I know that Bredemarket has pivoted away from full-time identity work in favor of part-time work with local businesses in Ontario, Eastvale, and other cities, but a recent local activity illustrated a possible identity issue that I’d like to explore here. So allow me this tangent; I’ll get back to my Ontario, California content marketing expert content later.
Identities and bus passes
Remember my trip to Eastvale yesterday? I had to use a bus to get there. And to do this, I bought a day pass.
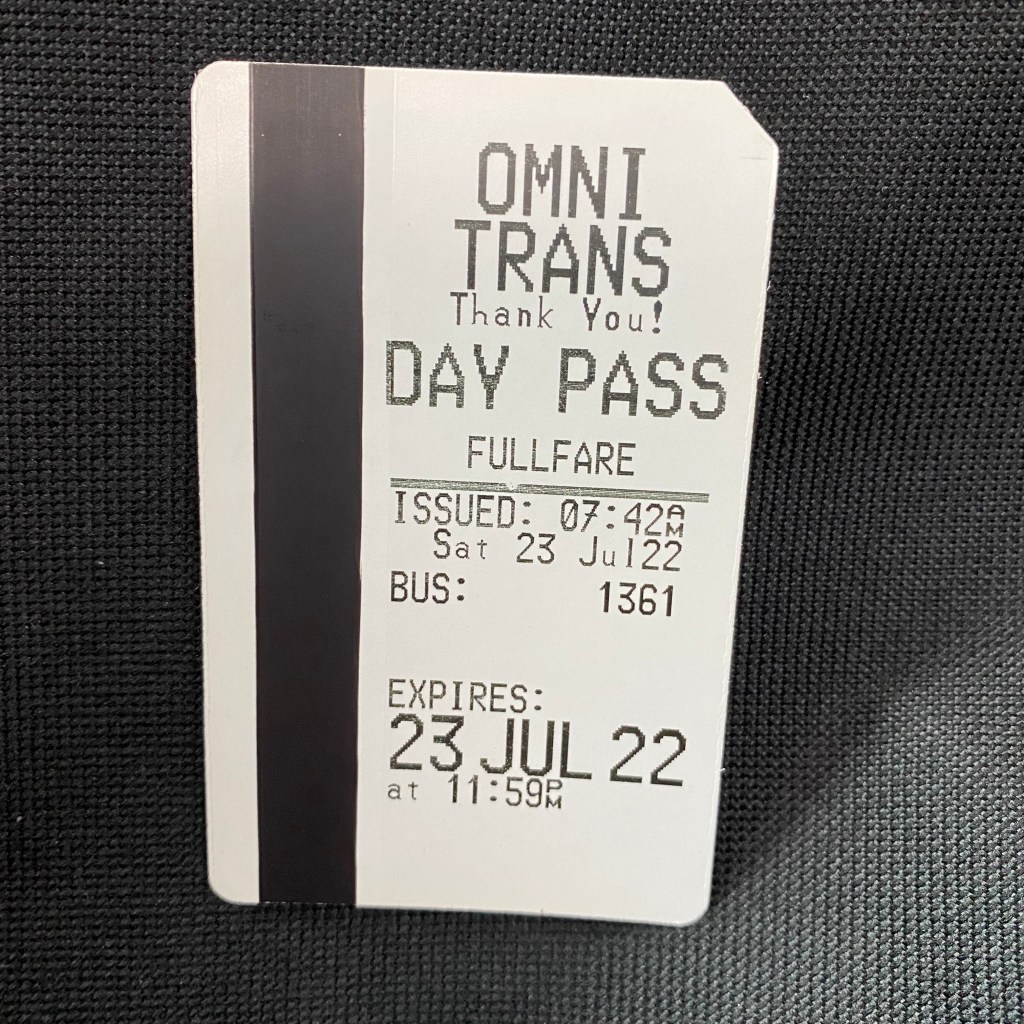
Now this is not the most robust proof of identity. As I recently noted in my JEBredCal blog (one of my other Google identities), it’s extremely easy for multiple people to use this day pass at different times during the day. Even the 7-day and 31-day passes, which must be signed and may be compared against an identity document, are not necessarily free from fraud.
