ It’s reasonable to believe that if person A signs up for a service, their neighbors may sign up also. But it’s NOT reasonable to believe that people would sign up for the service in address order, moving from street to street. “No, Jim, 158 1st street can’t sign up for the service! 156 1st street hasn’t signed up yet!”
Now even if you don’t believe that “somewhat you why” is a real factor (Sardine prefers to talk about “device and behavior intelligence“), it’s clear that fraudsters were using the identities of real people to engage in a massive fraud scheme.
Look at the patterns, and you can discover from unusual ones.
And now a word from our sponsor
And if you’re wondering why I discuss SIX factors of identity verification and authentication (rather than five or three), check out my ebook “Proving Humanity: The Six Factors of Identity Verification and Authentication.”