When you’ve been around long enough, zero trust is an attitude, not a technology. Which is how I reacted when I received an email from Substack yesterday and questioned whether it was REALLY from Substack.
The email
How many of you received this email yesterday?
Hello,
I’m reaching out to let you know about a security incident that resulted in the email address and phone number from your Substack account being shared without your permission.
I’m incredibly sorry this happened. We take our responsibility to protect your data and your privacy seriously, and we came up short here.
What happened. On February 3rd, we identified evidence of a problem with our systems that allowed an unauthorized third party to access limited user data without permission, including email addresses, phone numbers, and other internal metadata. This data was accessed in October 2025. Importantly, credit card numbers, passwords, and financial information were not accessed.
What we are doing. We have fixed the problem with our system that allowed this to happen. We are conducting a full investigation, and are taking steps to improve our systems and processes to prevent this type of issue from happening in the future.
What you can do. We do not have evidence that this information is being misused, but we encourage you to take extra caution with any emails or text messages you receive that may be suspicious.
This sucks. I’m sorry. We will work very hard to make sure it does not happen again.
– Chris Best, CEO of Substack
My reaction
My jaded reaction?
“Yeah, right.”
Yes, the email came from “Substack Standards & Enforcement” at security@substack.com, but such emails can be faked, and a few months ago I received an email processed by Substack’s servers that was NOT sent by the Substack account owner.
So last night I went to Substack’s own Substack account @substack to see what it said about the matter.
At the time…nothing.
As far as I was concerned, my email and phone number MAY have been breached, or maybe not. Perhaps some nefarious actor was trying to make Substack look bad.
So I forgot about it.
The article
This morning I revisited the issue to see if any reputable organizations had written about it. Not finding a Washington Post article, I turned to TechCrunch. (I’ve been reading TechCrunch since the Arrington days.)
Newsletter platform Substack has confirmed a data breach in an email to users.
So TechCrunch relied on the same information I had. There was no indication that TechCrunch had reached out to Substack directly to confirm the authenticity of the email.
Then again, TechCrunch printed its article at 6:55 am PST, and it was still up an hour later at 8 am. If the email had been a scam, Substack would have contacted TechCrunch immediately.
So I guess the story is legit.
Three ways to inform users of a breach
The story goes well beyond Substack, since sites are breached all the time. As far as I’m concerned, the issue isn’t “if,” but “when.”
(And yes I’m looking at you, all Workday-using sites that set the app to require account creation. How will you respond when a jobseeker asks you how you will protect their data WHEN your site is breached?)
There are three ways to inform your users of a breach.
[Bitdefender] surveyed over 400 IT and security professionals who work in companies with 1,000 or more employees. Bitdefender found that 42% of IT and security professionals surveyed had been told to keep breaches confidential — i.e., to cover them up — when they should have been reported.
Perhaps even more shockingly, 29.9% of respondents admitted to actually keeping a breach confidential instead of reporting it.
- Minimally inform them. What I’m calling the Substack method, where a breach is publicized via one easily-spoofed channel, and not on the platform itself.
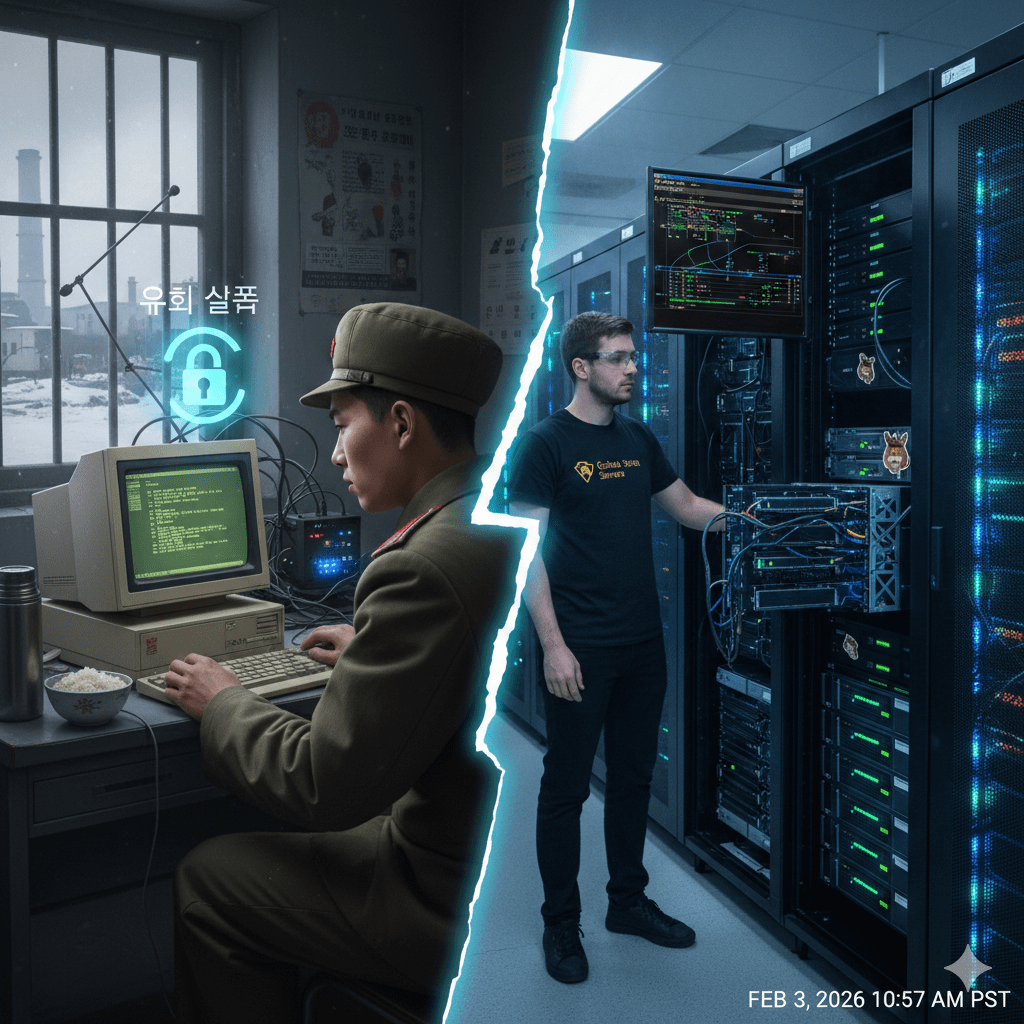
- Powerfully inform them. The KnowBe4 method, in which KnowBe4 confirmed on multiple platforms that a North Korean had successfully secured employment with the firm.
How will YOUR firm respond when you are breached?