How to remind everyone you’re Chinese-owned:
Time your January 19 “go dark” to happen before 11pm EST on January 18.
Identity/biometrics/technology marketing and writing services

How to remind everyone you’re Chinese-owned:
Time your January 19 “go dark” to happen before 11pm EST on January 18.

(Imagen 3)
Curiouser and curiouser. A recap:
The chatter in recent days has speculated that Elon Musk may buy TikTok, or that Mark Zuckerberg’s Meta may buy TikTok. (Both men were slated to attend Trump’s inauguration, although that may have changed since the festivities have moved indoors.)
CNBC reports one more interested party—Perplexity AI:
“Perplexity AI officially made a play for TikTok on Saturday, submitting a bid to its parent company, ByteDance, to create a new merged entity combining Perplexity, TikTok U.S. and new capital partners, CNBC has learned.”
What’s next: Procter & Gamble?

TikTok may still go dark Sunday…but (apologies to Tony Campolo) Monday’s coming!
“President-elect Donald Trump told NBC News’ “Meet the Press” moderator Kristen Welker in a phone interview Saturday that he will “most likely” give TikTok a 90-day reprieve from a potential ban in the U.S. after he takes office Monday.
“Trump said he hadn’t made a final decision but was considering a 90-day extension of the Sunday deadline for TikTok’s China-based parent company to sell to a non-Chinese-buyer or face a U.S. ban.”
Trump’s announced intention to possibly grant ByteDance a 90 day extension to sell TikTok means nothing until something actually happens. But it’s somewhat more likely than Liz Cheney in jail. Or the post-inauguration Trump tariffs.
And Trump (or, for that matter, Biden) has the power to grant such an extension.
“A 90-day extension under specific conditions is explicitly allowed for in the bipartisan law passed last year.”
But think about it.

In the political world, deadlines are but a dream.

(Imagen 3)
In my country, the issuance of driver’s licenses is performed at the state level, not the national level. This has two ramifications.
The U.S. government wanted to tighten down on identification cards to stop terrorists from hijacking planes and crashing them into buildings.
But it couldn’t.
When it told the states to issue “REAL ID” cards by 2008, the states said they wouldn’t be told what to do.
Today all of them support REAL ID cards as an option, but use of REAL IDs for federal functions such as plane travel won’t be enforced until 2027…if then.
For years there has been a move to replace physical driver’s licenses with mobile driver’s licenses, or mDLs.
Again, in my country this has been pursued in a piecemeal basis on the state level. Louisiana has its own mDL, with a separate one in Oklahoma, one in California, others in other states, and none in other states. And one state (Florida) that had one, then didn’t have one.
Some mDLs are in custom wallets, while others are or are not in wallets from Apple, Google, and Samsung.
Oh, and don’t try using your Louisiana mDL to buy a beer in Arkansas.
Things are different in other countries. Amit Alagh shared a BBC article with me.
“Digital driving licences are to be introduced in the UK as the government looks to use technology to ‘transform public services’…. The new digital licences will be introduced later this year….”
Throughout the entire United Kingdom, including Scotland and Northern Ireland, apparently.
In one fell swoop. Entire country done.

music is Devo’s “Booji Boy’s Funeral.”
Originally posted at https://www.instagram.com/reel/DE9zSw7pZI2/?igsh=NTc4MTIwNjQ2YQ==
When I wasn’t TikTok tracking tonight, I was trying to figure out how to deal with Instagram’s grid dimension change from square to 4×5.
I guess this change was announced long ago, but I didn’t get (or ignored) the memo.
I’m not going to worry about my grid, except for my first three pinned images. And Elle (Instagram/Threads inkwell.elle) has a fix for that:
“Click on the post, 3 dots, adjust preview and fit… it’s the best workaround for the new layout but you have to do it on each post individually 😅”
When I edited my three pinned images, I also changed the background from white to black.

Then I experimented with Canva (my primary image and video tool these days) and created an Instagram image that was 4×5 rather than square.
Nice neat grids are overrated anyway; I like mine messy. But I also like it readable.
Even though it appears that the U.S. government will not shut TikTok down in my country on Sunday, I wondered if TikTok would shut itself down, just to grab attention or make a point.
According to the BBC, TikTok is threatening to do just that.
“(TikTok) said ‘both the Biden White House and the Department of Justice have failed to provide the necessary clarity and assurance to the service providers that are integral to maintaining TikTok’s availability’.
“It said unless the government immediately stepped in to assure the video app it would not be punished for violating the looming ban, it would be ‘forced to go dark on January 19’.”
But if President Biden (who remains President until Monday) provided such an explicit assurance, he may be in violation of both the bipartisan Protecting Americans from Foreign Adversary Controlled Applications Act and the Supreme Court ruling (PDF).
To be continued.

