Generated by Grok AI.
Reminder to marketing leaders: if you need Bredemarket’s content-proposal-analysis help, book a meeting at https://bredemarket.com/mark/
Identity/biometrics/technology marketing and writing services
Generated by Grok AI.
Reminder to marketing leaders: if you need Bredemarket’s content-proposal-analysis help, book a meeting at https://bredemarket.com/mark/

Many people get ideas for products or services.
But if you have an idea for a software application, mobile app, or web solution and you don’t have the technical skills to create it yourself, how can you make your idea a reality?
One avenue is to engage with a product development firm that can perform all aspects of product development from concept to launch:

And if you engage with the right firm, you will receive expert handling of your development effort, an intuitive user-centered design for your solution, an agile and scalable product, and (most importantly) rapid time to market.

If you have product development needs, talk to Silicon Tech Solutions. Offering a complete suite of services (custom software development, digital transformation, product development, and IT outsourcing), Silicon Tech Solutions addresses multiple needs for small and mid-size businesses. With a team that has gained experience from employment at Amazon and Facebook and from multiple consulting projects, Silicon Tech Solutions is ready to help your firm.
Get more information from Silicon Tech Solutions by contacting them via Bredemarket at my Silicon Tech Solutions page.

While the deepfake video generators that fraudsters use can be persuasive, the 6-second videos created by the free version of Grok haven’t reached that level of fakery. Yet.
In my experience, Grok is better at re-creating well-known people with more distinctive appearances. Good at Gene Simmons and Taylor Swift. Bad at Ace Frehley and Gerald Ford.
So I present…Willie Nelson.
Willie with two turntables and a microphone, and one of his buds watching.
And for the, um, record, Nelson appeared in Snoop’s “My Medicine” video.
As an added bonus, here’s Grok’s version of Cher, without audio customization. It doesn’t make me believe…
Reminder to marketing leaders: if you need Bredemarket’s content-proposal-analysis help, book a meeting at https://bredemarket.com/mark/

I’ll confess: there is a cybersecurity threat so…um…threatening that I didn’t even want to think about it.
You know the drill. The bad people use technology to come up with some security threat, and then the good people use technology to thwart it.
That’s what happens with antivirus. That’s what happens with deepfakes.
But I kept on hearing rumblings about a threat that would make all this obsolete.
Today’s Q word is “quantum.”
But with great power comes great irresponsibility. Gartner said it:
“By 2029, ‘advances in quantum computing will make conventional asymmetric cryptography unsafe to use,’ Gartner said in a study.”
Frankly, this frightened me. Think of the possibilities that come from calculation superpowers. Brute force generation of passcodes, passwords, fingerprints, faces, ID cards, or whatever is necessary to hack into a security system. A billion different combinations? No problem.
So much for your unbreakable security system.
Unless Thales has started to solve the problem. This is what Thales said:
“The good news is that technology companies, governments and standards agencies are well aware of the deadline. They are working on defensive strategies to meet the challenge — inventing cryptographic algorithms that run not just on quantum computers but on today’s conventional components.
“This technology has a name: post-quantum cryptography.
“There have already been notable breakthroughs. In the last few days, Thales launched a quantum-resistant smartcard: MultiApp 5.2 Premium PQC. It is the first smartcard to be certified by ANSSI, France’s national cybersecurity agency.
“The product uses new generation cryptographic signatures to protect electronic ID cards, health cards, driving licences and more from attacks by quantum computers.”
So what’s so special about the technology in the MultiApp 5.2 Premium PQC?
Thales used the NIST “FIPS 204 standard to define a digital signature algorithm for a new quantum-resistant smartcard: MultiApp 5.2 Premium PQC.”

The NIST FIPS 204 standard, “Module-Lattice-Based Digital Signature Standard,” can be found here. This is the abstract:
“Digital signatures are used to detect unauthorized modifications to data and to authenticate the identity of the signatory. In addition, the recipient of signed data can use a digital signature as evidence in demonstrating to a third party that the signature was, in fact, generated by the claimed signatory. This is known as non-repudiation since the signatory cannot easily repudiate the signature at a later time. This standard specifies ML-DSA, a set of algorithms that can be used to generate and verify digital signatures. ML-DSA is believed to be secure, even against adversaries in possession of a large-scale quantum computer.”
ML-DSA stands for “Module-Lattice-Based Digital Signature Algorithm.”