However, this is not critical to Omnitrans, who would rather put up with a small amount of fraud than inconvenience its riders with multiple identity checks.
Identity proofing is more critical in some situations than it is in others.
From https://jebredcal.wordpress.com/2022/07/24/how-important-is-that-identity/.
Of course, if Omnitrans really wanted to, it could achieve the need for fraud prevention by using relatively frictionless forms of identity proofing. Rather than demaning to see a rider’s papers, Omnitrans could use passive methods to authenticate its riders. I won’t go into all the possible methods and their pros and cons here.
However, I would like to explore one possible identity proofing method to see if it would solve the Omnitrans pass use issue.
Returning to my sixth authentication factor
Can my self-proclaimed sixth factor of authentication provide a solution?
You’ll recall that many identity experts recognize five factors of authentication:
- Something you know.
- Something you are.
- Something you have.
- Something you do.
- Somewhere you are.
Well, because I felt like it, I proclaimed a sixth factor of authentication.
- Why?
I said, because I felt like it!
Whoops, “why?” is the sixth authentication factor. I still haven’t rendered it into the “somexxx you xxx” format yet.
Can Omnitrans use the “why?” factor to test the reasonableness that any particular trip is performed by the person who originally bought the pass?
Possibly.
Applying the “why?” question to bus boarding data
Assume the most challenging scenario, in which Omnitrans knows nothing about the person who purchases a 31-day pass. The person pays in cash and is wearing a face mask and sunglasses throughout the entire transaction. Therefore, the only identity information associated with the pass is the location where the pass was purchased, the date/time it was purchased, and some type of pass identification number. For this example, we’ll assume the pass number is 12345.
So Omnitrans really doesn’t know anything of importance about the holder of pass 12345…
…other than how it is used.
I’m making the assumption that Omnitrans logs information about every use of a pass. Since you don’t need to use your pass when you leave the bus, the only information available is when you board the bus.
So let’s look at some fake data.
| Date and Time | Bus | Location |
| Monday, July 25, 2022, 6:39 am | 87 | Euclid & Holt, Ontario |
| Monday, July 25, 2022, 6:35 pm | 87 | Amazon LGB3, Eastvale |
| Tuesday, July 26, 2022, 6:39 am | 87 | Euclid & Holt, Ontario |
| Tuesday, July 26, 2022, 6:35 pm | 87 | Amazon LGB3, Eastvale |
| Wednesday, July 27, 2022, 8:42 am | 87 | Euclid & Holt, Ontario |
| Wednesday, July 27, 2022, 6:35 pm | 87 | Amazon LGB3, Eastvale |
| Thursday, July 28, 2022, 6:39 am | 87 | Euclid & Holt, Ontario |
| Thursday, July 28, 2022, 6:35 pm | 87 | Amazon LGB3, Eastvale |
| Thursday, July 28, 2022, 7:20 pm | 61 | Plum & Holt, Ontario |
| Thursday July 28, 2022, 9:52 pm | 61 | Ontario Mills, Ontario |
| Friday, July 29, 2022, 6:39 am | 87 | Euclid & Holt, Ontario |
| Friday, July 29, 2022, 8:35 am | 87 | Amazon LGB3, Eastvale |
| Friday, July 29, 2022, 10:00 am | 66 | Vineyard & Foothill, Rancho Cucamonga |
| Friday, July 29, 2022, 11:26 am | 14 | Fontana Metrolink |
| Friday, July 29, 2022, 11:53 am | 82 | Fontana Metrolink |
| Friday, July 29, 2022, 12:08 pm | 66 | Fontana Metrolink |
Even if you are not familiar with California’s Inland Empire, you can probably classify these trips into the following categories:
- Trips that are probably legitimate.
- Trips that may or may not be legitimate.
- Trips that are probably fraudulent.
- Trips that are definitely fraudulent.