(Imagen 3)
Proposal professionals are familiar with this question: do you write the executive summary first, or last?
I recently struggled with this, but in a non-proposal project—specifically, for an online article I was writing for a Bredemarket client. I had already asked my seven questions, so I had a high-level idea of the points I wanted to make. But I intentionally started writing the rest of the online article, and put some filler text at the beginning:
“*** Introduction Goes Here”
Those who have worked with me on content, proposal, and analysis projects know how much I love my three asterisks, and other things to flag incomplete text.
But why did I delay writing the introduction to the end? Because of one important difference between proposals and online articles.
Because of this, the opening words of an article can be very important. And the right words need to be there.
So I saved that writing exercise for later.

(Imagen 3)
I’m not going to go into specifics, but a few of you know what I’m talking about.
What happens when an industry association assembles a governing board from senior executives at its member companies…
…but two of those senior executives were let go by the companies in question?
More details…elsewhere…
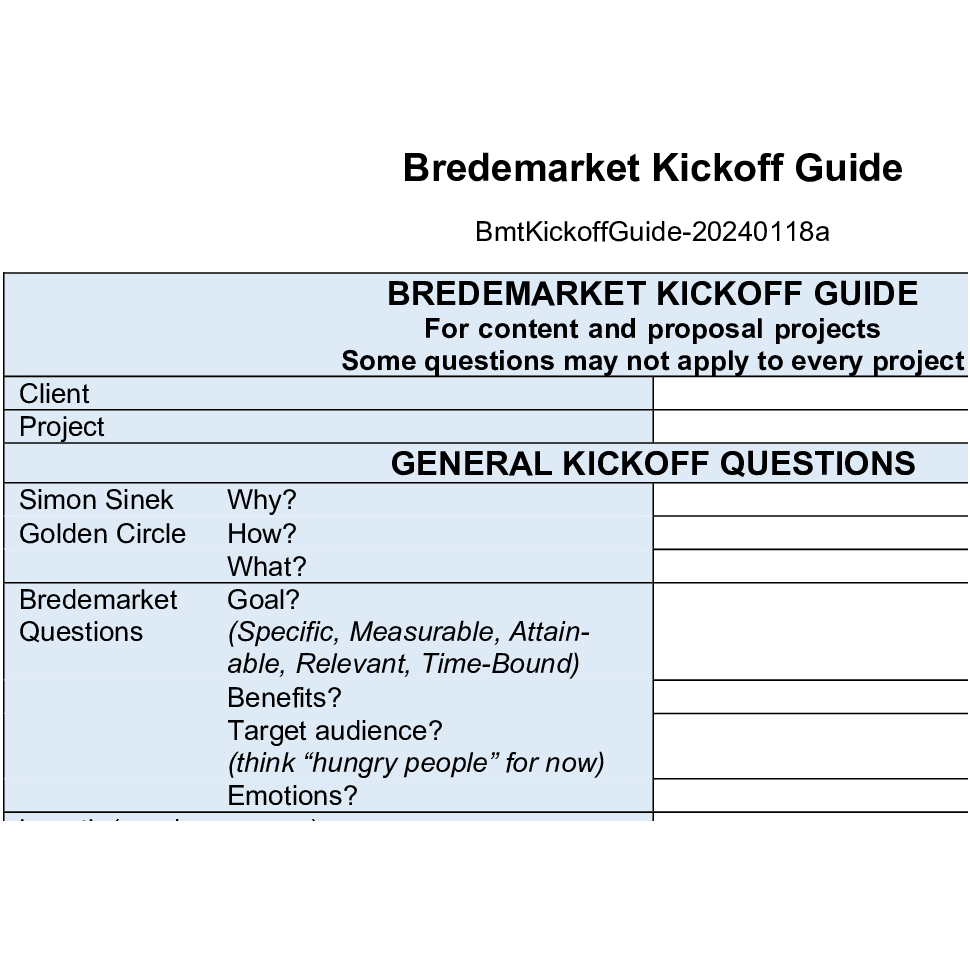
Luna Marketing Services asked us on Instagram when we last went over our current processes.
My answer: January 18, 2024.
The illustration shows just one part of one of my processes. I don’t share the rest of this particular process, but it governs creation of most of my “CPA” materials.
In fact, I am about to start a short writing project for one of my clients, and I will start by asking these seven questions.
But not in Word. In the client’s Jira.
Don’t forget that processes require flexibility. Don’t complete processes for the sake of completing processes.