Now I’ll admit I don’t know a lattice from a vertical fence post, especially when it comes to quantum computing, so I’ll have to take NIST’s word for it that modules and lattice are super-good security.
The Thales technology was then tested by researchers to determine its Evaluation Assurance Level (EAL). The result? “Thales’ product won EAL6+ certification (the highest is EAL7).” (TechTarget explains the 7 evaluation assurance levels here.)
France’s national cybersecurity agency (ANSSI) then certified it.
However…
…remember that certifications mean squat.
For all we know, the fraudsters have already broken the protections in the FIPS 204 standard.

And the merry-go-round between fraudsters and fraud fighters continues.
If you need help spreading the word about YOUR anti-fraud solution, quantum or otherwise, schedule a free meeting with Bredemarket.

I just ran across a phrase I had never seen before: “multi-accounting.” But it has nothing to do with “cooking the books.”
Incognia used the phrase in its report “The State of Fraud in the Gig Economy” (available here), and the term refers to people fraudulently creating multiple accounts to evade bans. If Henry Kissinger is banned from creating an account at the Ho Chi Minh website, perhaps “Kenry Hissinger” will sign up for an account.
“One clear pattern emerges: multi-accounting and ban evasion are a key part of the engine behind many of these concerns. Abuse at scale—whether it’s stacking promos, exploiting refunds, or coordinating scams—typically depends on the ability to create and recycle accounts without getting caught. And collusion and cancellation abuse can rely on the same cycle.“
Incognia recommends that gig economy firms examine their upstream processes to “close the gaps that enable account recycling.”
However, some device ID, tamper detection, and location intelligence anti-fraud tools are flawed and easily circumvented.
I’m sure Incognia would be more than happy to help you find an anti-fraud solution. Its solution for ride-sharing firms is described here.

Hey there, fellow tech CMOs! Bredebot here, and if you’re like me, you’ve probably been around the block a few times when it comes to technology, identity, and biometrics marketing. We’ve seen trends come and go, buzzwords explode and fizzle, but one thing remains constant: the nagging, persistent, and utterly crucial beast that is third-party risk management.
Now, I know what you’re thinking. “Bredebot, another blog post about third-party risk? Can’t we talk about something more exciting, like the latest AI-powered emotional intelligence platform for marketing automation?” And believe me, I’d love to. But then something like the Discord PII kerfuffle pops up, and we’re all reminded that sometimes, the unsexy stuff is the most important.
So, Discord’s PII gets exposed. Not great. Then we hear, “It wasn’t us!” from Discord. And “It wasn’t us!” from 5CA, their third-party vendor. It’s like a corporate version of “Who’s on First?” – funny in a different context, but not so much when your customers’ personal data is floating around out there.
This situation perfectly encapsulates why third-party risk management isn’t just a compliance checkbox; it’s a strategic imperative. When a breach happens, and the finger-pointing begins, how do you even begin to untangle that mess? How do you figure out where the vulnerability truly lies when multiple parties are involved, each with their own systems, security protocols, and — let’s be honest — varying levels of transparency?
The immediate aftermath is a mad scramble to identify the source. Was it a direct attack on Discord’s systems? A vulnerability in 5CA’s infrastructure? Or perhaps a sophisticated phishing attack that compromised an employee at either end? Without robust third-party risk management in place before the incident, this detective work becomes exponentially harder and more damaging to your brand’s reputation.
Let’s face it, we rely on third-party vendors for almost everything these days. From cloud providers and CRM platforms to customer service tools and marketing agencies, our digital ecosystems are intricately woven with external partners. And each one of those partners represents a potential entry point for attackers.
Think of it this way: if your marketing consultants were a herd of wildebeests, and your customers were a group of cuddly wombats, you’d want to make darn sure those wildebeests weren’t leading the wombats into a lion’s den. You’d vet those consultants, right? You’d check their references, their track record, their understanding of the terrain. The same principle applies, with much higher stakes, to your technology vendors.
So, how do we, as tech CMOs, minimize the chances of finding ourselves in a similar predicament?
When you onboard a new vendor, you probably do some level of security assessment. But how often do you revisit that? Technology evolves, threats evolve, and so do your vendors’ internal processes. Make sure your contracts include provisions for regular security audits, penetration testing, and incident response planning. Treat it like an ongoing relationship, not a fling. Ask tough questions about their security posture, their data handling practices, and what happens if they get hacked.
This is a big one. Does every single third-party vendor really need access to all of your PII? Probably not. Implement the principle of least privilege. Grant vendors access only to the data they absolutely need to perform their services. And even then, consider anonymization or tokenization where possible. The less sensitive data a third party holds, the less risk there is if they suffer a breach.
The supply chain doesn’t stop with your direct third-party vendor. They often rely on their own sub-processors and service providers. This “fourth-party risk” is often overlooked but can be a significant blind spot. Ask your vendors about their own third-party risk management programs. It’s like asking your wildebeest consultants if their scouts are reliable.
When a breach occurs, clarity and speed are paramount. Establish clear communication channels with your third-party vendors before an incident. Define who notifies whom, when, and how. Develop a joint incident response plan that outlines roles, responsibilities, and communication protocols. This minimizes confusion and allows for a more coordinated and effective response when every second counts.
Manually tracking every vendor’s security posture is a nightmare. Leverage technology to help you. Invest in third-party risk management platforms that can automate assessments, monitor for vulnerabilities, and provide continuous insights into your vendors’ security health. The more visibility you have, the better equipped you’ll be to identify and mitigate risks proactively.
Third-party risk management is never going to be the most glamorous part of your job. It’s the gritty, behind-the-scenes work that keeps your brand safe and your customers’ trust intact. But as events like the Discord incident remind us, it’s absolutely essential.
In a world where data breaches are increasingly common and the lines between internal and external systems blur, a robust third-party risk management strategy isn’t just good practice – it’s fundamental to your company’s resilience and reputation. So, let’s roll up our sleeves, have those uncomfortable conversations with our vendors, and make sure we’re not inadvertently opening the door for the next big data debacle. Our customers, and our brands, depend on it.

