How many people should use a SaaS service? If your answer is “only one,” you don’t need to read this post.
Last month I discussed a particular use case in which AI-based non-person entities (NPEs) were bound to the identities of carbon-based life forms. My post “Identity-Bound Non-Person Entities” reviewed the partnership between Anonybit and SmartUp.
This binding doesn’t need artificial intelligence to work. The NPE may be something as simple as a service.
But how many people can be bound to an NPE?
A company and its service
There is a very large technology company; I won’t reveal the company name, but its initials are HP. And this very large company provides a service; I won’t reveal the service name, but it instantly provides ink for the company’s printers…
Never mind. It turns out that I already discussed HP Instant Ink (Ink as a Service) in the Bredemarket blog before. Plus, the company providing IaaS is no longer known as “the Hewlett-Packard Company,” but as “HP Inc.” So much for my attempts at obfuscation.
The 1:1 binding between me and Instant Ink
Anyway, we did sign up for Instant Ink when we purchased a new printer. Specifically, my HP account was registered as the owner of our Instant Ink account.
(Those of you with a keen eye can already see where this is going.)
As part of the Instant Ink service that we purchased, I can obtain two things:
1. The status of Instant Ink shipments to us
Not that these shipments are all that fast.
So far we have encountered two instances in which we ran out of ink before the new Instant Ink shipment arrived.
And when you put a regular ink cartridge into the printer while waiting for the Instant Ink shipment, HP sends a nasty gram stating that I put the wrong ink in the printer, and to put Instant Ink in the printer right now.
Um, my Instant Ink is in Pennsylvania, and it will take 10 days to reach California. What am I supposed to do, fly to Pennsylvania and get it?
2. HP support
For our printer, I can obtain support from HP. I will have more to say about HP support later.
First person…or people
Do all of you see the issue now? If not, let me spell it out.
I am married, and my wife and I bought the printer together. But she has no access to shipment tracking or support; only I do.
Actually, I must confess that I gave her my HP login and password. So she has access to the shipment tracking information. But since her name is not John, we assumed that HP would never talk to her about the Instant Ink service that we purchased.
There is something in the (so-called) HP Smart App that allows me to “invite” someone to the printer. But when I tried to “invite” my wife, HP briefly flashed a message saying that I could not invite my wife because she already had an HP personal account.
I need support
By this time I had piled up 3 support requests for HP:
- How can I get new Instant Ink before my old Instant Ink runs out?
- How can my wife see information on our Instant Ink service?
- Plus there’s a third one regarding multiple HP accounts that I won’t get into here.
I decided to tackle the second support request first. So I found the support page, started a gust, and got a ticket number.
The first support chat
I was routed to a printer specialist, who informed me that they couldn’t help me and routed me to an Instant Ink specialist.
The Instant Ink person asked for the error code that appeared when I tried to “invite” my wife. I explained that I didn’t know because it disappeared so quickly.
So I tried to invite my wife again, pointing my smartphone camera at the laptop screen so that I could take a picture of the error code the…um…instant that it appeared.
I successfully took the picture, and there was no error code. Just a message saying that I couldn’t invite my wife because she already had an HP personal account. And to contact support.
The Instant Ink specialist instructed me to click on a link, then closed the support ticket.
I clicked on the link…and was asked to create a new support ticket.
The second support chat
I was routed to a printer specialist, who informed me that they couldn’t help me and routed me to an Instant Ink specialist.
(Yes, there’s a lot of repetition in this post.)
By this time I tried to boil my request down to a simple question: how can my wife see Instant Ink shipment status and request support on her own?
The Instant Ink specialist went quiet for a while, and finally—over an hour after I started the initial support chat—provided the solution to my problem.
Give my wife my HP login and password. And sure, she’ll have no problem contacting support, even though I’m the named user.
Suffice it to say that I was not pleased.
A systemic problem
But to be fair, none of the 4 support people I talked to could have solved my problem.
Because HP has made the underlying assumption that its Instant Ink service can only be managed by one person, not two.
And HP is not alone in this. There are multiple services that assume single person management. This affects married couples often, where one spouse is the named user for a service but knows nothing about it because spouse 2 handles it.
This results in a number of conversations like this:
SERVICE: John?
WIFE: No, this is his wife.
SERVICE: I need John’s authorization to continue.
WIFE: (carries phone to me in the Bredemarket world headquarters) Amazing and wonderful husband, could you authorize me to discuss our account?
(Some portions of this conversation may have been fictionalized.)
ME: Hello, this is John.
SERVICE: John, what is your date of birth?
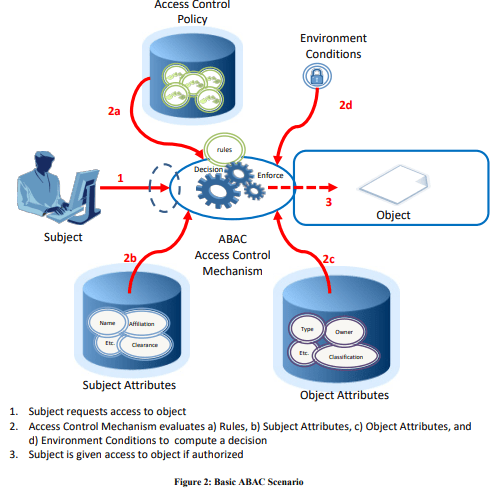
This is not a technology issue, but an organizational issue. Except where laws (such as HIPAA) regulate this, an organization should allow multiple people to be assigned to a service or other NPE.
It would make my—I mean our lives easier.