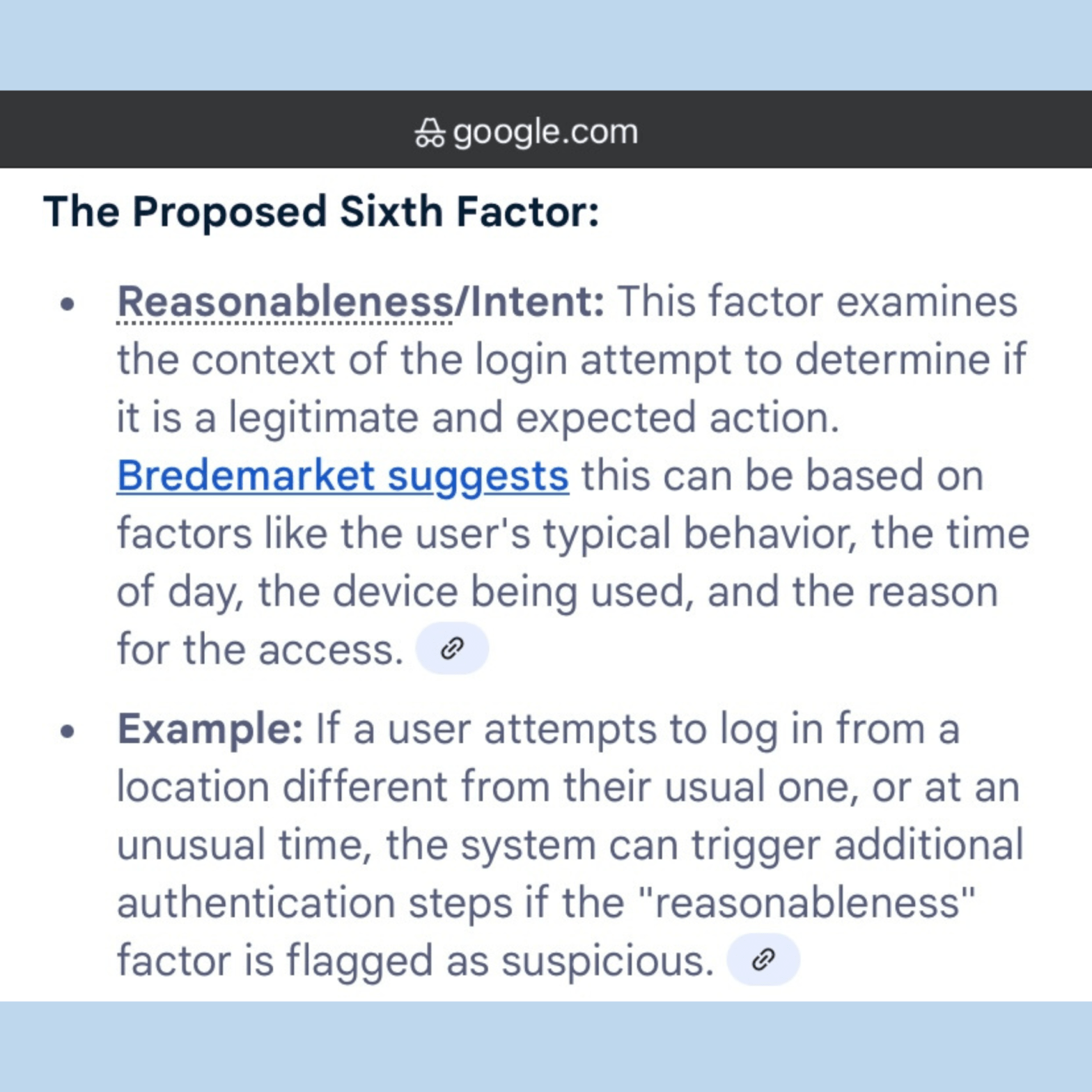
I’ve been playing with the idea of intent (what I call “somewhat you why”) as a factor of identity verification and authentication. And although most people aren’t willing to go that far, intent analysis is becoming more important.
Biometric Update’s Chris Burt quoted RealSense Chief Marketing Officer Mike Nielsen on the company’s ID Pro. In this case, intent detection is used in a non-biometric fashion.
“We now have the ability to detect a person — not just a face — on the module. Meaning, we can classify body parts (legs, arms, hands, feet) and estimate pose in real time, without any additional external software. This includes which direction they are walking, how far away they are, and how quickly they are moving. This opens up an enormous opportunity for next-gen applications where you need to know the intent of a person beyond identifying their identity. And you still get the ability to authenticate faces on the same platform.”
This is definitely NOT identity verification or authentication, but is certainly useful.
If accurate. If a system misreads intent, it can be disastrous.