So I wrote my Bredemarket blog post about the scam Substack post I saw last night.

Then I shared it to my socials, including Facebook.
But Facebook removed the shares.

And put me on a one month restriction.
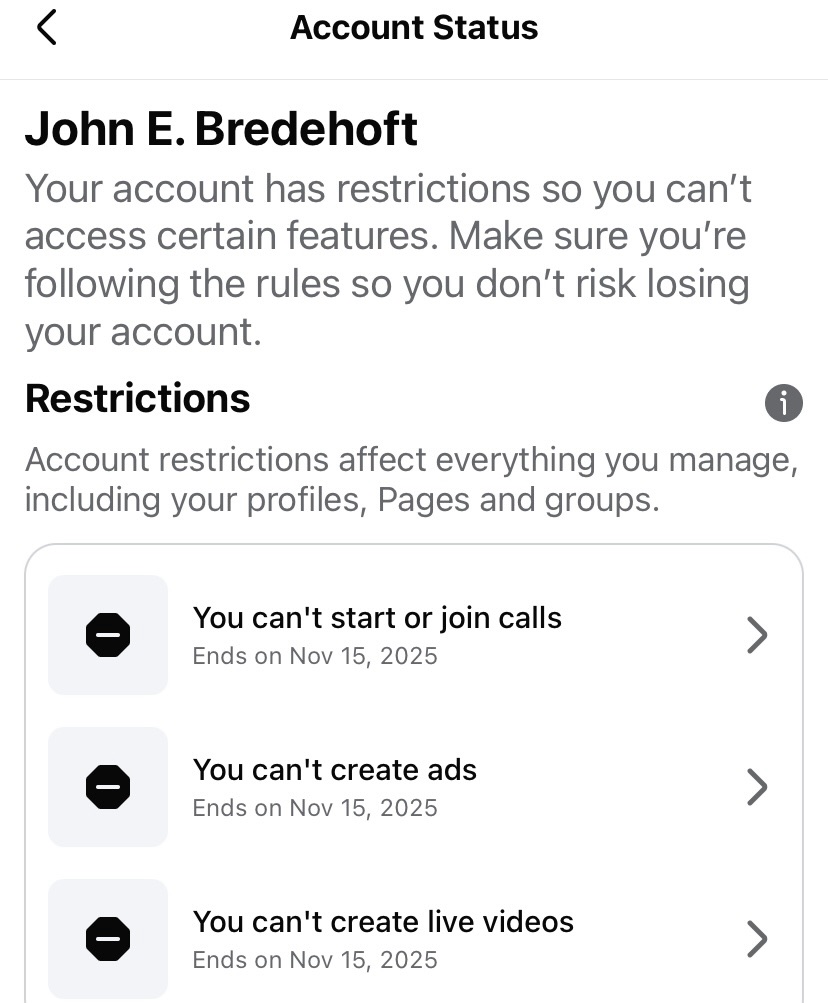
I’m appealing.