For the most part, you can’t know with certainty about the legitimacy of most of these trips. Here’s a story that fits the facts.
- Jack Jones starts his new job at Amazon on Monday, and works Monday and Tuesday with no incident. Jack overslept on Wednesday and was written up. He made sure to arrive at work on time Thursday, and at the end of the day he celebrated with a dinner at a restaurant in the Ontario Mills shopping center. After arriving at work on Friday, Sara Smith picked his pocket and took his pass, fleeing the scene an hour later and making her way to Fontana. She creates several clones of the bus pass and sells them at a discount before fleeing herself. Therefore, all trips beginning on Friday at 8:35 am are fraudulent.
But that might not be the true story. This one also fits the facts.
- Jack Jones starts his new job at Amazon on Monday, and works Monday and Tuesday with no incident. On Wednesday Jack calls in sick, but lets his housemate Bob Brown (who also works at Amazon) use his pass on Wednesday and Thursday. By Thursday evening, Jack is feeling better, retrieves his pass from his housemate, and goes to Ontario Mills for the evening. On Friday Jack goes to work and is fired. He boards the 87, misses his stop in Ontario, and stays on the bus until he reaches Rancho Cucamonga. Despondent, he decides to visit his friend in Fontana. However, his Fontana friend, Sara Smile, secretly created several clones of Jack’s bus pass and sells them at a discount. Therefore, the Wednesday trips, the Thursday day trips, and all Friday trips beginning at 11:26 am are fraudulent.
Or perhaps some other set of facts fit the data.
- It’s possible that the pass was stolen before it was ever used and all of the trips are fraudulent.
- Or perhaps every trip before arriving in Fontana is legitimate, but how can we tell which one (if any) of the three trips from Fontana was undertaken by the true passholder?
But the data that Omnitrans captured provides a way to challenge the pass holder for possibly fraudulent trips.
- If Omnitrans is really suspicious for some reason, it may choose to challenge every trip that didn’t take place at the “regular” times of 6:39 am or 6:35 pm. “Why are you boarding the 87 bus at this hour of the morning?” “Why are you boarding the 61 bus?”
- Or Omnitrans may assume that all of the trips are reasonable and don’t necessitate a challenge. Yes, someone can go to work late. Yes, someone can go to Ontario Mills for the evening. Well, all of them are reasonable until Friday at 11:53 am, when a passholder boards a bus at the same location where the same passholder supposedly departed at 11:26 am.
Now even if strict identity checks are used with the “why?” statement, the data alone can’t detect all fraud. If Jack Jones and Bob Brown both work the day shift at Amazon, but on alternate days, how can Omnitrans detect the days when Jack Jones leaves Ontario at 6:39 am, vs. the days when Bob Brown leaves Ontario at 6:39 am?
Again, no identity proofing method is 100% foolproof.
But the “why?” question may detect some forms of fraud.
Or are there really only five factors of authentication after all?
Now I’ll grant that “why?” might not be a sixth factor of authentication at all, but may fall under the existing “something you do” category. This factor is normally reserved for gestures or touches. For example, some facial liveness detection methods require you to move your head up, down, right, or left on command to prove that you are a real person. But you could probably classify boarding a bus as “something you do.”
Anyway, thank you for engaging my tangent. If I can think of a “why?” example that doesn’t involve something you do, I’ll post it here. That will help me in my hopeful (?) quest to become the inventor of the sixth factor of authentication.
What about the businesses in cities where my bus trips took place?
But back to the businesses in Ontario, Eastvale, Rancho Cucamonga, Fontana, and other cities: need some content help? I can create esoteric long-winded content like this, or (what you probably want) more concise, customer-focused content that conveys your important message. My regular work includes case studies, white papers, proposal services, and other types of content. If you need someone to help you create this content:
- Send me an email at john.bredehoft@bredemarket.com.
- Or go to calendly.com/bredemarket to book a meeting with me.
- Or go to bredemarket.com/contact/ to use my contact form.