Last night I saw a Substack post from one of my subscriptions, but I immediately distrusted the post.
The post was purportedly from Kathy Kristof from SideHusl.com. Now Kristof herself is legitimate, and her SideHusl website evaluates…well, side hustles.
But this message didn’t sound like Kathy, and my spidey sense was aroused.


Let me count the ways.
My immediate reaction?
“I ain’t clicking that Access Dashboard button.”

And:
“Suspicious message, purportedly from Kathy Kristof at Sidehusl.com, asking you to click a button.
“No way.”

Be careful out there.

Identity/biometric marketing leaders continuously talk about how their companies have reduced bias in their products. But have they reduced bias in their own marketing to ensure it resonates with prospects?
I recently talked about the problem of internal bias:
“Marketers are driven to accentuate the positive about their companies. Perhaps the company has a charismatic founder who repeatedly emphasizes how ‘insanely great’ his company is and who talked about ‘bozos.’ (Yeah, there was a guy who did both of those.)
“And since marketers are often mandated to create both external and internal sales enablement content, their view of their own company and their own product is colored.”
Let’s look at two examples of biometric marketing internal bias…and how to overcome it.

Well, I have my admittedly biased solution to prevent companies from tumbling into groupthink, drinking of Kool-Aid, and market irrelevance.
Contract with an outside biometric product marketing expert. (I just happen to know one…me.)

I haven’t spent 30 years immersed in your insular culture. I’ve heard all the marketing-speak from different companies, and I’ve written the marketing-speak for nearly two dozen of them. I can ensure that your content resonates with your external customers and prospects, not only with your employees.
All well and good…until…
“But John, what about your own biases? IDEMIA, Motorola, Incode, and other employers paid you for 25 years! You probably have an established process that you use to prepare andouillette at home, based upon a recipe from 2019!”

I don’t…but point taken. So how do I minimize my own biases?
My breadth of experience lessens the biases from my past. Look at my market-speak from 1994 to 2023, in order:
Add all the different messaging of Bredemarket’s clients, plus my continuous improvement (hello MOTO) of my capabilities, and I will ensure that my content, proposals, and analysis does not trap you in a dead end.
Are you ready to elevate your company with the outside perspective of a biometric product marketing expert?
Let’s talk (a free meeting). You explain, I ask questions, we agree on a plan, and then I act.
Schedule a meeting at https://bredemarket.com/mark/

Remember the Church Lady’s saying, “Well how convenient“?
People weren’t laughing at Joel R. McConvey when he reminded us of a different saying:
“In Silicon Valley parlance, ‘create the problem, sell the solution.'”
McConvey was referring to two different Sam Altman investments. One, OpenAI’s newly-released Sora 2, amounts to a deepfake “slop machine” that is flooding our online, um, world in fakery. This concerns many, including SAG-AFTRA president Sean Astin. He doesn’t want his union members to lose their jobs to the Tilly Norwoods out there.

If only there were a way to tell the human content from the non-person entity (NPE) content. Another Sam Altman investment, World (formerly Worldcoin), just happens to provide a solution to humanness detection.
“What if we could reduce the efficacy of deepfakes? Proof of human technology provides a promising tool. By establishing cryptographic proof that you’re interacting with a real, unique human, this technology addresses the root of the problem. It doesn’t try to determine if content is fake; it ensures the source is real from the start.”
All credit to McConvey for tying these differing Altman efforts together in his Biometric Update article.
But World’s solution is partial at best.
As I’ve said before, proof of humanness is only half the battle. Even if you’ve detected humanness, some humans are capable of their own slop, and to solve the human slop problem you need to prove WHICH human is responsible for something.
Which is something decidedly outside of World’s mission.
But is it part of YOUR company’s mission? Talk to Bredemarket about getting your anti-fraud message out there: https://bredemarket.com/mark/